What is MEM:Trojan.Win32.SEPEH.gen?
MEM:Trojan.Win32.SEPEH.gen is the heuristic term the antivirus program Kaspersky names the virus threats found by its scanners. These malware are harmful and have the potential to harm the device they infect.
Kaspersky may have alerted you that MEM:Trojan.Win32.SEPEH.gen is present in your device since it might have picked up the said virus during its scan.
These warnings about detections shouldn't be ignored because they indicate that your device is weak and open to attack from cybercriminals.
Once your anti-malware software detects these kinds of threats on your device, you should take the appropriate action. It is important to get rid of anything before it does the computer a lot of damage.
These dangerous malware are frequently obtained via clicking on links in emails, visiting compromised websites, or receiving spam. MEM:Trojan.Win32.SEPEH.gen will start to propagate across your PC via Windows System files once it has been installed on the computer system.
Once they have been installed on the system, hackers may be able to access all the data on your computer and even take control of it.
Threats like this shouldn't be allowed to stay on the computer for a long time since they could cause permanent damage. Kaspersky may continue to warn you about this threat until you take action on it.
The following issues are most likely to be encountered by users who have MEM:Trojan.Win32.SEPEH.gen installed on their devices.
- Sudden problems with programs and the internet.
- Freezes or performance lags on the machine.
- Having trouble accessing or opening files.
- Unusual pop-up advertisements while surfing or browsing the web.
- Excessive heat and CPU utilization from unknown programs.
These kinds of discovered threats are particularly dangerous since they can be leveraged to steal bank information, privacy passwords, and other data from unknowing people and use it to attack them online.
As soon as you believe you may have been exposed to this virus, you must get rid of it. Since Kaspersky was the program that specifically identified and located the malware on your PC. Their antivirus program should be enough to eliminate the threat posed by MEM:Trojan.Win32.SEPEH.gen.
Before attempting to remove the virus, it is preferable to run the anti-malware tool in safe mode because there may be other programs running that prevent the threat from being eliminated unless specific circumstances prevent the program from doing so.
Safe mode will make it much simpler to remove MEM:Trojan.Win32.SEPEH.gen because it only uses the drivers and software that the system needs.
Boot into Safe Mode with Networking
To launch Windows Safe mode with networking, click the Windows button + R simultaneously to open the run dialog box.
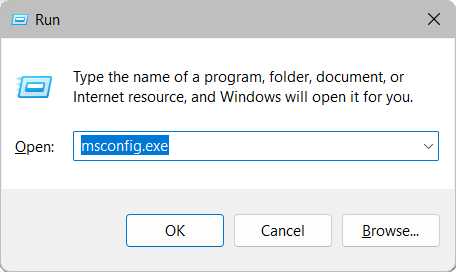
Once the run box is open, type msconfig.exe to open the Microsoft system configuration window.
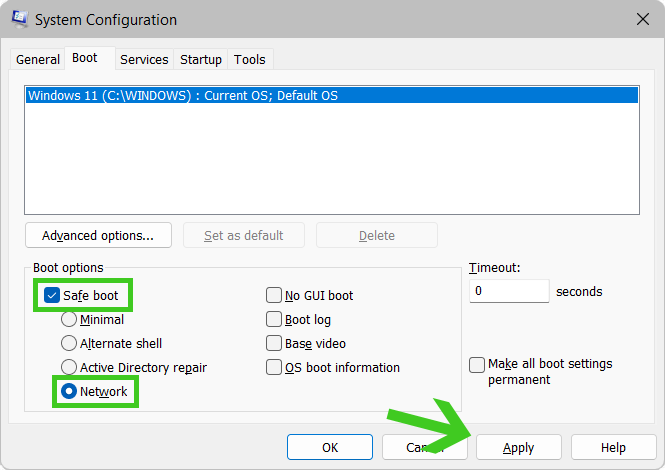
After the system configuration window has opened, click on the Boot option, tick Safe Boot, and then select the option below that indicates Network. You should then be booted into safe mode with networking after clicking apply.
However if Kaspersky was unable to remove the malicious threat from the computer, you may utilize Malwarebytes Anti Malware to help you remove the virus instead. You may follow the steps below to eliminate the threat that has been discovered in your system using Malwarebytes.
Remove MEM:Trojan.Win32.SEPEH.gen with Malwarebytes (Alternative)
This program is one of the most effective anti-malware programs available. They have some of the greatest threat detection software, ensuring that any unwanted threats on your computer are eliminated.
You can utilize this antivirus program to complete the task since it was this program that detected the malicious threat. Furthermore, even if MEM:Trojan.Win32.SEPEH.gen is completely removed from the computer, we recommend that you run a complete scan just in case.
1 Visit the antivirus website or click the button above to download the most up-to-date version of the software that best suits your requirements.

2 Follow the software installation instructions until they are completed.
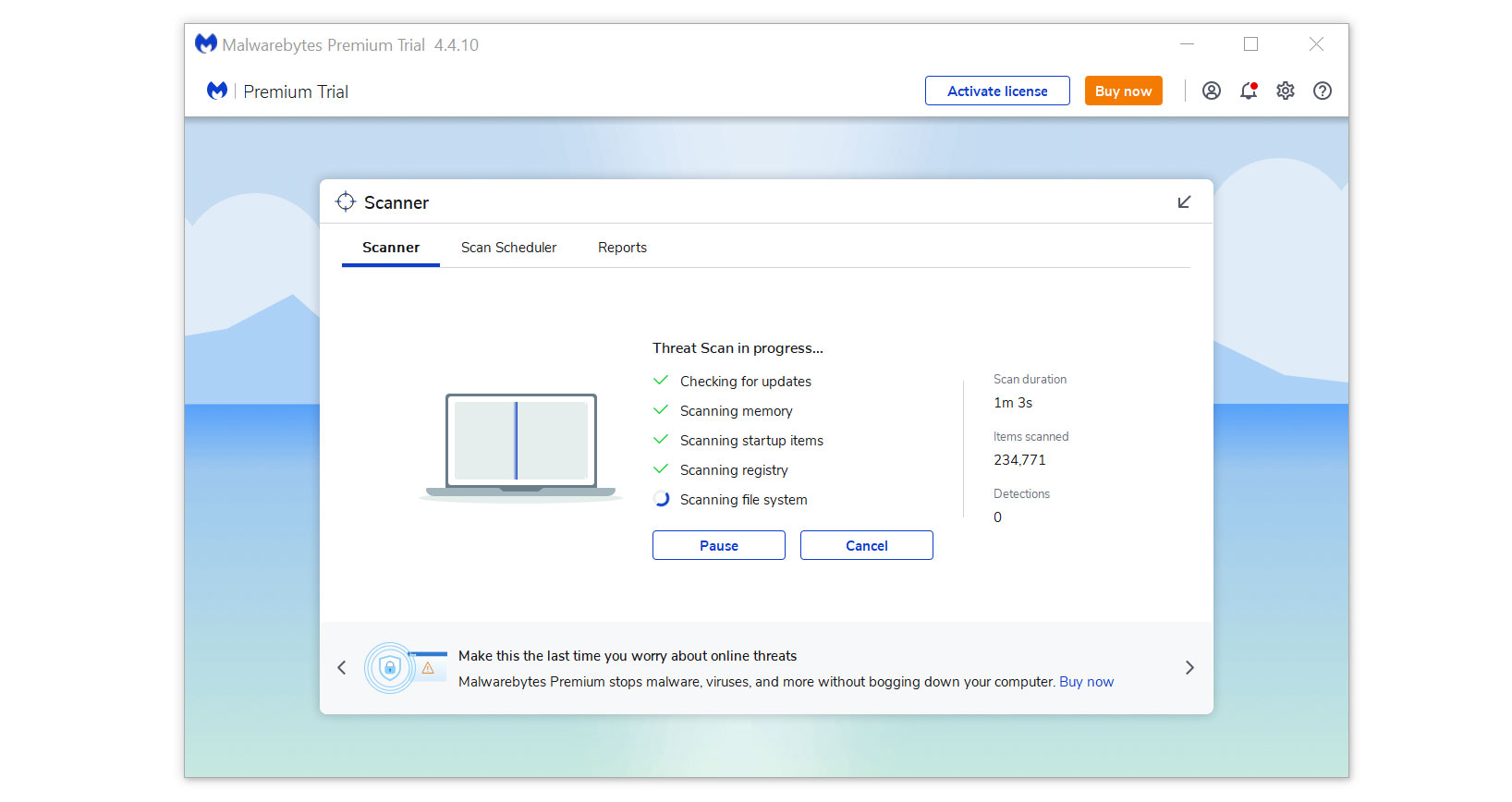
3 Run a complete malware scan on the machine and wait for it to finish.
4 All the detected threats found on the computer will be shown on the screen and clicking the "quarantine" button to remove them.
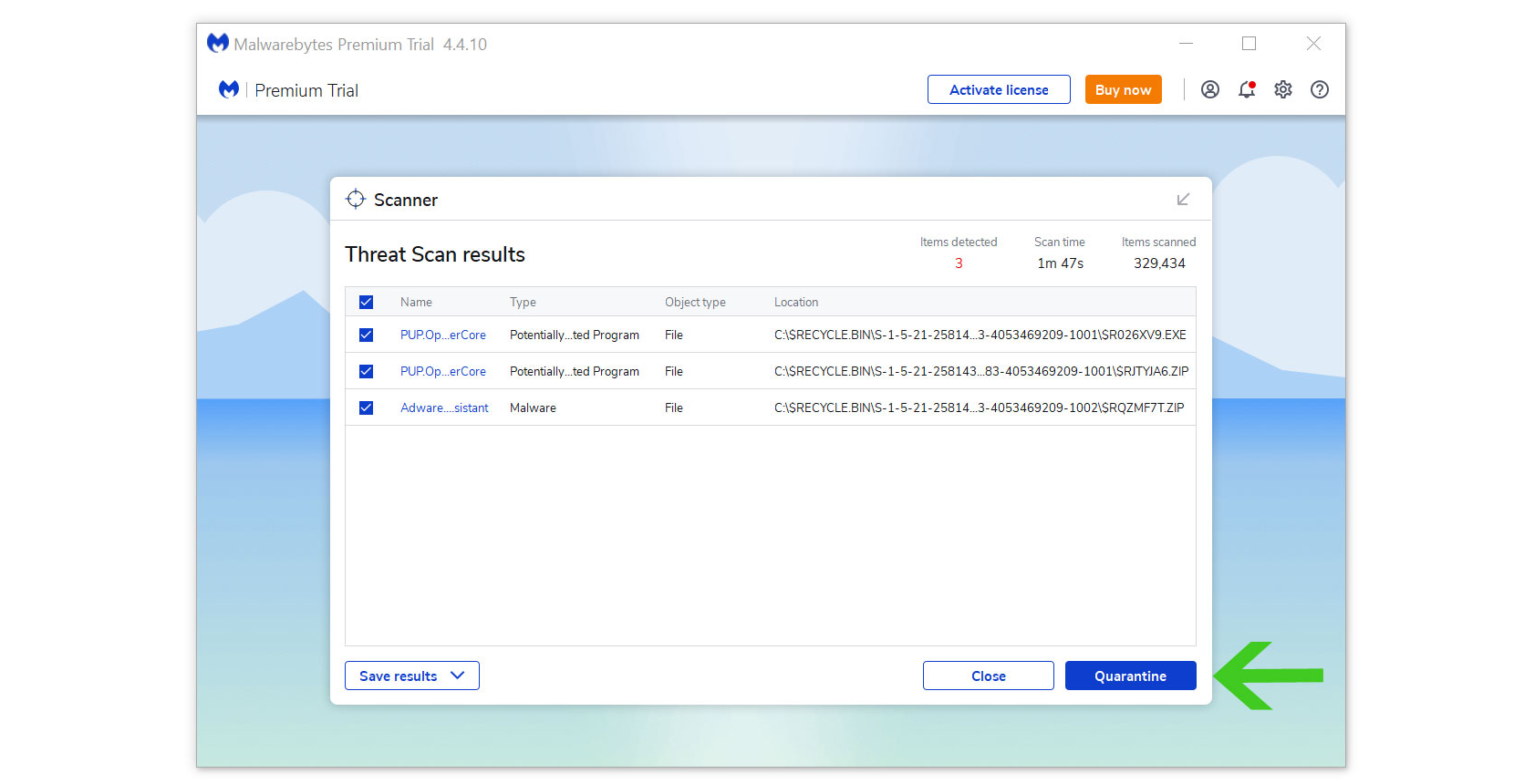
MEM:Trojan.Win32.SEPEH.gen, as well as any other harmful viruses discovered on the computer, should be eliminated once the process is complete. We also recommend using Malwarebytes Real-Time Protection, which will secure your machine and detect any threats as soon as they appear.
Tips to Keep Your Device Safe
- Never download software or programs from unknown sources. This is one of the most popular ways for adware and other malware to infiltrate your computer. Download only from recognized and legal sources. To be secure, avoid torrent downloads and cracked software download sites, as the files will almost always contain viruses.
- One of the most reliable ways to be safe online is to use a firewall. It protects users from potentially hazardous websites by acting as a first line of protection. It keeps intruders out of the user's network and device. In today's world, a firewall will protect a user from the risks that lurk on the huge internet.
- Anti-virus software must be kept up to date. These programs should always be updated on a computer since hundreds of new malware threats are produced every day that aim to infect the machine's weaknesses. Antivirus updates contain the most recent files needed to combat new threats and protect your computer.
- Only visit websites that have a secured connection. A site with an HTTP connection does not encrypt the data it receives and therefore is not considered secure. Entering personal information such as email addresses, phone numbers, and passwords on a website with an HTTP connection is risky since it could be compromised and your information was stolen. Websites with HTTPS connections, on the other hand, are secure since data is encrypted and attackers are unlikely to gain access to information exchanged within the site.
