Vapedance.com is a deceptive website that tricks unsuspecting online shoppers with unbelievably discounted rates on their products.
The truth behind this deception is that they fail to deliver the goods, leaving numerous customers with empty hands even after making purchases.
Although there are instances where buyers do receive packages, the items are frequently fake or of such inferior quality that they scarcely resemble the promised merchandise.
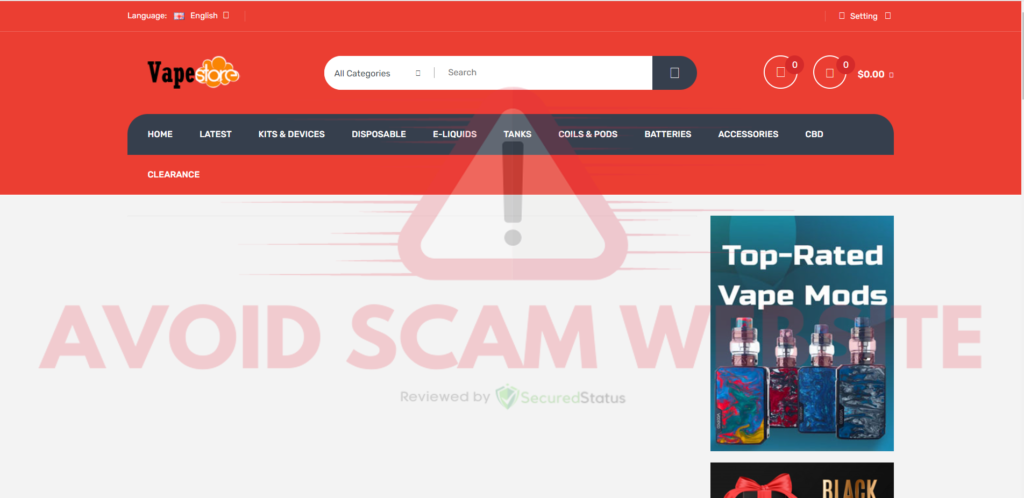
After conducting a thorough examination of the Vapedance.com online store, it is abundantly clear that the evidence leads to one undeniable conclusion: it is undoubtedly a website made to scam people of their hard-earned money.
However, before we delve into the red flags that categorize Vapedance.com as a fraudulent website, we will also provide ways to safeguard yourself if you have interacted with the aforementioned site.
Reasons why Vapedance.com is not safe to visit
Even though these malicious websites disguised as online stores are to blame for huge financial losses, many people fail to acknowledge the fact that the website in question was created by cybercriminals to steal personal information and launch malware attacks.
Because we have previously determined that Vapedance.com is an unsafe website that intends to cause harm to its purchasers, we believe that it is only fair to explain why this is the case.
The domain Vapedance.com was only registered recently
Domain name registration involves obtaining and utilizing a specific name for a designated period, typically a year. Once a domain name is registered, all its associated details, crucially including its creation date, are made publicly accessible.
As of the current date, a quick inquiry into the domain name "Vapedance.com" through registrar databases like Whois reveals that the name is relatively new, having been recently created.
By checking the domain "Vapedance.com" in registrar databases like Whois, it becomes evident that the name has only been created/updated recently as of the time of writing.
What does this mean?
Based on the available data, it appears that Vapedance.com is a recently created website, having been in existence for only a few days to a few weeks at the time of your visit.
We should note that such newly established websites are often associated with heightened risks of malware and viruses.
This in itself judges the credibility of the website and should already serve as a red flag to avoid the website at all costs.
We believe that these malicious sites have a relatively short lifespan, typically ranging from a few weeks to a few months.
Not to mention, when their harmful activities come to light and they are labeled as such, the cybercriminals responsible for creating these deceptive stores tend to abandon the current site and swiftly create a new one under a different name.
When encountering recently registered domains, we advise users to be as careful as possible as they may pose an increased risk of malicious activities, such as the distribution of malware and viruses.
They use stolen images in their malicious website
Malicious websites posing as online stores such as Vapedance.com probably lack the means to feature authentic product placement images due to their lack of actual inventory.
That is why they might resort to generating AI-generated images or, more commonly, using stock images or product photos sourced from legitimate websites.
To verify the legitimacy of an online store, take a few product placement image addresses from the website and paste them into reverse image search tools like Tineye and Duplichecker.
This will help determine if the images have been used elsewhere online, potentially indicating a malicious website posing as an e-commerce store.
Large discounts that are too good to be true
As the saying goes, "If it sounds too good to be true, it probably is." This statement holds, especially when dealing with online stores.
Large discounts often serve as bait, luring unsuspecting users into purchasing counterfeit items or, worse, receiving nothing at all in return for their hard-earned money.
We strongly advise buyers to exercise caution and refrain from placing trust in these seemingly irresistible offers, as they are often designed to trick online buyers into giving their sensitive data to cybercriminals which they can later on use to target users with phishing emails that are attached with malware and viruses.
If you genuinely seek to find products at a lower price, we suggest considering waiting for genuine sales events from legitimate stores or waiting for special occasions like Black Friday, where big discounts can be found.
Legitimate ways to save money through discounts exist, but websites like Vapedance.com are not among them; such sites can lead to financial loss and disappointment.
In conclusion, the analyses conducted have raised numerous red flags, strongly indicating that it is advisable to steer clear of this harmful website.
Potential harm that Vapedance.com can cause
Vapedance.com makes use of several deceitful strategies to take advantage of internet users who are unaware of the intentions behind their visit to the website.
Although collecting money from users by pretending to be an online store is the most obvious approach, this is only the tip of the iceberg regarding malicious activity.
We will also provide solutions and preventive measures to help you safeguard yourself against these harmful effects.
Cybercriminals can steal your credit card via Vapedance.com
When users reach the checkout stage within these malicious websites, they encounter a non-transparent payment system that does not conceal the details of the card information entered.
This is why they only allow credit/debit cards as a payment method since other options such as PayPal cannot be accessed by hackers due to two-factor authentication and overall security.
By obtaining valid credit card numbers, expiry dates, and CVNs, cybercriminals can expand their scheme further. With this acquired card information, they can later proceed to make exorbitant purchases with the user's card.
On the other hand, the victim is left with an unexpectedly high credit card bill for products they never ordered or received.
Solution: Call your bank for a refund and to stop transactions
One of the most important things to do after purchasing from Vapedance.com is to contact the bank that issues your credit card right away.
Tell them about the fraudulent purchase and give them information about it, including the precise product(s) you bought and where its source of purchase is.
This is accomplished through the use of a chargeback, a consumer safeguard that enables you to dispute a transaction and request that your bank cancel a payment made to a fraudulent website.
It adheres to regulations established by card networks (such as Visa and MasterCard) and the Electronic Fund Transfer Act (EFTA), providing buyer protection for electronic financial transfers.
Furthermore, you have the option to request your bank to block any future transactions on your credit card, ensuring that these threat actors are unable to exploit it.
This can be achieved by initiating either a fraud alert or a credit card freeze, effectively safeguarding you from financial losses.
The added layer of security provided by fraud alerts, akin to two-factor authentications, requires identity verification before any purchases can be made, offering an extra level of protection.
You may suddenly receive phishing emails with malware attached
Vapedance.com serves as a tool for cybercriminals to steal data from users who visit the site. Once you input any information on this website, it becomes ammunition that can be turned against you.
For instance, when you provide your email address while making a purchase or registering on the platform, the cybercriminals behind it seize this data, potentially using it to send phishing emails.
They can attach damaging malware, viruses, and trojans to the emails and make it something exclusive and alert to make the user click on the attachment fast and disregard whether it is safe or not.
Phishing emails are the most common source of malware and ransomware infestations around the globe. As a result, if cybercriminals acquire access to your email address, they now have a channel through which they can attempt to directly access your device.
Solution: Use an antivirus software to protect your device
An antivirus program is your all-in-one solution for dealing with malware. It serves as a preventive and corrective step, quickly detecting and eliminating malware from your device.
We cannot emphasize enough the significance of using antivirus software especially when facing potential malware threats due to visiting malicious websites like Vapedance.com.
Having antivirus software on your computer offers several significant benefits, including:
- Detection, filtering, and automatic removal of malware ranging from harmless adware to extremely severe ransomware.
- Providing caution and notifications for possibly risky websites that you may visit, helps you in mitigating online risks.
- Antivirus threat databases are regularly updated to ensure the detection of new viruses and the protection of your device.
- Keep your operating system clean by protecting all files on your computer, assuring their safety and integrity.
Which antivirus should I use?
The answer is dependent on how you use your computer, as several antivirus applications on the market offer benefits and drawbacks. Because most of them identify and remove malware at the same rate, we recommend choosing your choice based on research.
For example, if you use your computer for resource-intensive applications such as video editing, you might want to avoid resource-consuming antivirus programs.
Fortunately, numerous publications provide extensive comparisons of each antivirus's merits and cons. However, for the best of all worlds, we recommend one of the following antivirus programs:
The majority of free versions are already sufficient for removing and blocking viruses from your computer. Some antivirus products also provide free trials that allow you to learn more about their capabilities before making a purchase choice.
They can hack your accounts and leak them on public databases
In addition to that, if you registered on their website and used the same login credentials, such as your email address and password, that you use on other social networking platforms, chances are that they will also seek to obtain access to those accounts.
Additionally, they could potentially sell the data that they have obtained to third-party advertising or on the deep web, making it accessible to cyber criminals for exploitation.
The fact that your data is distributed around the internet makes it possible for a multitude of different threat actors to use it to target you for their malicious purposes.
For instance, they can obtain further information about the user whose data was leaked and use it to send phishing and malware attacks that are particularly targeted at that person.
Solution: Protect your identity with Aura
We recommend using Aura Identity Theft Protection, a powerful tool that keeps you safe from identity threats, such as SSN breaches and compromised online accounts. It actively monitors your personal information, ensuring it is not sold by data brokers on the Web.
Additionally, it alerts you if your identity, passwords, or accounts are detected on the Dark Web. Moreover, if someone misuses your SSN to open a bank account in your name, you'll receive an instant alert.
In the unfortunate event of becoming an ID theft victim, Aura's experienced fraud resolution team will guide you through the process.
They will assist you in dealing with credit bureaus, initiating credit freezes, and working tirelessly to resolve your fraud incident.
To further enhance your protection, Aura Identity Theft Protection also includes Identity theft insurance with a $1,000,000 policy covering eligible losses and fees related to identity theft for every adult member of your plan.
More ways to protect yourself from Vapedance.com
At SecuredStatus, safeguarding user privacy and protection is our utmost priority. If you've entered your details or made purchases on the website, you do not have to worry.
We have compiled additional protective measures to ensure your safety from the potential risks posed by the malicious Vapedance.com website.
Update your login details and enable two-factor authentication
As we've already explained, creating an account with Vapedance.com using the same credentials you use on other websites could result in a data breach because threat actors have access to information like your email address and password that you used to register on their website.
They can easily connect to websites where you have an account if the email address and password match those from your other accounts.
For any website where you have an account, you should enable two-factor authentication in addition to simply reset your password.
This will make sure that you go through a verification step before logging in, such as entering a 6-digit code that will be given to your phone number.
With this, only you will be able to log in to the aforementioned accounts. If you suddenly receive a two-factor verification, it signifies that hackers have attempted to connect to your account but were unable to do so because they lack access to the code that was sent.
Check for personal leaked data online
The very last thing you would want is for your email address and password to be made public on the internet. Since then, user logins have been taken as a result of data breaches at respectable websites and made available on the dark web, leading to the leakage of data.
All of the information you provided on the malicious Vapedance.com website is not secure, to begin with, that is why to guarantee overall safety, it is crucial to search for data breaches involving your accounts.
Using a leaked data scanner, which will look for potential leaks of information that includes your email address or password, is one of the best ways to check for personal data leaks.
You may use the following data leak checker tools to examine your data for leaks:
- Dehashed.com
- Intelx.io
- Haveibeenpwned.com
The websites listed above have a large data leak from which they draw their data. Rest assured that if the malicious Vapedance.com website has released your personal information, you might be able to find it on one of these leak detector websites.
Hide your online presence with a VPN
Every website possesses the ability to track your location and gather details about the device you're using. Unfortunately, this information can be misused, leaving you vulnerable to various scams and fraudulent activities. That's where VPNs come to the rescue.
VPNs offer a vital shield of anonymity. By using a VPN, these malicious online stores won't have a clue about your actual location since your IP address is masked, giving the impression that you're browsing from an entirely different place. This adds a powerful layer of protection against potential exploitation.
Furthermore, the magic of VPNs lies in their encryption capabilities. They fortify your internet traffic, making it difficult for third parties to intercept and pry into your sensitive data. This means you can browse the web with peace of mind, knowing that your online activities remain private and secure.
So, if you want to safeguard yourself from the prying eyes of internet threat actors and maintain your online privacy, embracing the power of a VPN is a smart and natural choice. In this case, we recommend Mullvad VPN.
Since user privacy is the main focus of a virtual private network program, Mullvad VPN excels at putting users' privacy first. You do not need to enter your email address while registering to download their application because they maintain anonymous accounts.
If you want to hide or don't want your credit card information to be disclosed, Mullvad VPN also accepts Bitcoin payments. According to their website, they support a free internet that is devoid of surveillance and censorship.
They have also been announcing new server locations to guarantee users a fast connection anytime they want to connect to various areas throughout the world.
Frequently Asked Questions (FAQs)
Since we think you might still have some questions about Vapedance.com, here are some of the most asked queries regarding this topic.
So that you may leave this article knowing everything there is to know about the phony Vapedance.com online store and how to protect yourself online.
How do I report Vapedance.com?
Fake online shopping sites like Vapedance.com can be reported to the Federal Trade Commission via the reportfraud.ftc.gov website.
When asked what kind of problem you are reporting, choose "Online shopping" and continue with the complaint. Make sure you provide enough information so that authorities can investigate the case knowing more about the fake Vapedance.com website.
What are the odds of getting money back from Vapedance.com?
In an actual fraudulent purchase scenario, your case is highly likely to be accepted for a chargeback, given that you are dealing with a fake online store and an unintentional purchase on your part.
As a result, there is a high probability that the money used to purchase the unwanted items will be fully refunded. Once your bank verifies that the purchase indeed originated from a fake website, the chargeback will be approved and the funds returned to you.
Can the creators of Vapedance.com steal your identity?
Identity theft is a highly widespread action among those whose personal information has been exposed. Since login information may be compromised, impersonating such a person will be fairly simple, making access to accounts and interpersonal connections easier.
If you followed the instructions above, you do not have to worry since your accounts are secure because all of the passwords have been changed, and two-factor authentication is enabled.
Not to mention the fraud alert freeze, which will ensure that threat actors cannot use your identity to obtain a loan as verification is necessary.
Is it possible to get infected with malware from a malicious website?
The Vapedance.com website poses a great risk of malware infection because web users are required to provide sensitive information, such as their email addresses and many more. This information can be exploited by third parties to distribute malware.
As a result, you may begin to receive phishing emails with malicious attachments, which might cause infections on your computer. Using antivirus software like Kaspersky or Malwarebytes can immediately remove the malware for you in such circumstances.
