SettingSysHost – What you need to know
SettingSysHost is a legitimate file name used by respected programs, but fraudsters exploit it to conceal their malicious software. It should be mentioned that it may cause damage to the computer system, therefore it is advisable to remove it as soon as possible.
One of the most prevalent techniques of infiltration is software bundling, in which their malicious program is mixed in with legitimate software such as video editing apps and other utility utilities. As a result, the malware is installed when the consumer installs the program.
Another typical way dangerous files like SettingSysHost enter the system is through suspicious email attachments; many people become infected this way because malware developers utilize appealing material to lure the user to click on the malicious attachment contained in the email.
When it is clicked, the virus spreads across the computer, compromising the user’s privacy and data. If your computer is infected by the mysterious SettingSysHost, you may notice lag and system overheating every time you use it.
The appearance of Windows PowerShell and Command Prompt every few minutes indicates that the machine is infected with malware. Please proceed to the section below and follow the removal instructions to remove SettingSysHost from the computer system.
SettingSysHost Removal Procedure
The methods provided below will assist you in removing the harmful SettingSysHost trojan virus. We made sure that it will assist you in resolving the malware issue on your system.
Removing malware from the system should be thorough and carefully executed; therefore, please follow every step provided.
We made the instructions below easy to understand so non-tech-savvy users can still remove the computer threat without needing help from tech support or a computer technician.
If you come across a method that doesn't appear to be working, please contact us via our Contact Page. We appreciate your feedback and will address the issue as soon as possible.
Step 1: Uninstall SettingSysHost from the computer
We have provided two methods for removing the malicious SettingSysHost trojan from your computer: standard uninstallation and, if that fails, an advanced uninstall method that ensures the removal will proceed without any complications.
Remove SettingSysHost via Control Panel
Uninstalling the application via the Control Panel is the most common approach employed for removing trojans from the computer. Within the list of applications, you can find the developer's name in addition to all of the installed applications.
1. From the Windows search bar at the bottom of your screen, search for Control Panel and click the result that matches the same application.
2. You will see different options, such as System and Security, as well as User Accounts. But what you want to click is the Uninstall a program under the Programs section. Depending on your Windows version, hovering over the uninstall section will be relatively the same.
3. Now that you are on the Programs and Features page, it will show you all the installed programs. There will be filters you may want to use, such as viewing them in lists with details such as the publisher, version number, and when they were installed.
4. Right-click SettingSysHost and click Uninstall to get rid of it (We will be using Adaware as an example). It will then proceed to remove the application, or you will be presented with an uninstaller that will guide you to remove it; either way, it will be removed.
There is a chance that the program may not be uninstalled successfully, and when that happens, it is important to use the power of an uninstaller program such as Revo Uninstaller.
It is widely known to be enough to remove malicious programs that are evading uninstallation. If you encounter such an issue when proceeding to uninstall the app, you may utilize the uninstaller to do the job for you.
Alternative: Remove SettingSysHost via Revo Uninstaller
For computer users who are uncertain of their next steps. You may choose to utilize Revo Uninstaller instead, as it is considerably more efficient and user-friendly. Revo Uninstaller is a useful application for consumers of Windows.
This uninstaller ensures that program modifications are also eliminated from the computer, including the Host File, Windows Registry, and other relevant locations. You can remove the SettingSysHost trojan by installing and utilizing Revo Uninstaller in accordance with the instructions below.
1. Click the button below to proceed with installing Revo Uninstaller on your computer since we have made an in-depth guide on how to use it on the following page. On the other hand, you can also head over to Revouninstaller.com and download it from there.
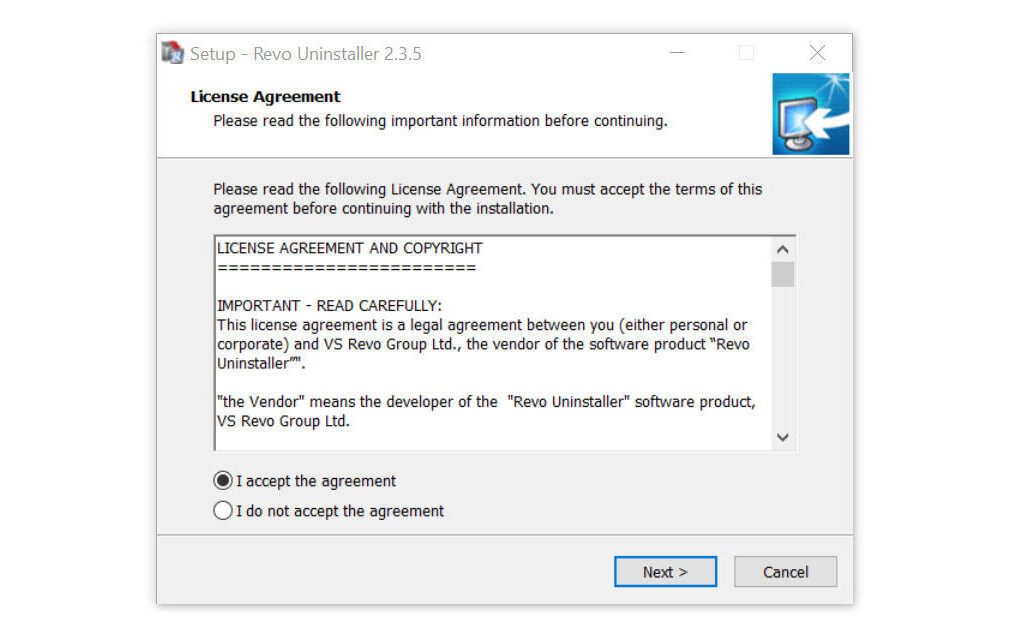
2. After the setup file (revosetup.exe) has finished downloading, run the installation wizard, read the license agreement, and click agree to proceed to the next step of the installation. Follow the procedure and wait until the installation of the software is complete.
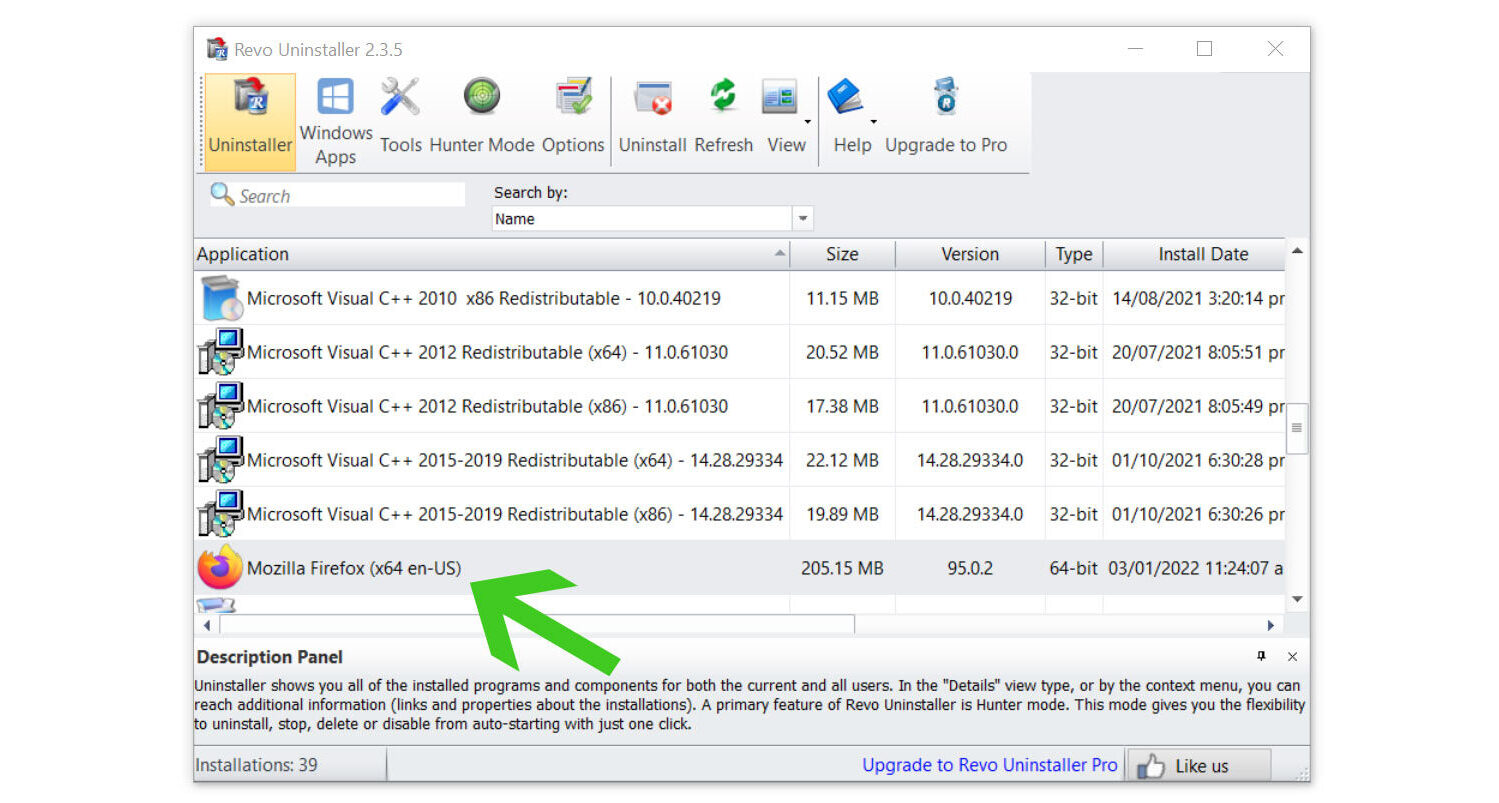
 3. Once the software has launched, find the harmful SettingSysHost trojan and double-click the program to uninstall it.
3. Once the software has launched, find the harmful SettingSysHost trojan and double-click the program to uninstall it.
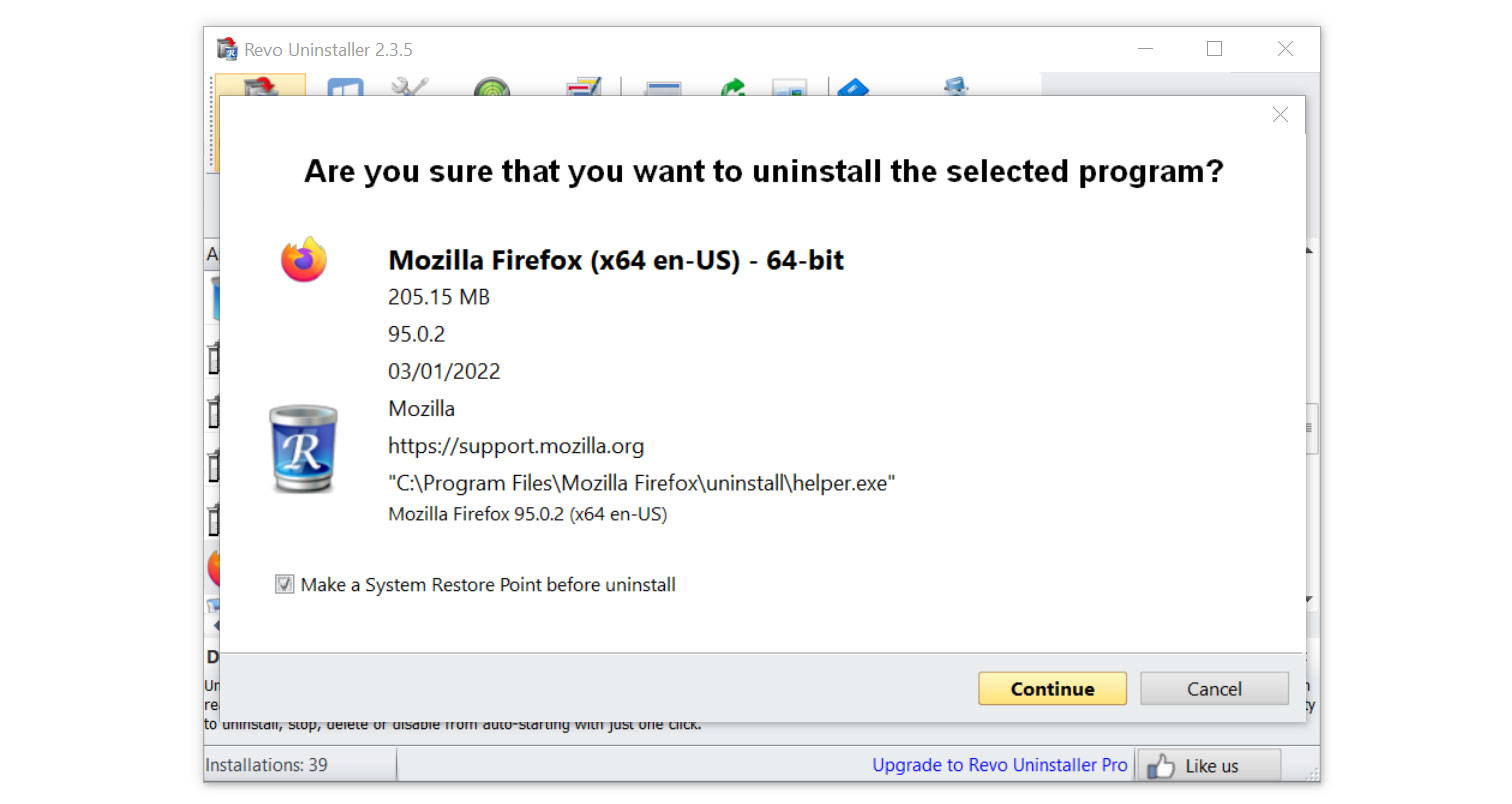
4. Click on the Continue button and follow the procedure to start uninstalling the SettingSysHost trojan virus. It is also advised to make sure that a System Restore Point is made before the uninstallation, just in case. (We will be using Firefox as a demonstration.)
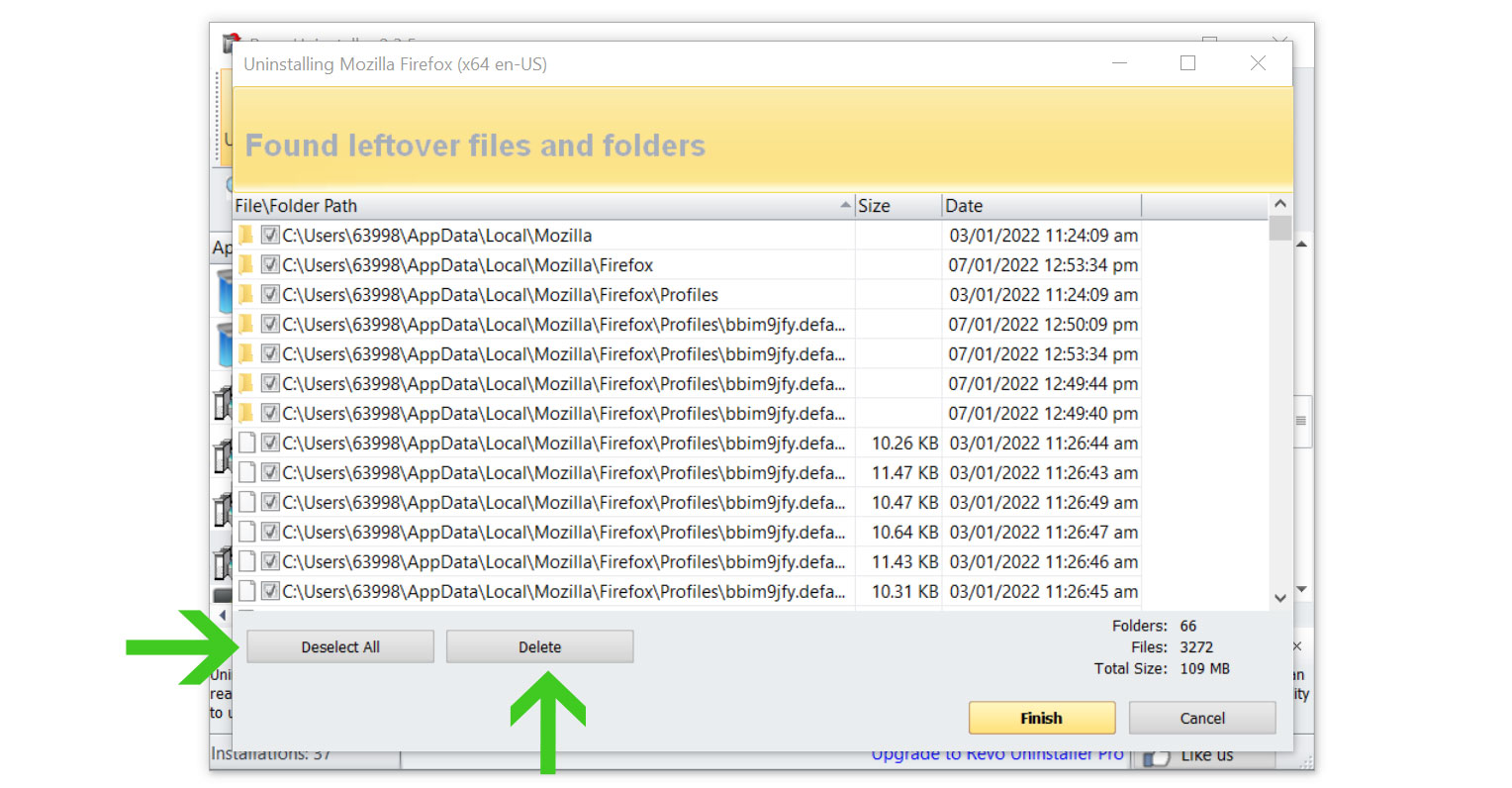
5. You will be prompted to choose a scanning mode. From the three options available, select Advanced mode, then click Scan.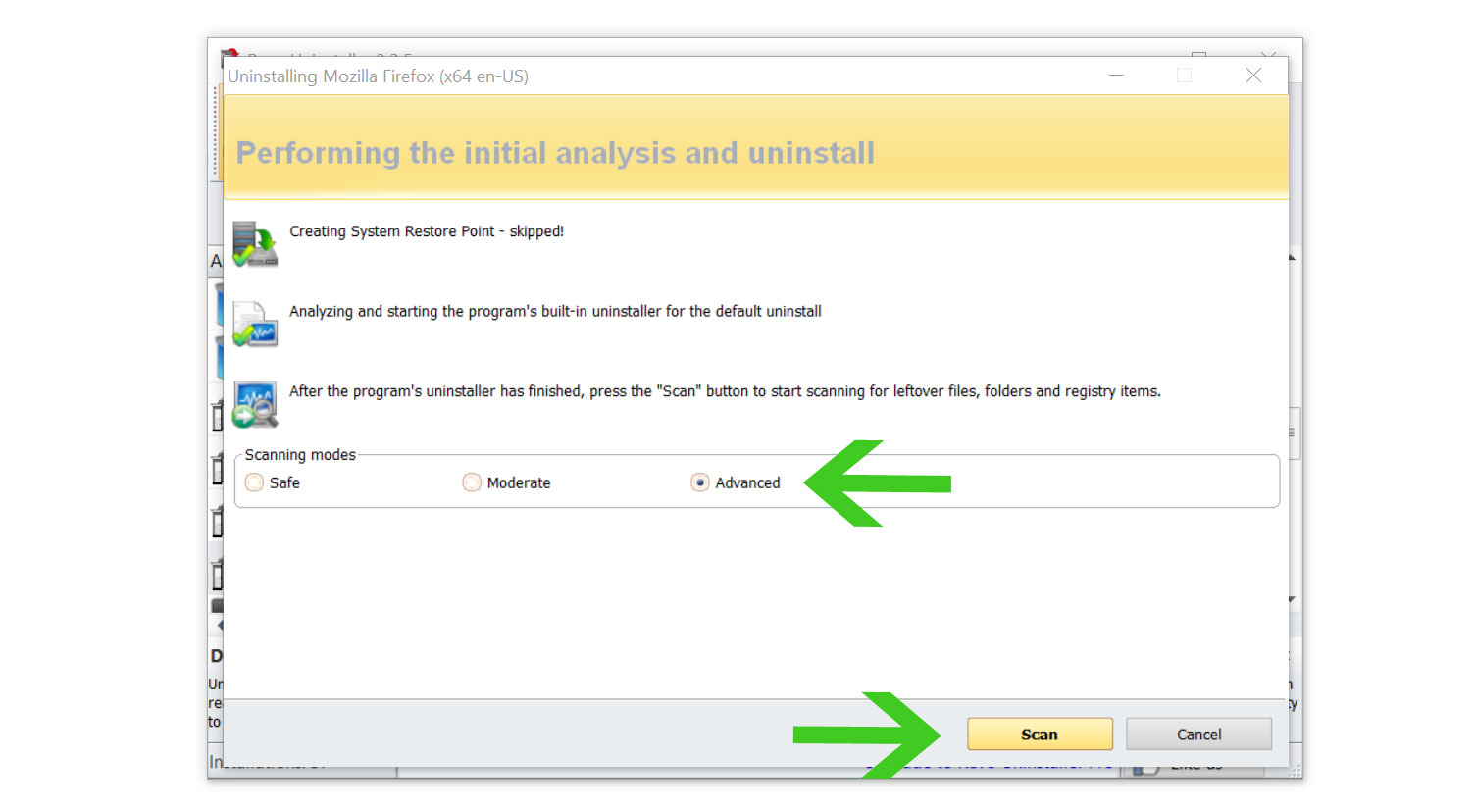 6. A window will pop up and show all of the leftovers and changes made by the uninstalled program. Click the Select All button and hit Delete to remove the leftovers found in the Windows Registry.
6. A window will pop up and show all of the leftovers and changes made by the uninstalled program. Click the Select All button and hit Delete to remove the leftovers found in the Windows Registry.
Once the window closes, you have successfully removed SettingSysHost from your computer system.
Step 2: Delete SettingSysHost manually
There is a chance that SettingSysHost may not be an installed Windows program but rather a single executable file that is hiding in the computer. If this is the case, then you can remove it by locating the source of the file and deleting it from there.
Please follow the instructions below to find and delete SettingSysHost manually from the computer.
1. When the trojan virus is causing your computer to overheat, launch Task Manager by simultaneously pressing the Ctrl, shift, and Esc buttons. Another option is via the Run program by pressing the Windows key and R, then typing taskmgr.
2. Check the processes that are running on your computer right now to discover how much hardware they are using once Task Manager has opened. Once you have located it, right-click on it and select Open file location.
3. Make that the file location does not originate from a Windows system directory, such as the C:Windows\System32, after the File Explorer has opened up while highlighting the SettingSysHost file, since you may risk unintentionally deleting a system file. If the software is not from a crucial directory, delete it by selecting it with the right-click menu.
If the file refuses to be deleted because the process is running as well as if certain programs are preventing it from being uninstalled, simply enter Windows Safe Mode and delete it from there.
Before doing so, please remember the directory where SettingSysHost is located because Safe Mode prevents non-essential files from running on the computer.
To boot into Safe Mode, first, open the system configuration by pressing the Windows Key + R button then type "msconfig.exe".
Once the System Configuration window appears, click Boot next to General then check the Safe Boot from Boot options. Below that, tick the Network option to allow internet within the Safe Mode then click Apply, once everything is done the computer should be restarted into safe mode.
After booting into the said mode, go to the directory where SettingSysHost is located and delete it. It should be able to be deleted now that the configurations preventing it from being removed are blocked in Safe Mode.
Step 3: Scan with powerful malware removal software
SettingSysHost may be hard to delete and for users who are not knowledgeable about their technology, it is best to utilize a program dedicated to removing such threats from the computer.
An antivirus program is your all-in-one solution for dealing with malware. It serves as a preventive and corrective step, quickly detecting and eliminating malware from your device.
We cannot emphasize enough the significance of using antivirus software especially when facing a threat like the SettingSysHost trojan virus.
Having antivirus software on your computer offers several significant benefits, including:
- Detection, filtering, and automatic removal of malware ranging from harmless adware to extremely severe ransomware.
- Providing caution and notifications for possibly risky websites that you may visit, helping you in mitigating online risks.
- Antivirus threat databases are regularly updated to ensure the detection of new viruses and the protection of your device.
- Keeping your operating system clean by protecting all files on your computer, assuring their safety and integrity.
Which antivirus should I use?
The answer is dependent on how you use your computer, as several antivirus applications on the market offer benefits and drawbacks. Because most of them identify and remove malware at the same rate, we recommend choosing your choice based on research.
For example, if you use your computer for resource-intensive applications such as video editing, you might want to avoid resource-consuming antivirus programs.
Fortunately, there are numerous publications that provide extensive comparisons of each antivirus's merits and cons. However, for the best of all worlds, we recommend one of the following antivirus programs:
The majority of free versions are already sufficient for removing and blocking viruses from your computer. Some antivirus products also provide free trials that allow you to learn more about its capabilities before making a purchase choice. However, in the end, the free version usually provides everything needed to remove malware.
For a better and safer web browsing experience, we've provided a few security measures and advice below that will safeguard your browser and computer from harmful threats like worms, malware, trojans, keyloggers, stealers, and other kinds of computer viruses that will harm user data.
Protective measures for better overall security
Removing the SettingSysHost trojan and other malware from the computer is one thing; keeping it secure for the future and for a long period is a different thing and will require certain things to make sure you are secured, especially if you do not know most of the ins and outs of the device you are using.
Cybercriminals are continuously improving their methods in order to infect users and steal money and information from them.
Before leaving this page, we firmly advise you to implement the measures outlined below to guarantee absolute security, as we strongly believe in the importance of web security and maintaining a secure online presence.
Safeguard your data and privacy online by using a VPN application
VPNs, also known as virtual private networks, guarantee your safety and complete anonymity while you browse the internet.
In contrast to a firewall, which monitors and blocks potentially harmful connections in the network, A VPN hides the user's connection via a tunnel so that it would appear to third parties as a different IP address and location.
This ensures that your data won't be leaked because the program hides it. Be aware that visiting infected websites may cause your IP address and location to be disclosed; however, if you use a VPN, this will prevent your true IP address from being revealed to malware actors.
Use a firewall to prevent cyber attacks
A security firewall is required for every internet connection that is made. It is an essential tool that enhances security and stops online attacks.
Through a security mechanism, it controls incoming and outgoing network connections on your system and network and filters the undesirable ones. Consider it a further barrier against malicious assaults and zero-day exploits.
Bottom Line
Although this may seem like standard procedure, we strongly advise against visiting illicit streaming or torrenting websites and, more significantly, against downloading anything from them, as doing so could lead to the installation of malware and viruses.
It is crucial to consistently ensure that your device is safeguarded against hidden exploits and cyberattacks. Although exercising caution and avoiding questionable websites are vital, safeguarding your network and data requires an effective line of defense.
If you experience another computer issue, please visit our website to find a solution for your problem or get in touch with us, and SecuredStatus will be happy to assist you once again.

