Superdrysale.com looks to be an e-commerce website that provides highly discounted products and it most probably caught your attention through social media promotions.
If you are wondering if it is a trustworthy site, the answer is no. Superdrysale.com is a deceptive website made by cyber criminals to deceive users and capitalize from their visits to the site.
This website is particularly similar to other fraudulent online stores, such as Alignean.com, Worthyejoy.com and Wtobgvx.com, which are known for using misleading tactics and luring users through social media advertisements.
To be precise, the website may appear like a real e-commerce website, captivating users with cheap products, but it’s actually a malicious platform. Buyers who make purchases might receive replicas or nothing at all. The site might provide a fake shipment ID, leaving them anticipating a package that will not come.
However, the deception goes beyond a simple rip-off. Superdrysale.com serves as the initial step in a more darker cyber attack.
While it presents itself as an e-commerce website, its main purpose is to steal data. Nowadays, data is the new online currency, and cybercriminals exploit this to their advantage.
When you visit Superdrysale.com, your data is immediately at risk. The website logs your IP address, geolocation, and device information.
Here is what Superdrysale.com looks like:
Moreover, as part of the purchasing process, creating an account is mandatory, exposing your email address and password to cybercriminals.
The troubling aspect is that these sign-in details may be used across your various accounts, especially if you tend to reuse passwords.
As you submit your credit card information on the supposedly legitimate payment page, it’s important to note that it’s just a basic HTML and CSS design.
There are no actual payment providers involved; you’re basically providing your credit card details directly to the cybercriminals.
To make matters worse, the payment form also requires your full name, home address, and phone number. Now, cybercriminals have a extensive amount of data – your credit card details, name, address, country, phone number, email, and password.
This much data is nearly enough for cybercriminals to commit identity theft and carry out various forms of data-related crimes.
| What we know about Superdrysale.com based on public information | |
|---|---|
| Extension | com |
| Creation Date | January 30, 2024 |
| Last Updated | January 30, 2024 |
| Expiration Date | January 30, 2025 |
| Status | ok |
| Name Servers | seven.dnspod.net, tennis.dnspod.net |
| Registrar Name | West263 International Limited |
| Registrar Phone | 86.18030649815 |
| Registrar Email | abuse@hkdns.hk |
Here's something you should know: When determining whether a website is legitimate or not, check its registration date. A newly created website can be a major red flag. In this case, Superdrysale.com was just registered 3 days ago as of the time of the investigation.
How The Malicious Superdrysale.com Website Work
Superdrysale.com is the starting point for a dangerous cybercrime and potential malware attack. It might sound like a big claim, but about 2,200 cyberattacks are happening every day, and over 5 million cases of identity theft are reported to the FTC each year in the US alone.
Wondering where this threat originates? Well, websites like Superdrysale.com are major contributors to these cybercrimes.
To understand how the whole scheme operates, let's break down how the Superdrysale.com website is used and what happens next.
1st Stage - Luring You In With Absurd Advertisements
The first step in the attack involves a carefully planned strategy to deceive users. The scam website, like Superdrysale.com, is promoted on popular social media platforms such as Facebook, Instagram, and TikTok. These cybercriminals use sponsored content, often claiming clearance or closing sales with big discounts.
They might even mimic the appearance of well-known brands to trick users. Despite creating unknown brand names, people are still drawn in by the allure of massive discounts, which should raise a red flag, as such steep discounts could bankrupt legitimate companies.
2nd Stage - Stealing Your Sensitive Data Via Superdrysale.com
Once you land on their website, in this case, Superdrysale.com, the real plan unfolds. Psychological tactics come into play, such as showing limited-time offers with countdowns to create a sense of urgency.
To dispel suspicions, fake notifications claiming recent purchases appear at the bottom. These are automated and not genuine. In this stage, they now take your data, something as simple as visiting the site already logs your geolocation, IP address, and device type.
Creating an account exposes potential email and password combinations. Completing a purchase reveals your credit card number, full name, home address, and phone number.
3rd Stage - Using Your Credit Card Details For Their Gain
You might receive an email receipt or none at all. If you do receive one, it could come with a malware-infected attachment. A tracking number may also be provided for a shipment that either doesn't arrive, contains nothing, or is a poorly made knockoff.
After the initial chaos of knowing you got scammed settles down, cybercriminals will now use your credit card for their gain, ordering expensive items to a location where they can retrieve them undetected.
Their primary goal isn't just the small amount they scam from the Superdrysale.com website. Instead, they're after the valuable data that they can exploit by using the malicious site as bait.
4th Stage - Baiting You With Phishing Messages
Once they've exhausted the initial data, cybercriminals turn to phishing emails and messages, attempting to gather more information.
This could lead to extortion or selling the data on the dark web. They may send targeted phishing messages and emails, and they may appear authentic due to the crucial information that you provided to Superdrysale.com.
We recommend everyone to verify unknown sources and avoid opening attachments or clicking on unfamiliar URLs.
5th Stage - Utilize Your Data For Identity Fraud
The final, and most concerning, stage involves identity fraud. With enough data, cybercriminals can commit crimes such as taking out loans in your name or soliciting money from friends and family under false pretenses.
Identity fraud is dangerous, harmful, and can have devastating impacts. When sufficient data is obtained, cybercriminals can convincingly pose as you, leading to further breaches and potential harm to both you and those close to you.
What's the best solution? Keep yourself and your family safe from online threats like data breaches, cyber-attacks, and identity fraud by using Aura. As the saying goes, it's always better to be safe than sorry.
Additionally: They can sell the collected data on the dark web
They could potentially sell the data that they have obtained to third-party advertising or on the deep web, making it accessible to cyber criminals for exploitation.
The fact that your data is distributed around the internet makes it possible for a multitude of different threat actors to use it to target you for their malicious purposes.
For instance, they can obtain further information about the user whose data was leaked and use it to send phishing and malware attacks that are particularly targeted at that person.
How To Protect Yourself Against Superdrysale.com
No one should face terrible consequences just for clicking on an ad to buy something at a discount. SecuredStatus is a website committed to stopping these cyber attacks.
Even if you only visit our site once, we aim to ensure you feel secure and confident against cybercriminals like those behind Superdrysale.com.
Call your bank for a refund and stop transactions
After making a purchase from the deceitful Superdrysale.com, it's important to contact your credit card issuer right away.
Inform them about the unauthorized purchase, providing details such as the specific product(s) you bought and where it was purchased.
You can do this by initiating a chargeback, a safety measure allowing you to dispute a transaction and ask your bank to cancel a payment made to a fraudulent website.
This process follows rules set by card networks (like Visa and MasterCard) and the Electronic Fund Transfer Act (EFTA), offering consumer protection for online financial transfers.
Additionally, you can request your bank to block any future transactions on your credit card, preventing the threat actors from exploiting it.
You have the option of implementing either a fraud alert or a credit card freeze, adding an extra layer of protection against financial losses.
Fraud alerts work similarly to two-factor authentications, requiring identity verification before any purchases can be made, providing an added level of security.
Prevent future cyberattacks by using an antivirus program
This is very important because Superdrysale.com is a creation of cyber criminals, so it comes with risks. They might send you fake receipts for your purchases, which could be infected with malware.
Since they have your email and other data, they can create targeted phishing emails with malicious attachments and harmful links leading to dangerous websites.
It's tough to tell if a link or file is safe just by looking at it. They may even pretend to be someone you know, tricking you into thinking the file is from a coworker, a common cause of data breaches and cyber-attacks.
So, what's the solution to this ever-growing problem?
To prevent this, it's important not to get infected with malware in the first place. One effective measure is investing in a reliable antivirus program to enhance your protection.
Yes, we used the term "investing" because that's exactly what it is. Unlike the early 2000s when malware would visibly pop up on your screen, today's threats are in stealth mode, and you might get infected without even realizing it.
We invest in insurance for our physical well-being, so it makes sense to view antivirus software as digital insurance for our online activities. In today's world, where everything we do is online, it's important to protect that part of ourselves.
This is especially important if you use your computer for work. It's even more important for mobile devices like Android phones, which are susceptible to spyware, trojans, and harmful malware infections.
Introducing... Malwarebytes Anti-malware. It has been around for over a decade, making it one of the best software for spotting and getting rid of the malware.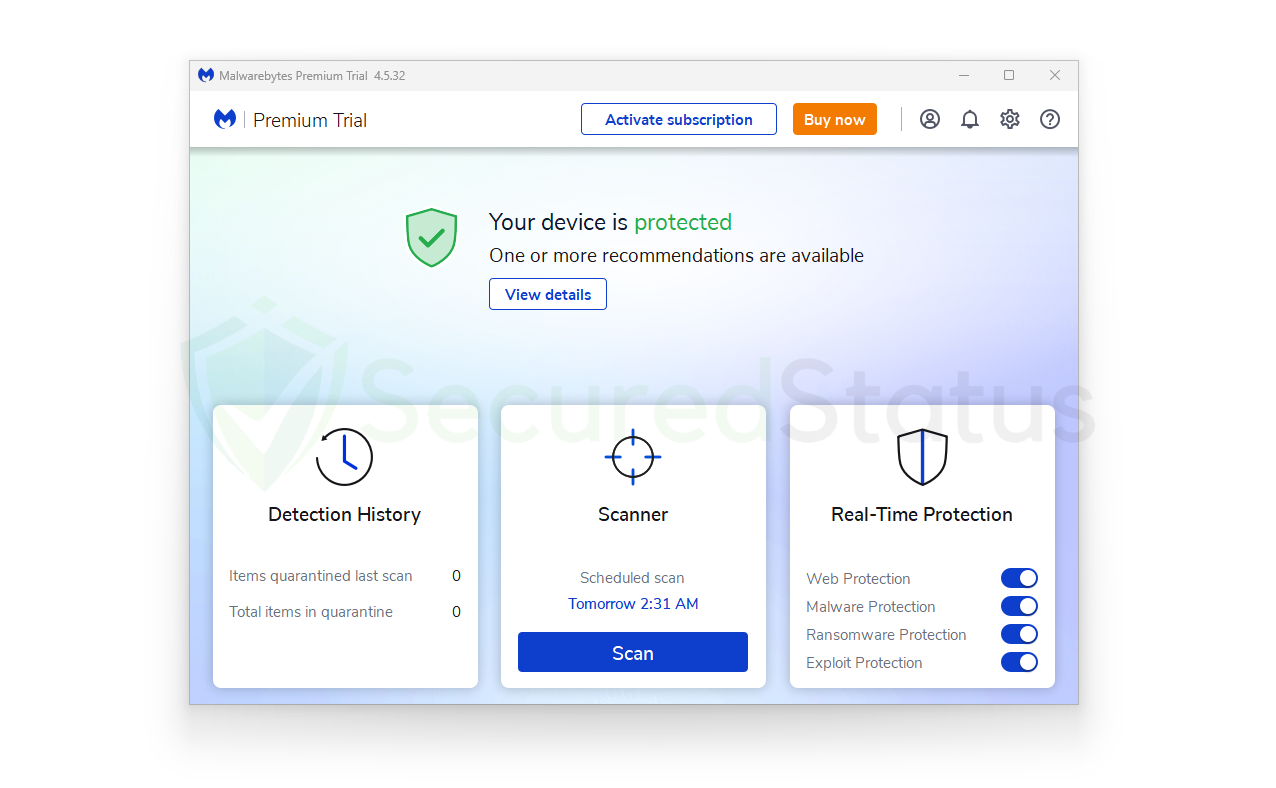 We conducted a malware detection test using Malwarebytes and it performed really well. Its standout feature, the one you really need, Real-Time protection, ensures your computer and mobile device stay safe from malware threats coming from various attack sources.
We conducted a malware detection test using Malwarebytes and it performed really well. Its standout feature, the one you really need, Real-Time protection, ensures your computer and mobile device stay safe from malware threats coming from various attack sources.
Get Protected with Malwarebytes
You can use Malwarebytes on macOS, Windows, and Android, protecting all three devices simultaneously with a single $5 monthly subscription.
Update your login details and enable two-factor authentication
As mentioned before, using the same login details on Superdrysale.com as you do on other sites could lead to a data breach. This is because the bad actors behind the site have access to information like your email address and password used during registration.
If these credentials match those of your other accounts, the threat actors can easily gain access to those accounts as well. To enhance security on all your accounts, consider enabling two-factor authentication and regularly resetting your password.
Two-factor authentication adds an extra layer of security by requiring a verification step before logging in. This could involve entering a 6-digit code sent to your phone number.
Only you, with access to this code, can log in to your accounts. If you receive a two-factor verification request unexpectedly, it indicates that someone attempted to access your account but failed because they lacked the necessary code.
Most important of all, protect your online identity
The last thing anyone wants is for cybercriminals to use their identity for personal gain. This can lead to targeting your loved ones and extorting them, which is something nobody on this planet would want to happen.
In today's internet age, data is the currency, not just money. As mentioned earlier, those with the most data hold the upper hand online.
You might have heard about data brokers on the internet buying and selling data, and cybercriminals do the same on the dark web. The problem is, what do they do with the data? You probably don't want to know, but you might have a clue.
Data spreads everywhere, and once it's out, it seems unstoppable, right? Wrong.
Despite that, there are innovative products out there, and one of them is Aura—an all-in-one data protection not only for you but also for your loved ones.
So, what does Aura do exactly?
It provides fraud and identity protection across the entire internet to ensure your data isn't used by data brokers and buyers. With online crime on the rise, it's important to be protected, and Aura can help safeguard you and your family from falling victim to cybercrime.
It's better to be safe than sorry, and Aura offers identity protection along with financial fraud protection. It even has an online fraud protection expert to guide you.
If you truly desire a breath of fresh, secure internet air, this is something of a must-have.
Get Online Protection with Aura
To stop potential data issues before they escalate, try Aura. It will remove all leaked data from platforms like Superdrysale.com and many others that have exposed your information.
Report Superdrysale.com to the designated authorities
Finally, make sure to report Superdrysale.com to the right authorities and let them take it from here. You've done your part, and congratulations on avoiding this potentially disastrous scam.
However, you should realize that the next person visiting Superdrysale.com might not be as fortunate. They may not see the warnings and could be unaware of the dangers ahead.
To bring down those behind the malicious website, it's important to rely on authorities who can take appropriate action.
Here are the links where you can submit a report:
Please complete the form with specific details to ensure that authorities can take prompt action and conduct a swift investigation into the matter.
How To Detect Fake Online Stores Like Superdrysale.com
If you've had a bad experience with a site like Superdrysale.com, you might feel hesitant about online shopping altogether. However, it's essential to know that there are many legitimate websites out there, and encountering one bad apple doesn't mean the whole bunch is spoiled.
To assist users in avoiding such incidents in the future, we've put together ways to recognize fake online stores. This information can help you steer clear of them and, hopefully, protect other unsuspecting users from similar experiences in the future.
They use stolen images in their product category
Fraudulent online stores such as Superdrysale.com probably lack the means to feature authentic product placement images due to them not caring to purchase a bunch of products.
That is why they might resort to generating AI-generated images or, more commonly, using stock images or product photos sourced from legitimate websites.
To verify the legitimacy of an online store, take a few product placement image addresses from the website and paste them into reverse image search tools like Tineye and Duplichecker.
This will help determine if the images have been used elsewhere online, potentially indicating a scam.
Offer big discounts that are too good to be true
As the saying goes, "If it sounds too good to be true, it probably is." This statement holds, especially when dealing with online stores.
Large discounts often serve as bait, luring unsuspecting buyers into purchasing counterfeit items or, worse, receiving nothing at all in return for their hard-earned money.
We strongly advise buyers to exercise caution and refrain from placing trust in these seemingly irresistible offers, as they are often designed to trick online buyers.
If you genuinely seek to find products at a lower price, we suggest considering waiting for genuine sales events from legitimate stores or waiting for special occasions like Black Friday, where big discounts can be found.
Legitimate ways to save money through discounts exist, but websites like Superdrysale.com are not among them; instead, such sites can lead to financial loss and potential identity fraud.
Little to no customer reviews
Our research on Superdrysale.com resulted in little to no reviews regarding the products they offer. Typically, buyers rely on reviews from other customers to gauge the credibility of a store before making a purchase.
However, in the case of fake online stores, it is common for such websites to lack genuine reviews. This lack of feedback raises suspicions about the legitimacy of the store's operations.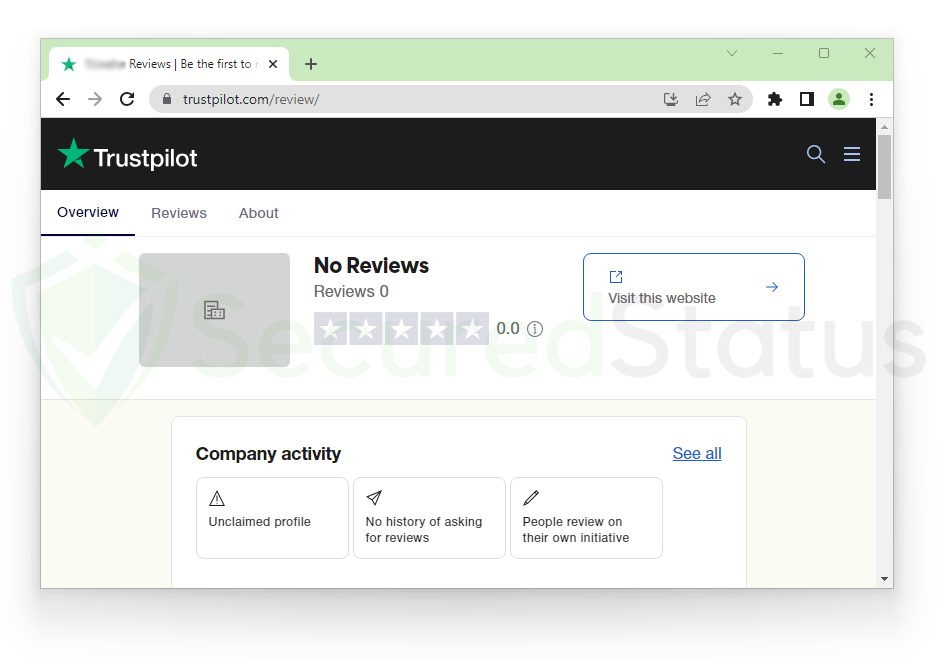 It is also possible that any positive reviews found could be fabricated by bot accounts, aimed at boosting the deceptive store's reputation.
It is also possible that any positive reviews found could be fabricated by bot accounts, aimed at boosting the deceptive store's reputation.
On rare occasions, genuine reviews may surface, warning users about the scam nature of the Superdrysale.com online store.
However, it appears that in response to such negative feedback, the store may selectively remove these reviews to mislead potential buyers and maintain an appearance of legitimacy.
They use the same website designs
Cybercriminals make websites like Superdrysale.com to trick people on the internet. They create hundreds of these fake sites at a time to target a large number of users. They might have made Superdrysale.com and many others that we haven't discovered yet.
This is why online users need to learn how to tell apart malicious online stores from legitimate ones. One noticeable thing is that cybercriminals often use the same design for all their fake websites.
While there are a great number of website themes and designs available on the internet, a small number of templates are commonly used by the people behind such sites.
Based on our research, we've identified some of the website designs that cybercriminals use for their fake online stores, like Superdrysale.com.
The images above show common website templates that cybercriminals often use for deceptive websites like Superdrysale.com. If you come across enticing sales ads on social media that lead you to a website with the same design, it's a good idea to be cautious.
However, not all fake websites have the same design, as different attackers have various approaches. Some cybercriminals create websites that look legitimate and you can't easily tell if they're scams based solely on the design.
Therefore, while website design shouldn't be the only factor, it's still wise to be cautious, especially if a website uses the same hero images as the ones shown above.
Additional factors to watch out for in an online store
Considering website design is helpful, but it's not foolproof. Legitimate online stores might also use similar templates and get mistakenly flagged as scams by some scam-detecting sites.
To ensure a more reliable method for identifying whether a website is a scam, you should pay attention to specific elements within the website itself.
For instance, Superdrysale.com employs psychological tactics to encourage users to make purchases, potentially leading them to disclose personal data.
As a public website, we at SecuredStatus can analyze their site and expose the tricks they use to manipulate users into buying. Our research highlights what you should be cautious of:
The "Recently Bought" pop-up at the bottom of the screen
The "Recently Bought" pop-up is a tactic commonly used by marketers, but cybercriminals often exploit it to create a false impression that people are actively making purchases on the website.
In reality, this is a scam. Anyone can generate a pop-up with fake information, such as different names, locations, and purchased products, whenever someone visits the site.
This is a trick frequently employed in online stores run by cybercriminals. It aims to give the illusion of a trustworthy website where others have already made purchases. However, it's simply a coded message and no real purchases occurred at that moment.
Too-good-to-be-true top bar message
Another thing to watch out for is the top bar message that appears at the top of the website. These messages often show up when you first visit the site, and they play on psychology to make users believe they're getting a better deal than initially advertised in the social media ads that brought them to the website.
After analyzing thousands of websites, we've found the most common messages:
- Up to 90% off on products
- Free shipping for orders over $60
- Hurry Up! Sale Ends in 2 hours
Worldwide shipping & Clearance sale This is another marketing trick that cybercriminals frequently use. If you encounter such top bar messages, along with the other factors we mentioned, it's a sign that you need to be cautious with the website.
Discount coupon upon visit
When you visit websites like Superdrysale.com, you might encounter a sudden pop-up offering discount coupons that you can use across the site.
This is a significant psychological tactic, making users think they have valuable coupons to spend, with the idea that spending more will save more.
However, it's all a false promise. Remember, Superdrysale.com is a scam operated by cybercriminals, rendering these coupons completely worthless.
They are only used to trick users into making hasty purchases. If you come across a pop-up like the one shown above, it's best to be cautious about the website.
Considering these common website elements, along with the other factors mentioned earlier, you can now distinguish fake online stores from legitimate ones based on the behaviors and key details typical of stores created by cybercriminals.
Frequently Asked Questions (FAQs)
To provide more information and address some common inquiries, here are answers to frequently asked questions about Superdrysale.com, based on our research.
What are the odds of getting money back from Superdrysale.com?
In an actual fraudulent purchase scenario, your case is highly likely to be accepted for a chargeback, given that you are dealing with a fake online store and an unintentional purchase on your part.
As a result, there is a high probability that the money used to purchase the unwanted items will be fully refunded. Once your bank verifies that the purchase indeed originated from a fake website, the chargeback will be approved and the funds returned to you.
Can the cybercriminals behind Superdrysale.com steal your identity?
Identity theft is a highly widespread action among those whose personal information has been exposed. Since login information may be compromised, impersonating such a person will be fairly simple, making access to accounts and interpersonal connections easier.
If you followed the instructions above, you do not have to worry since your accounts are secure because all of the passwords have been changed, and two-factor authentication is enabled.
Not to mention the fraud alert freeze, which will ensure that scammers cannot use your identity to obtain a loan as verification is necessary.
Is it possible to get infected with malware by interacting with Superdrysale.com?
Superdrysale.com poses a great risk of malware infection because web users are required to provide sensitive information, such as their email addresses and many more. This information can be exploited by third parties to distribute malware.
As a result, you may begin to receive phishing emails with malicious attachments, which might cause infections on your computer. Using antivirus software like Kaspersky or Malwarebytes can immediately remove the malware for you in such circumstances.
