Malwarebytes Anti-Malware is a powerful and efficient program for removing certain kinds of malware and computer viruses.
It is widely used by many users to remove malware from their computers and other devices because it is compatible with many different operating systems, including Windows, Mac OS, and Android.
In addition, its numerous other applications, including VPN and Browser Guard, are also useful tools to ensure that you are browsing the web securely.
With their key feature being real-time protection, this will ensure that your computer is able to not only identify and remove malicious threats from the advanced scanner, but also function as an antivirus program that can protect your device round-the-clock and watch for suspicious computer process behavior, preventing trojans and viruses from being able to do their harmful things to the computer.
As seen from our tests, Malwarebytes was also able to handle the latest threats that are frequently installed on computers. Now that all has been said, here are some specifics on why you ought to use Malwarebytes as a computer virus scanner and a defense against dangerous software.
Why you should choose Malwarebytes
Here are the major reasons why you should use Malwarebytes out of the various antivirus and security applications that are readily available online:
Advanced Technology
They utilize intelligent technology to identify dangerous viruses, as opposed to traditional and more prevalent antivirus, which still relies on out-of-date signature-based malware and virus detection that only tackles the threat at the time it is actually run on the machine.
Common antivirus software will have reacted recently to the malware because it was discovered as soon as it was launched at the beginning of an attack chain.
This makes it less effective because some threats may ultimately go undetected, and some malware may evade antivirus detection as soon as it is launched, allowing it to execute and engage in harmful behaviors.
Malwarebytes, on the other hand, uses a variety of proprietary detection technologies that work in sync to identify and stop an attack chain before it even gets started.
It can also detect malware from the time it is delivered or injected into a system all the way through its execution and post-execution.
Strong Web Protection
As the primary source of malware installation on a user’s device, the internet. Malwarebytes also works on blocking connections between the computer and the browser and dangerous websites and redirections.
Additionally, the instant the browser accesses the harmful webpages, ad networks that distribute malware, fraudsters, and phishing links are blocked, preventing any malware from being downloaded to the computer.
Making sure that if the user tries to click it, it won’t open and won’t ever finish the download, ensuring that it won’t be executed by the user and will instead go straight to quarantine.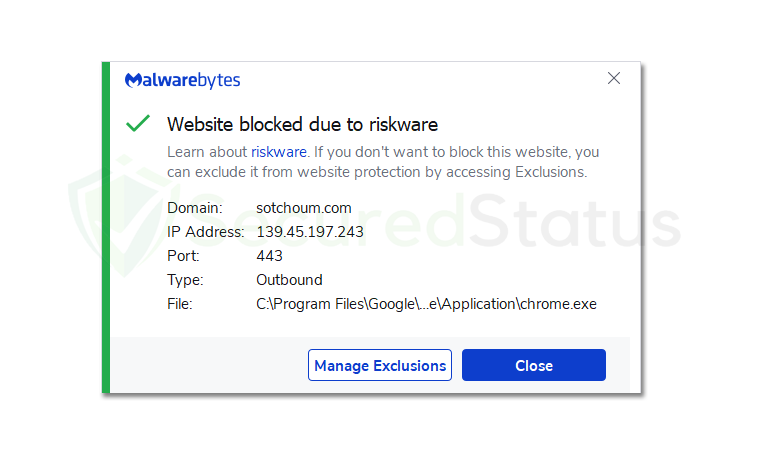 Their browser extension, Browse Guard, which is installed on the browser and performs the same functions as the main application but with a stronger focus on the browser and the websites being visited by the user, also acts as a line of defense for the browser.
Their browser extension, Browse Guard, which is installed on the browser and performs the same functions as the main application but with a stronger focus on the browser and the websites being visited by the user, also acts as a line of defense for the browser.
Exploit Mitigation
Cybercriminals are constantly discovering new computer exploits and vulnerabilities; therefore, developers often update their software to address this risk.
However, cybercriminals will continue to operate regardless of the situation, so even in the absence of malware installation, a system vulnerability is a very important place for malware to enter a computer.
This is why Malwarebytes is an excellent piece of software because it has an Exploit Mitigation system that ensures it can spot and stop attempts to exploit system and application vulnerabilities.
Additionally, remotely executed codes from other connections will also be blocked, preventing the malicious hackers from accessing the computer and terminating any connection between the two.
Application Behavior Protection
Since reputable apps are very unlikely to be identified as malware, cybercriminals frequently use other applications to their advantage in order to gain control over them and use them for their own gain instead of creating malware executable files for computers, which can easily be detected by antivirus software.
This is done, for instance, with legitimate coin mining programs and remote viewing programs that offer relatively unsafe tools. If those programs are not being used by the user who installed them but by someone else who wants to take advantage of them, primarily cybercriminals.
This kind of attack leverages reliable programs rather than trojan viruses, which hide themselves as trusted processes or well-known applications.
Application Behavior System, a feature of Malwarebytes, offers a foolproof solution to this problem by preventing applications from being used by cybercriminals to infect the user’s endpoint system or personal computer.
It recognizes harmful connections and actions that are less frequently known to be authentic and that originate from undesirable sources.
Anomaly Detection
This detection feature distinguishes Malwarebytes from other programs because it recognizes malware and viruses using machine learning techniques rather than matching-based or signature-based detections, which makes it distinct because it learns on its own to recognize and remove malware that may one day pose a zero-day threat.
When malware is installed on a computer, it’s possible that the anomaly detection system will be able to detect it based on prior knowledge and will be able to have it quarantined and removed from the computer.
As the detection system learns how these threats operate and analyzes them, it may also be aware of how the malware will soon adapt.
This makes it a foolproof approach; for example, if a user frequently downloads game modifications from a website, Malwarebytes will be able to determine whether or not a download is likely to include malware based on previous downloads.
Payload Analysis
Scanning is used to analyze payloads, so it’s critical for an antimalware tool to be astute in its detection of certain executable files.
Malwarebytes uses heuristic and behavior-based techniques to assess and identify not only specific risks but also the whole malware family associated with a given threat.
This further strengthens the program because, with Anomaly Detection, it can determine whether a threat is a variant or a part of a specific malware family.
This is because hackers can only update their malicious code so often, and machine learning tools are always going to be better and smarter than humans.
Payload Analysis is an effective malware detection tool that scans the malware file’s contents as well as the objects and files it drops from a specific command and control network in order to determine which other executables will be run on the computer once the primary file has been launched.
Ransomware Protection
Ransomware is an extremely dangerous Trojan virus that can lock all of the crucial files on the computer, causing a total disaster. Particularly if the impacted files have a strong connection to your personal background or are tied to your place of work.
In any case, you will always have essential files on your computer, and ransomware viruses will use this to their advantage to demand payment from you in exchange for your files.
In essence, it encrypts your data using a powerful encryption technique, and in order to reverse its effects, you’ll need a specialized decryption application that can only be obtained from the cybercriminals who initially infected you, thus being dubbed “ransomware.”
Malwarebytes uses a strong detection system to ensure that no such ransomware will be executed on the computer, and it also blocks ransomware using behavioral monitoring technologies that can determine whether a particular file contains codes that will lock and encrypt files, as well as whether it will leave a ransom note.
Minimal Hardware Resources Usage
The requirement to scan a large number of system, memory, and registry files, which can take a lot of time and resources, necessitates the regular usage of hardware resources by antivirus and anti-malware programs.
Malwarebytes offers a good detection scan that requires only 50% of the CPU resources less than what many antivirus programs use.
Please be aware that while CPU use might still have an impact, scanning will also rely on the hardware and operating system age of your computer because older systems run slower and experience higher CPU usage than the latest computers with better and faster processing power.
Malwarebytes is lighter than most software on the market since, unlike other antivirus software, it only has the features that users will need to protect their device against malware.
If you wanted to scan while playing a resource-intensive game or viewing a high-resolution movie, you could also enable Play Mode, which is a function that can be useful for these types of usage.
Malwarebytes Key Features
There are many reasons to use it, so since you’re considering downloading it, let’s first go through what you’ll get and the main features of the application so you’ll know what to use and anticipate after the app is installed.
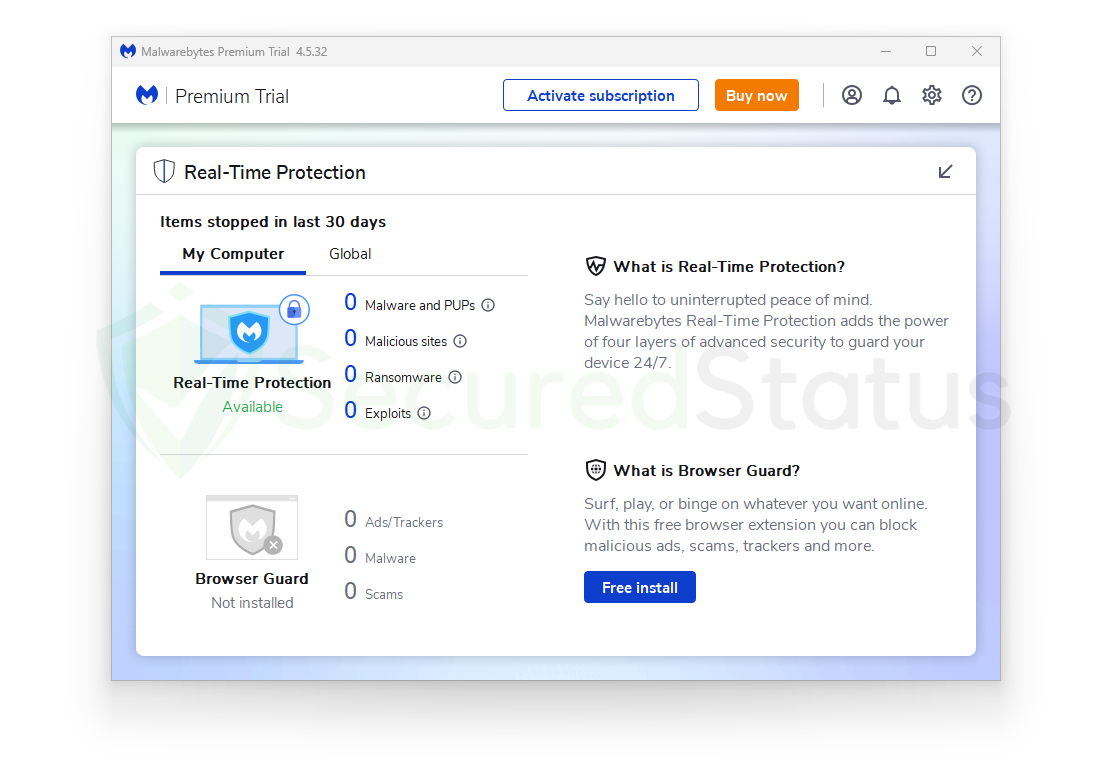
Real-Time Protection
Real-time protection is a feature that is available for both Windows and Mac operating systems. It is an essential component of the application that saves users from having to manually run system scans because real-time protection can be configured to scan for malware on a daily basis.
Along with performing a daily scan, it will also immediately stop all incoming malware threats that it finds on the computer, which is crucial to preventing malware execution and other malicious activities by online criminals that could result in data loss and theft.
Real-time protection, however, is a feature that stands out from the program’s primary function, which is to scan for malware. By using the real-time feature, the system will be automatically scanned, so users don’t need to worry.
Therefore, this function does not come for free; it is a part of the application’s subscription plan, which is reasonably priced and offers a lot of standard features. This is a tiny amount to pay for the assurance of computer security and to ensure that no malware ever sets foot on the computer.
Web Protection
Web Protection makes sure that users do not come across harmful websites while browsing the internet, such as phishing, tech support scams, pop-ups, and redirections that result in the installation of malware. As we have previously stated, this is extremely important because the majority of malware originates from and is distributed via the internet.
Users who do not use proper web browsing techniques, such as refraining from visiting illegal streaming websites and torrenting platforms, will most likely come across malware entities on the internet.
Cybercriminals are becoming more cunning in their attempts to convince users to download and grant permission for their malware; sometimes users will be tricked into solving a phony captcha while a malware download will then happen in the background without the user noticing.
Malware Protection
The majority of dangerous software that is found all over the internet falls into the category of malware. These dangers, which range from malicious stealers to coin miners, pose a serious risk to computer users since, for example, miners utilize computer hardware without the user’s permission, and stealer malware is designed to steal account information kept in browsers and computer files.
This is significant because it can allow cybercriminals to steal bank account information and other sensitive information, which they can then use against the victim to demand money.
The key to preventing all of these issues is automatic malware protection, which eliminates the need for any scanning at all because malware will be discovered and displayed to you as it is blocked before you are even aware of it.
Ransomware Protection
While other malware may appear to operate maliciously, ransomware is generally the one that causes the greatest harm to users because, as we have already explained, it digs into the files and locks them. Ransomware is considered to be the most harmful form of malware known to exist.
Once the files have been encrypted, a lump sum payment will be demanded by the cybercriminals, and it is uncertain if you will receive your files back at all. As files can be extremely valuable and sentimental to users, preventing ransomware is essential to maintaining a safe computer and data.
Malwarebytes provides protection against ransomware infections because it has accumulated an extensive database of signatures and patterns that may be used to identify the source of the threat, ensure that the virus does not execute on the user’s computer, and prevents the encryption from happening.
Exploit Protection
Computer exploits are often referred to as unpatched flaws in a system or application that can result in a vulnerability that malicious actors can take advantage of to compromise a system or a person’s computer.
This may result in ransomware and spyware infections, as well as expose it to subsequent malicious attacks. It is crucial to fix these vulnerabilities, which is why software frequently publishes updates and patches to make sure that any flaws in their system and program won’t be exploited.
However, as we already indicated, cybercriminals will continue to find new ways to exploit the system and its applications, so users will require a program like Malwarebytes to ensure that these exploits do not take place. Additionally, it offers real-time defense against exploits and ensures their execution is stopped.
Browser Guard
Malwarebytes Browser Guard is a useful browser extension that prevents users from seeing unsolicited and dangerous content online. This results in a safer and better browsing experience for you, one that is devoid of ads and nefarious website redirects.
Malwarebytes also claims that it is the only browser extension in the world that can recognize and stop tech support scams, which is beneficial because many people fall for these types of scams because they are specifically created to take advantage of unwary and uninformed consumers.
The extension not only protects you from harmful content but also speeds up your browser by ensuring that the webpage loads quickly by removing third-party advertisements and undesirable scripts from the website.
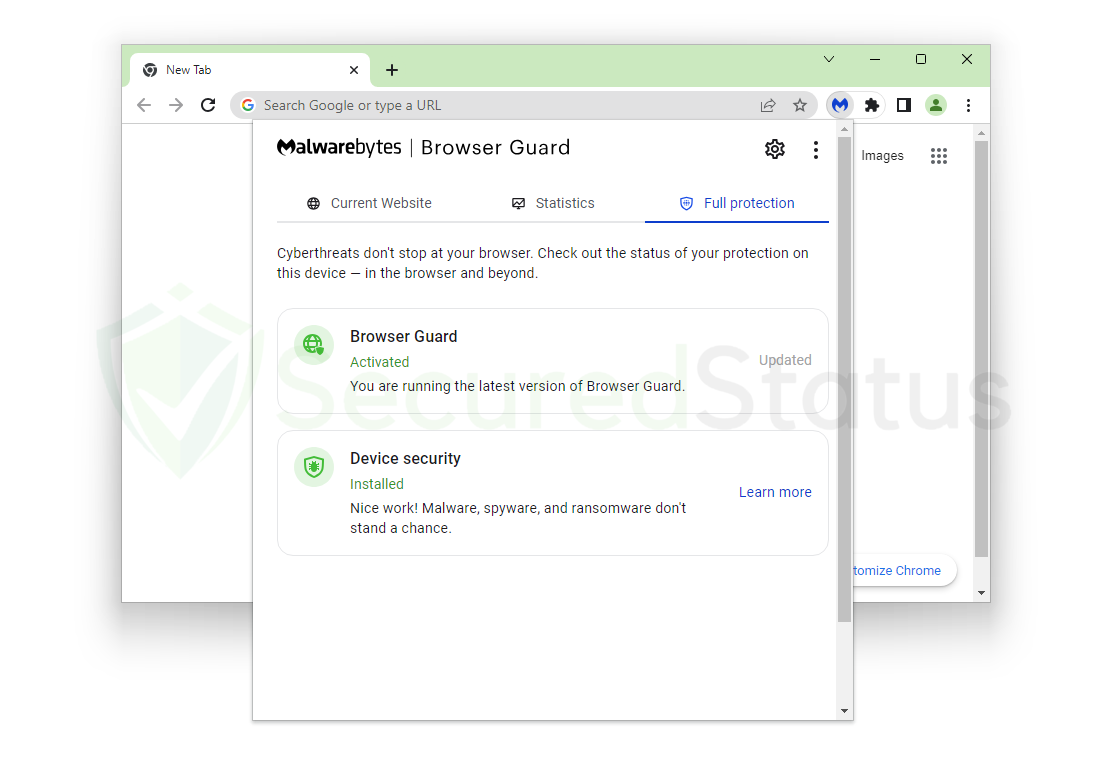
In addition to the primary anti-malware program, it can also detect and remove browser hijackers, which acts as an additional line of defense against online attacks.
It can also block third-party trackers that remember your location and IP address. Not only is it effective, but it is also free to use. If you don’t already have Malwarebytes Browser Guard, you may download it by clicking the button below:
Note: If you do not want to install the additional Malwarebytes extension, you may skip the browser extension download and proceed with the main software installation procedure in the section below.
Download Browser Guard (Optional)
Privacy VPN
When you purchase the premium version of the primary anti-malware program, you can also download the virtual network program Malwarebytes Privacy VPN. This useful addition is available only in the paid versions of the program and is not included in the free versions.
Privacy VPN can mask your network activities, which will prevent the disclosure of your IP address, location, and other information that can be seen while you browse the internet.
To ensure that the information passed via the tunnel is secure and cannot be compromised by other parties, Privacy VPN employs highly sophisticated 256 bit military-grade encryption.
Additionally, it uses the servers of Mullvad VPN which is a program we also highly recommend due its to fast servers and overall transparency with the application. With that being said, if you managed to go for Malwarebytes Premium, make sure to use Privacy VPN as an addition to be safe when browsing online.
How to Setup and Use Malwarebytes
Knowing everything there is to know about Malwarebytes anti-malware and the other add-on apps and browser extensions that it comes with can help you maximize both your computer’s and your online security.
Here is a step-by-step guide on how to download, install, and use the application, along with information on some of its additional features. You are therefore aware of its various applications.
For Windows Computers
Please click here to access the detailed step-by-step tutorial if you are using a Mac computer.
1. To start, click the button below to go to the official Malwarebytes website and download the anti-malware program. Additionally, you can access their official website directly using Malwarebytes.com (Please avoid misspellings since hackers on the internet occasionally employ them to send users to unsafe sites).
2. Check the application’s pricing, as there are many plans available if you decide to buy the paid edition of the application. This includes a VPN software for all of your devices to further secure your internet activity.
You can choose the paid version if you believe that a small price is worth it in exchange for enhanced protection. Should you only want to eliminate malware, then you may proceed to download the free version since Malwarebytes offers a 14-day free trial of the premium features, so you may try it first. This table lists the prices and features offered for each plan.
| Features Available | Premium Version (Starting at $44.99) | Premium + Privacy VPN (Starting at $59.99) |
|---|---|---|
| Advanced antivirus and anti-malware | ✓ | ✓ |
| 24/7 real-time protection | ✓ | ✓ |
| Malicious websites and phishing protection | ✓ | ✓ |
| Ransomware, zero-day exploits, brute force, and uninstall protection | ✓ | ✓ |
| Browser Guard | ✓ | ✓ |
| Privacy VPN | ✓ | |
| – No-log VPN to protect your digital footprint | ✓ | |
| – 500+ servers in 30+ countries | ✓ |
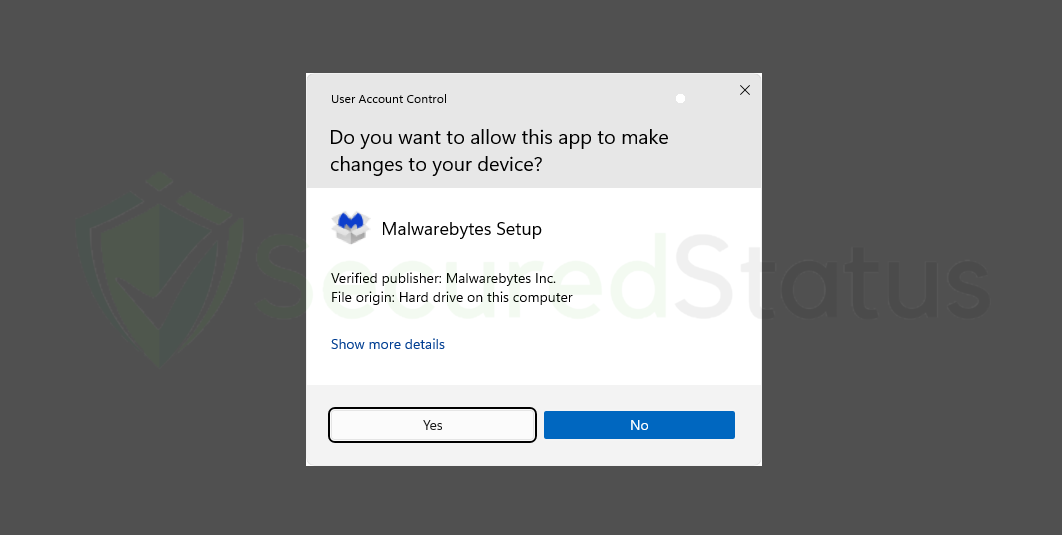
3. After selecting your preferred plan, click the Download button for the Malwarebytes anti-malware application. You should then receive a Thank You for Downloading message, and the application setup file (MBSetup.exe) will then be downloaded.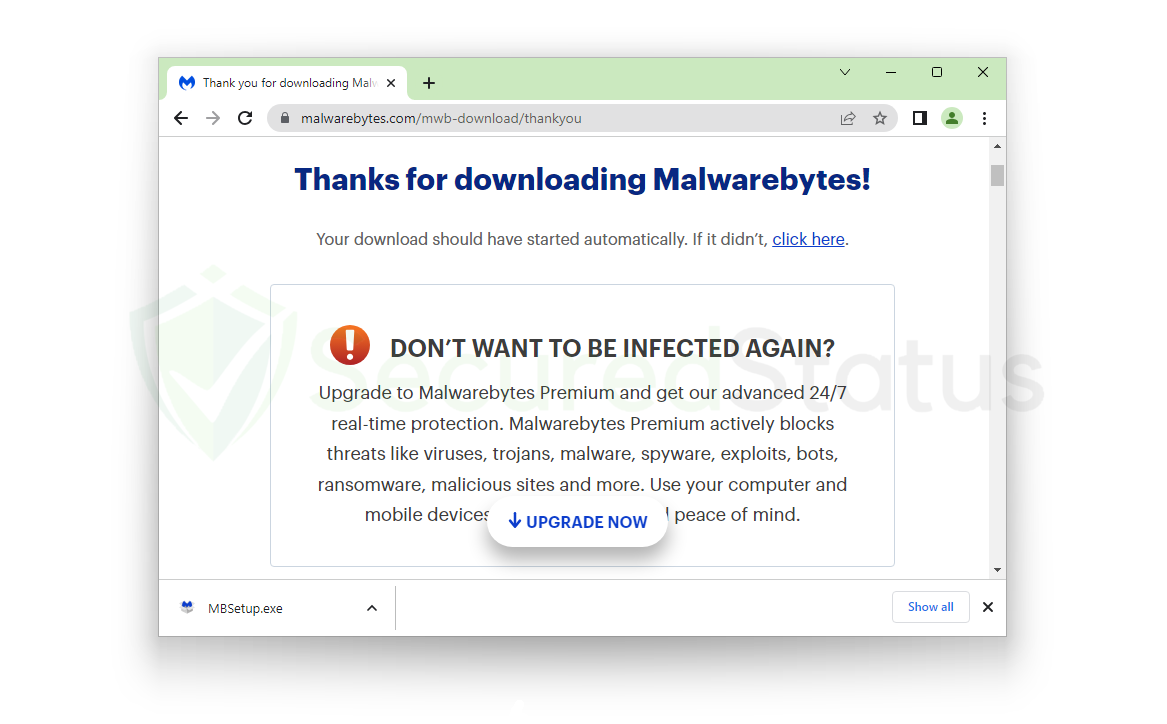 4. Once the setup file has downloaded completely, launch the executable software to start installing Malwarebytes on your computer. The User Account Control will then ask you if you wish to give the program Malwarebytes Setup permission to modify your device. Click Yes to continue, as it is necessary to do so in order to make sure the application is installed without issues.
4. Once the setup file has downloaded completely, launch the executable software to start installing Malwarebytes on your computer. The User Account Control will then ask you if you wish to give the program Malwarebytes Setup permission to modify your device. Click Yes to continue, as it is necessary to do so in order to make sure the application is installed without issues.
5. The Malwarebytes Setup process will then launch and display a welcome message and an Install button that must be clicked in order to begin the installation. If you are a tech-savvy individual, you can choose Advanced Options to install the application with additional customizations if you wish. But since doing the normal installation makes sure Malwarebytes does all the installation work for you, using the standard option is preferred.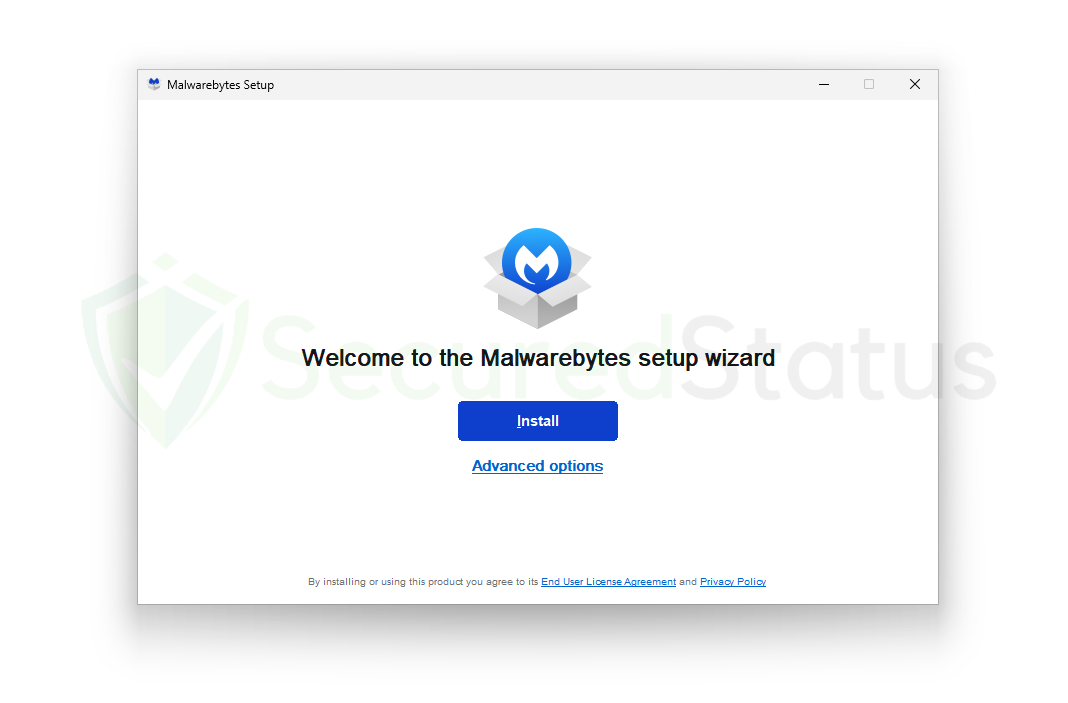 6. You will be taken to a product selection screen where you can choose how to use Malwarebytes on your computer before continuing with the installation. This is between personal use, such as for devices owned by you and your family, and My organization for office use, which may download a different version of Malwarebytes anti-malware developed specifically for businesses. But since you likely came here to get rid of spyware and safeguard your computer, simply choose the Me or my family option.
6. You will be taken to a product selection screen where you can choose how to use Malwarebytes on your computer before continuing with the installation. This is between personal use, such as for devices owned by you and your family, and My organization for office use, which may download a different version of Malwarebytes anti-malware developed specifically for businesses. But since you likely came here to get rid of spyware and safeguard your computer, simply choose the Me or my family option.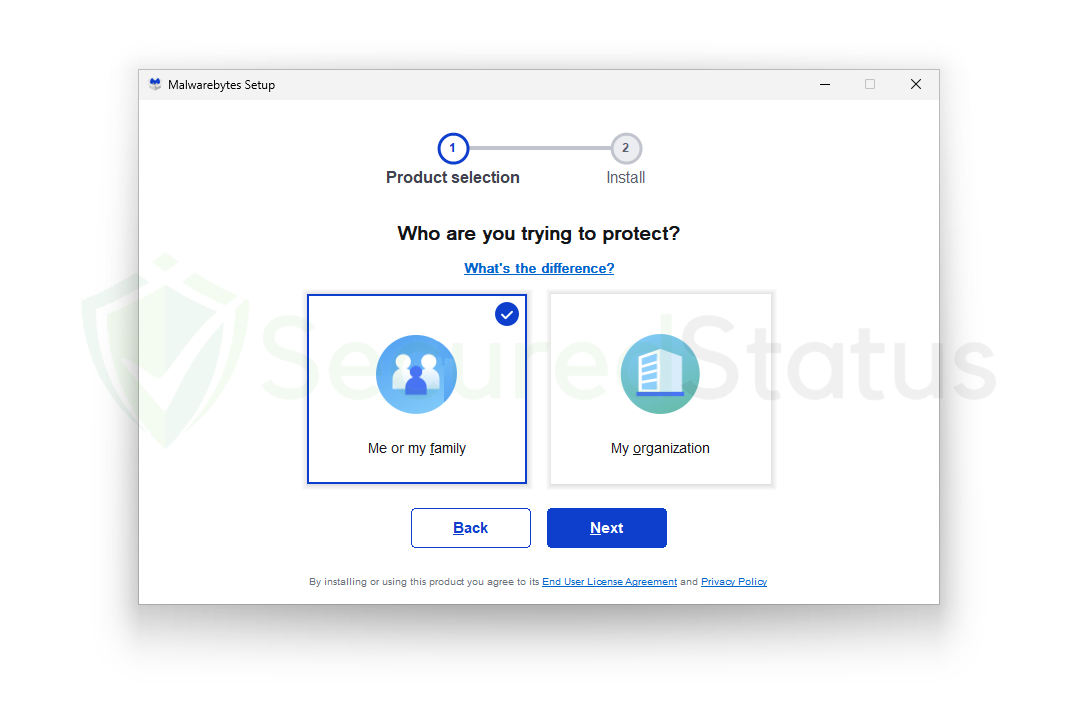 7. Malwarebytes anti-malware will start to install on your computer after you finish selecting from the product selection options. Depending on the hardware and speed of your computer, such as whether it is charging, in performance mode, or in battery saving mode, this could take a while. When downloading programs like antivirus and anti-malware, lagging and slowness are expected because these programs alter the security of the device.
7. Malwarebytes anti-malware will start to install on your computer after you finish selecting from the product selection options. Depending on the hardware and speed of your computer, such as whether it is charging, in performance mode, or in battery saving mode, this could take a while. When downloading programs like antivirus and anti-malware, lagging and slowness are expected because these programs alter the security of the device.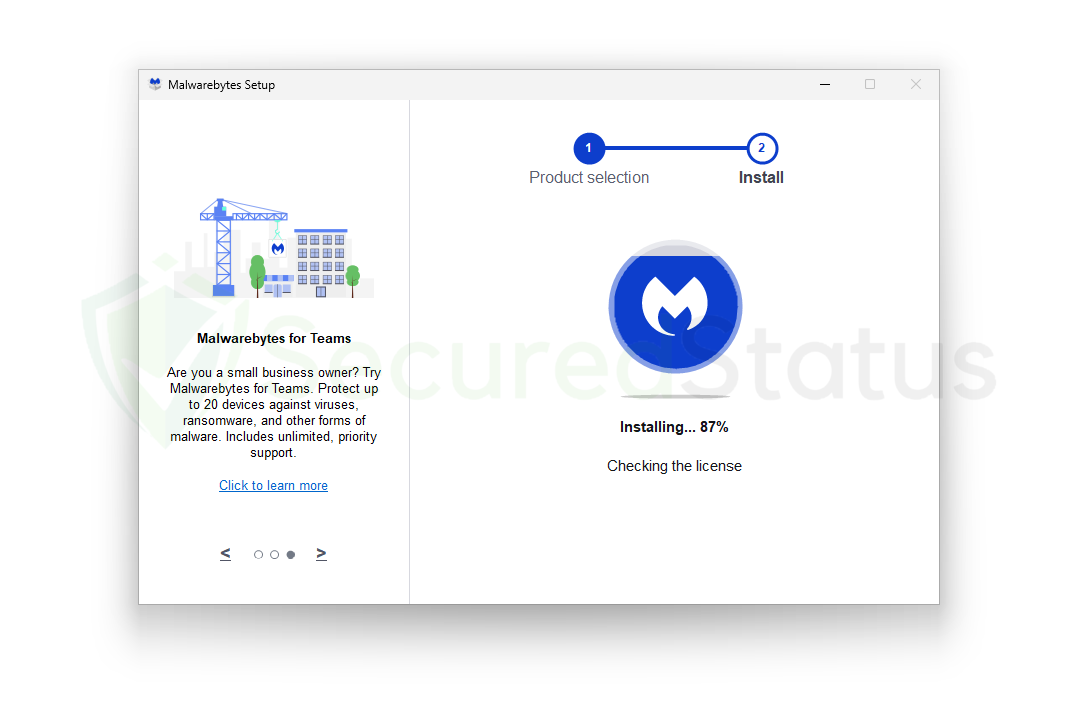 8. Malwarebytes is now prepared to scan your computer after the installation is complete, which is indicated by the message Install successful. To launch the Malwarebytes program and launch a scan, click on Done. If it didn’t open after you clicked the button, just look for it in the list of Windows applications and launch it manually.
8. Malwarebytes is now prepared to scan your computer after the installation is complete, which is indicated by the message Install successful. To launch the Malwarebytes program and launch a scan, click on Done. If it didn’t open after you clicked the button, just look for it in the list of Windows applications and launch it manually.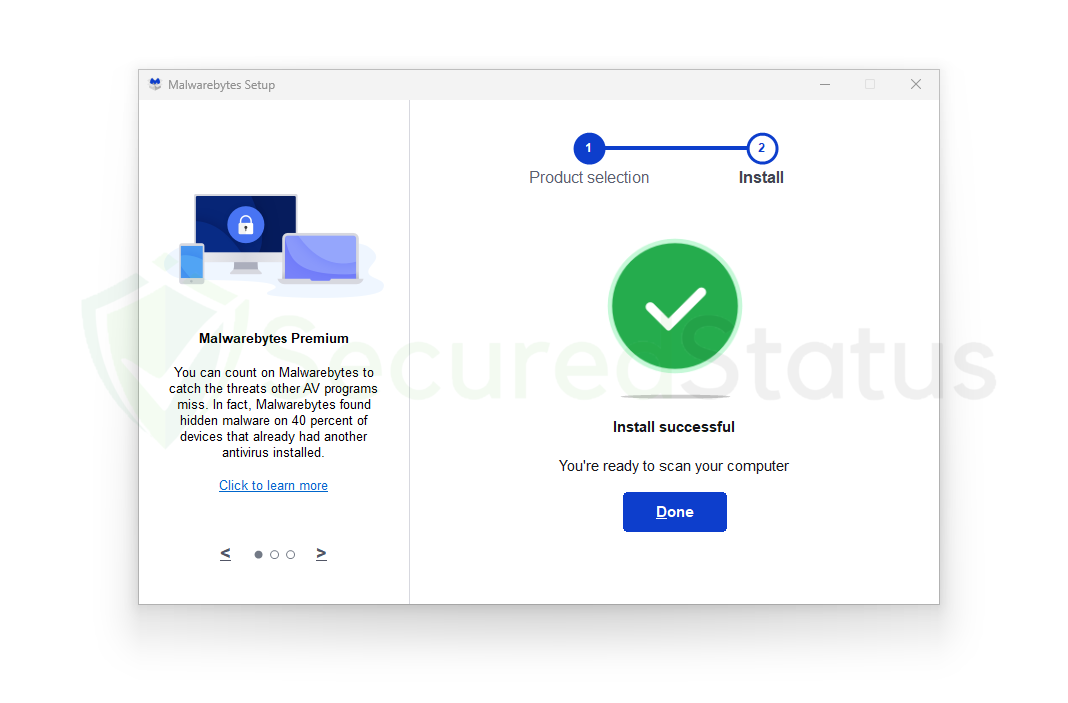 9. When the anti-malware program has finished installing and is open, a Welcome to Malwarebytes screen will appear. To use the program to search for malicious software and dangerous infections, click on the Get started button. This screen will only show up the first time you launch the program; it won’t show up again after that.
9. When the anti-malware program has finished installing and is open, a Welcome to Malwarebytes screen will appear. To use the program to search for malicious software and dangerous infections, click on the Get started button. This screen will only show up the first time you launch the program; it won’t show up again after that.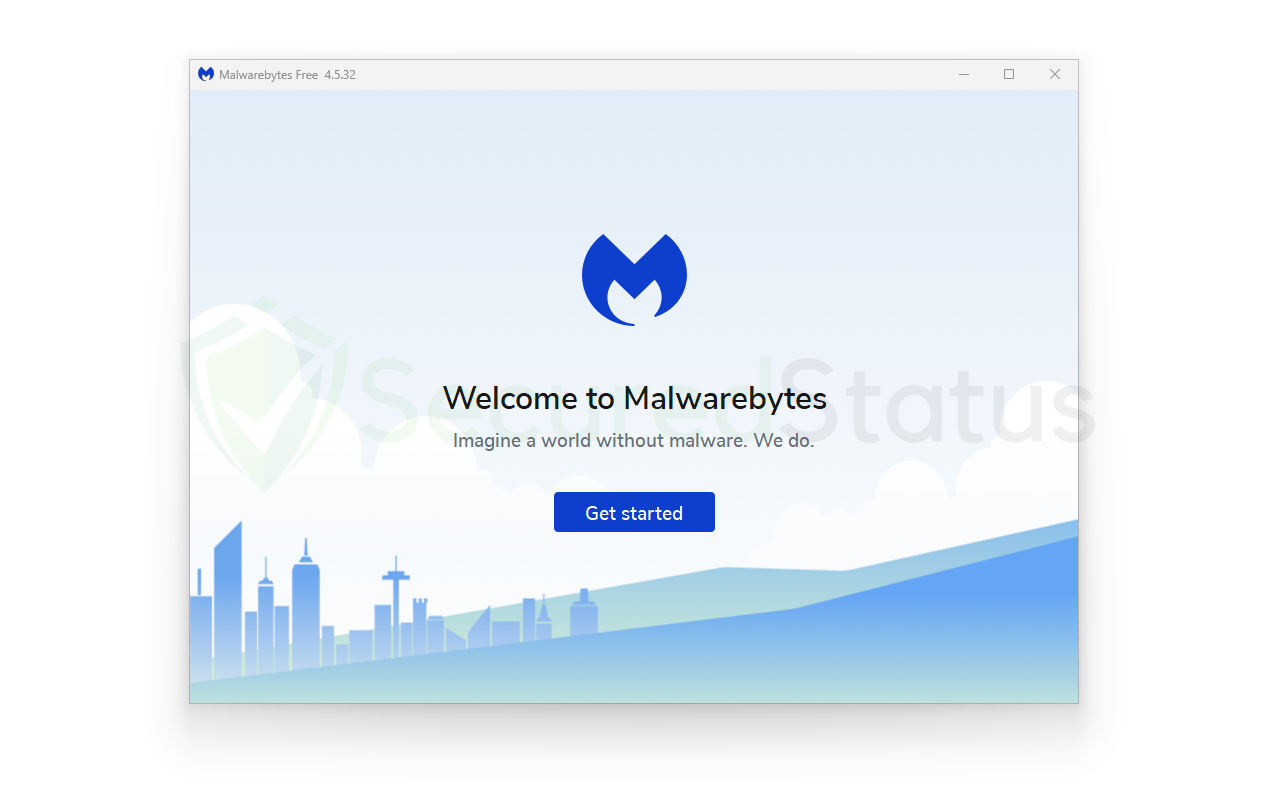 10. The next screen will display the features of Malwarebytes Premium, which will be available for a 14-day free trial period if this is your first time downloading the application. On the other hand, if you paid for the paid version, click on Activate subscription to start inputting the license code you were given. To continue without a subscription, click Maybe later.
10. The next screen will display the features of Malwarebytes Premium, which will be available for a 14-day free trial period if this is your first time downloading the application. On the other hand, if you paid for the paid version, click on Activate subscription to start inputting the license code you were given. To continue without a subscription, click Maybe later.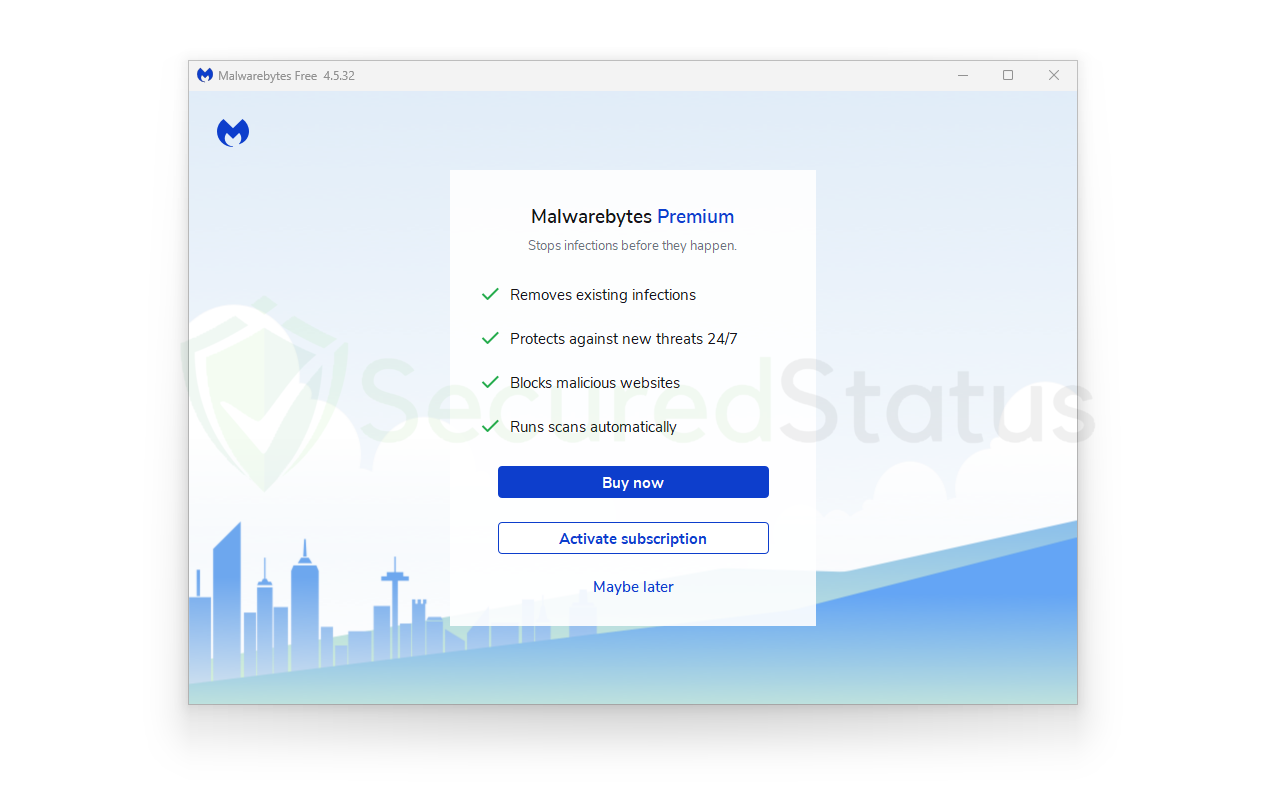 11. You will then be met with a 14-day Premium trial message if you opted for the free version. If you want to receive marketing emails and promotions from Malwarebytes, put your email address in the text box provided. When you’re ready to finish the welcome messages and start scanning and protecting your device, click Get started.
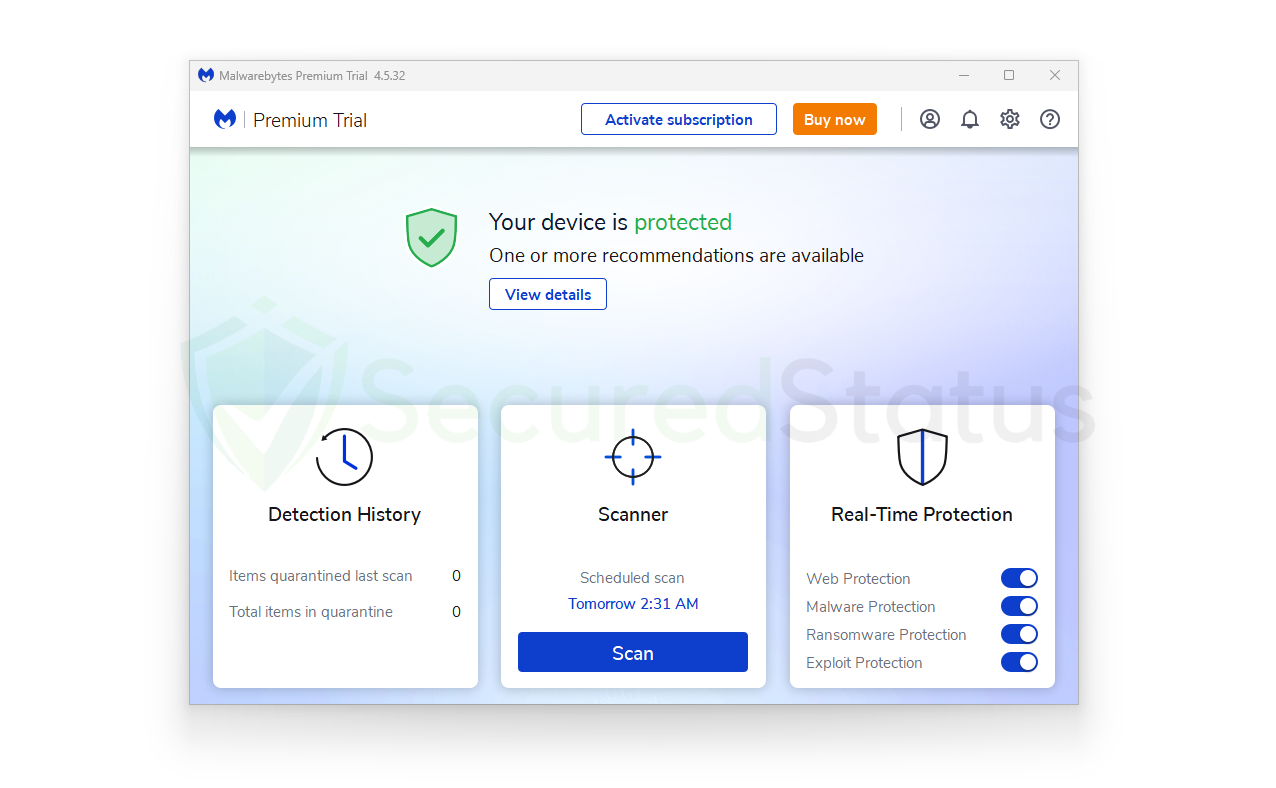
11. You will then be met with a 14-day Premium trial message if you opted for the free version. If you want to receive marketing emails and promotions from Malwarebytes, put your email address in the text box provided. When you’re ready to finish the welcome messages and start scanning and protecting your device, click Get started.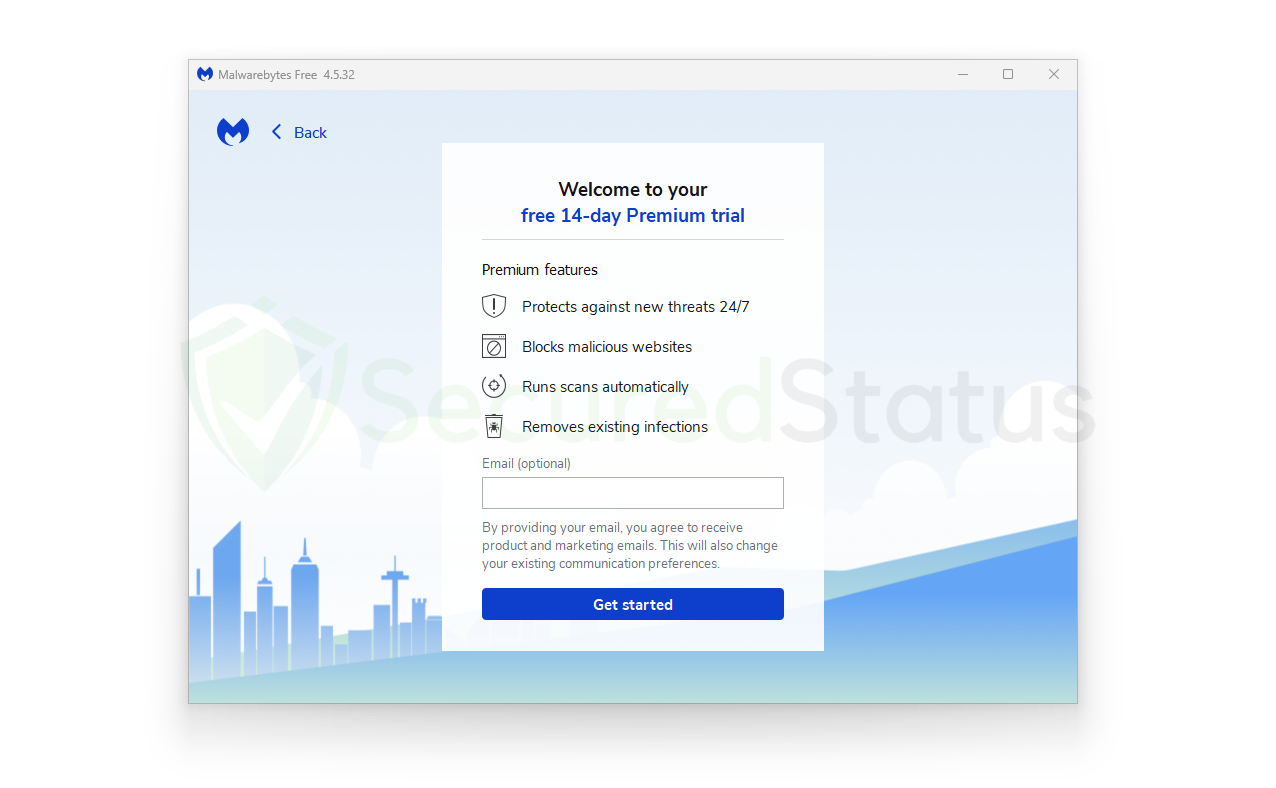 12. The primary software has a distinctive and straightforward user interface, and when you first use it, you will see three boxes. A Scanner for starting the computer’s scan, Real-Time Protection for turning on and off all-around security capabilities, and Detection History for deleting quarantined files after scanning, which is crucial and should not be forgotten.
12. The primary software has a distinctive and straightforward user interface, and when you first use it, you will see three boxes. A Scanner for starting the computer’s scan, Real-Time Protection for turning on and off all-around security capabilities, and Detection History for deleting quarantined files after scanning, which is crucial and should not be forgotten.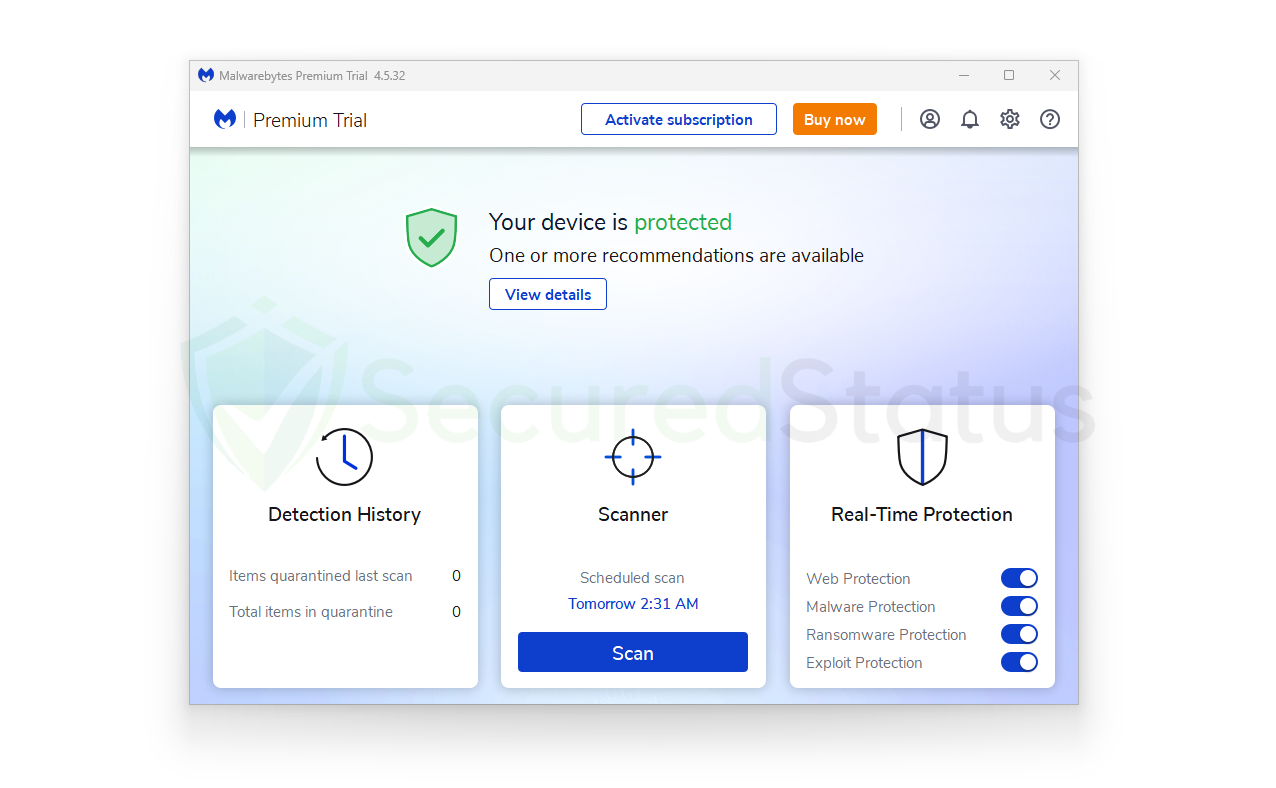 13. To start scanning for malware, click on the Scan button from the home screen. Malwarebytes should start scanning your computer for malware. It will search the memory, startup items, registry, and file systems, among other components. The amount of time it takes to complete the scan will depend on the processing speed of your computer and the quantity and size of the data you have on it.
13. To start scanning for malware, click on the Scan button from the home screen. Malwarebytes should start scanning your computer for malware. It will search the memory, startup items, registry, and file systems, among other components. The amount of time it takes to complete the scan will depend on the processing speed of your computer and the quantity and size of the data you have on it.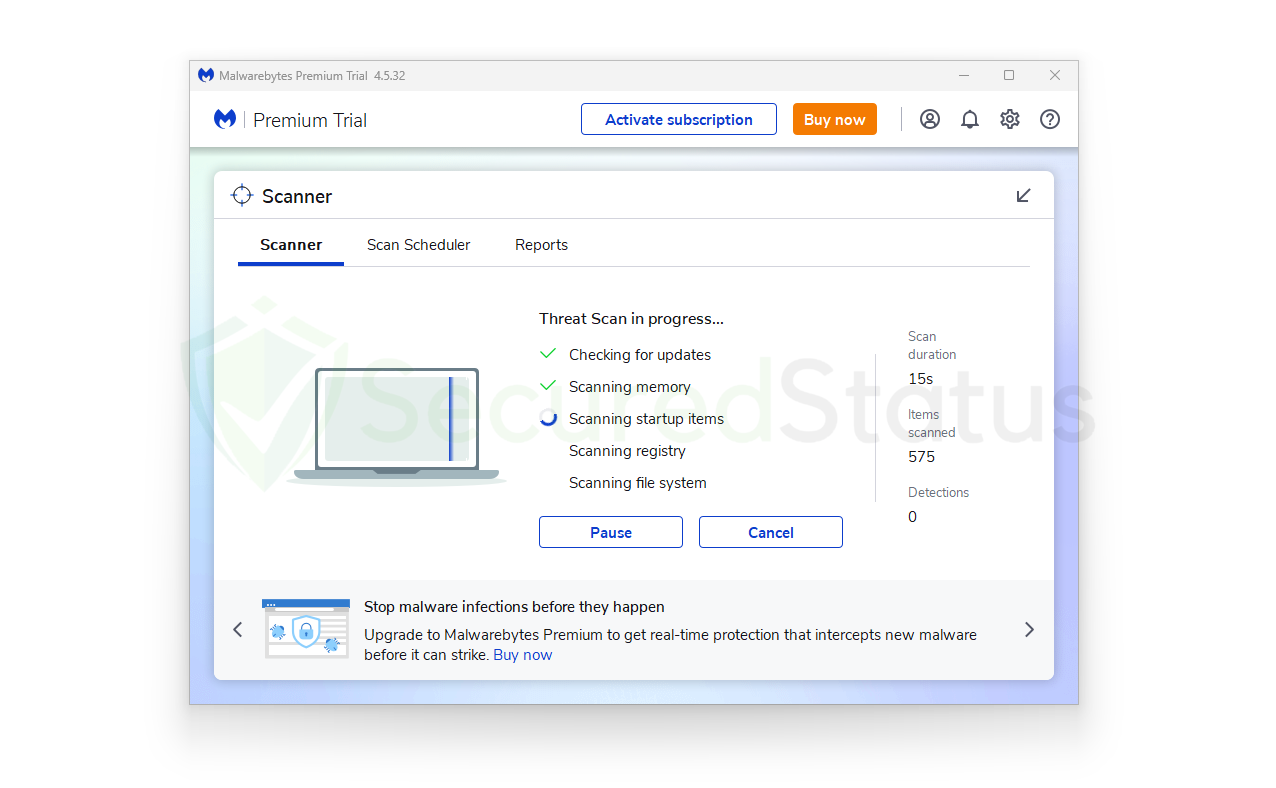 14. After the scan is finished, Malwarebytes will provide the results of the malicious threats it has discovered on the computer. It will be displayed together with its location and the detection name that Malwarebytes has identified it for, such as Generic.Trojan.Injector.DDS and etc.
14. After the scan is finished, Malwarebytes will provide the results of the malicious threats it has discovered on the computer. It will be displayed together with its location and the detection name that Malwarebytes has identified it for, such as Generic.Trojan.Injector.DDS and etc. 15. To remove dangerous files from the computer system and place them in the safe, protected quarantine zone of the anti-malware application so that they won’t influence or harm the computer again, select all the discovered files from the report and click the quarantine button.
15. To remove dangerous files from the computer system and place them in the safe, protected quarantine zone of the anti-malware application so that they won’t influence or harm the computer again, select all the discovered files from the report and click the quarantine button. 16. If the program asks you to restart the computer to complete the full system scan operation after you’ve quarantined the malware files, please do so because it’s crucial. The Malwarebytes software will launch after the restart and provide a notification indicating that the scan was successful.
16. If the program asks you to restart the computer to complete the full system scan operation after you’ve quarantined the malware files, please do so because it’s crucial. The Malwarebytes software will launch after the restart and provide a notification indicating that the scan was successful.
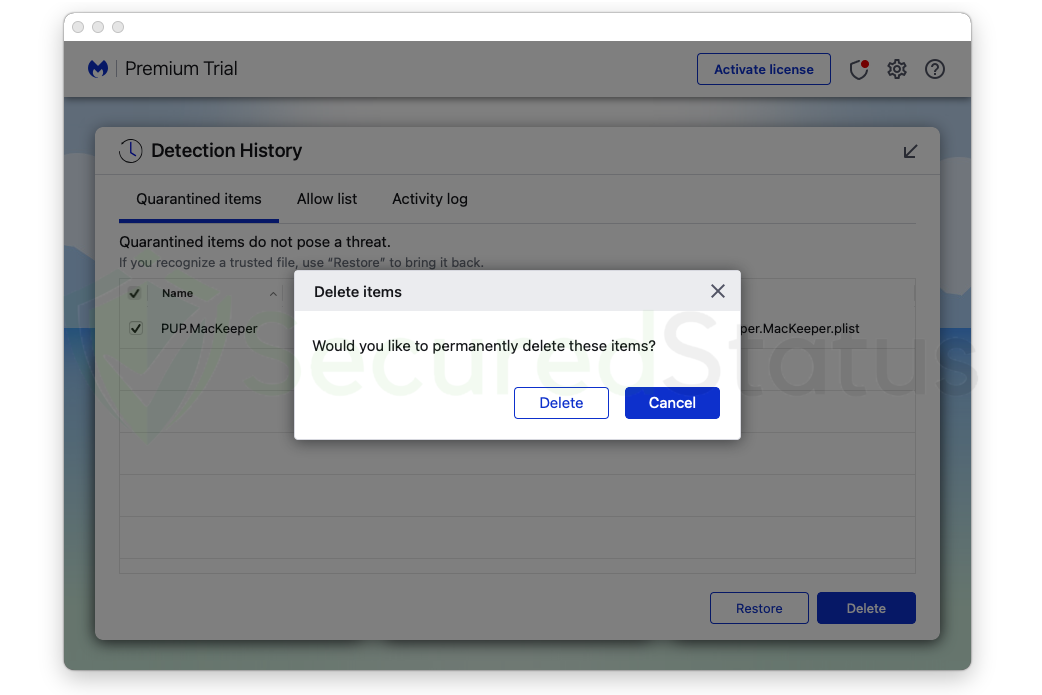
Note: Don’t forget to delete the quarantined files.
Malicious files must be thoroughly deleted in addition to being quarantined. It’s a frequent mistake for users to believe that after they click the quarantine button, everything is resolved. The malware is still present in the system; it has just been hidden in the quarantine folders of the program, even though its negative effects and malicious activities have been stopped. So, from the home screen, go to the Detection History and select all Quarantined objects, then click Delete to completely remove them.
The malware is still present in the system; it has just been hidden in the quarantine folders of the program, even though its negative effects and malicious activities have been stopped. So, from the home screen, go to the Detection History and select all Quarantined objects, then click Delete to completely remove them.
For Mac Operating Systems
The procedure is basically the same for Mac operating systems, but let us walk you through it to ensure that the program is installed properly.
1. To begin, click the button below to go to the Malwarebytes official website and download the malware removal tool for the Mac OS. Additionally, you can directly access their website, Malwarebytes.com via Safari or your default web browser. (Please avoid misspellings since online criminals occasionally use them to direct customers to dangerous websites.)
2. If you opt to purchase the paid edition of the application, be sure to check the pricing, as there are several plans offered. To better secure your online behavior, there is also a plan with additional VPN software for all of your devices.
If you think that paying a small fee is worthwhile in exchange for better protection, you can opt for the paid version. However, should you not want to spend a dime, Malwarebytes offers a 14-day free trial of its premium features, so you can test it out first. The prices as well as features for each plan are listed in the table below.
| Features Available For Mac | Premium Version (Plan starts at $44.99) | Premium + Privacy VPN (Plan starts at $59.99) |
|---|---|---|
| Around the clock real-time protection | ✓ | ✓ |
| Malicious websites and phishing protection | ✓ | ✓ |
| Ransomware, zero-day exploits, brute force, and overall protection | ✓ | ✓ |
| Browser Guard for Safari and other Browsers | ✓ | ✓ |
| Malwarebytes Privacy VPN | ✓ | |
| – Complete transparency as it does not log data | ✓ | |
| – 500+ servers in 30+ different countries | ✓ |
3. Click the Download button for the Malwarebytes anti-malware program after choosing your preferred plan. A Thank You for Downloading notice should appear after that, and the application setup file (Malwarebytes-Mac.x.xxx.x.pkg) will then be downloaded.
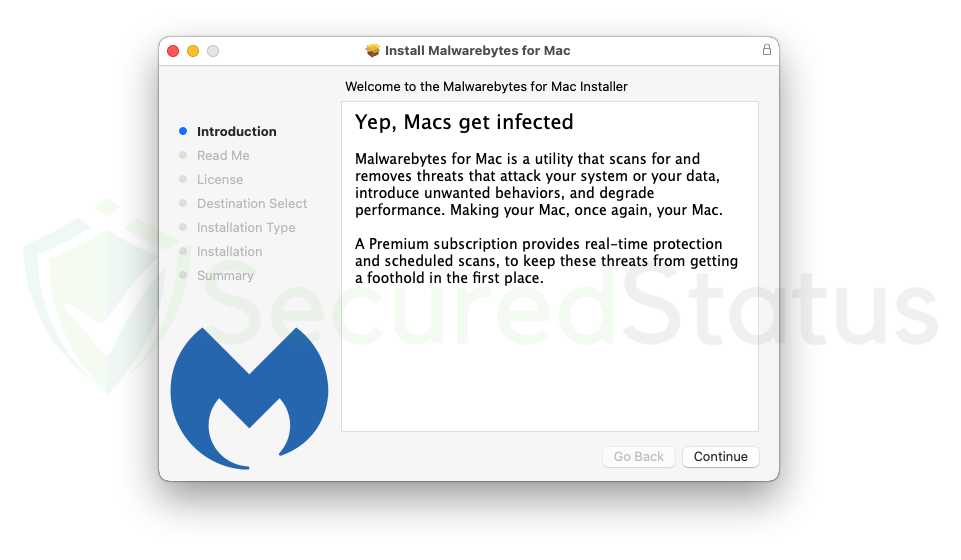
4. Run the setup package file after the application has finished downloading, and it should direct you to install Malwarebytes for Mac. There are numerous steps in the setup wizard, the first of which states that all Macs are susceptible to malware. To proceed, click the Continue button in the application’s lower right corner.
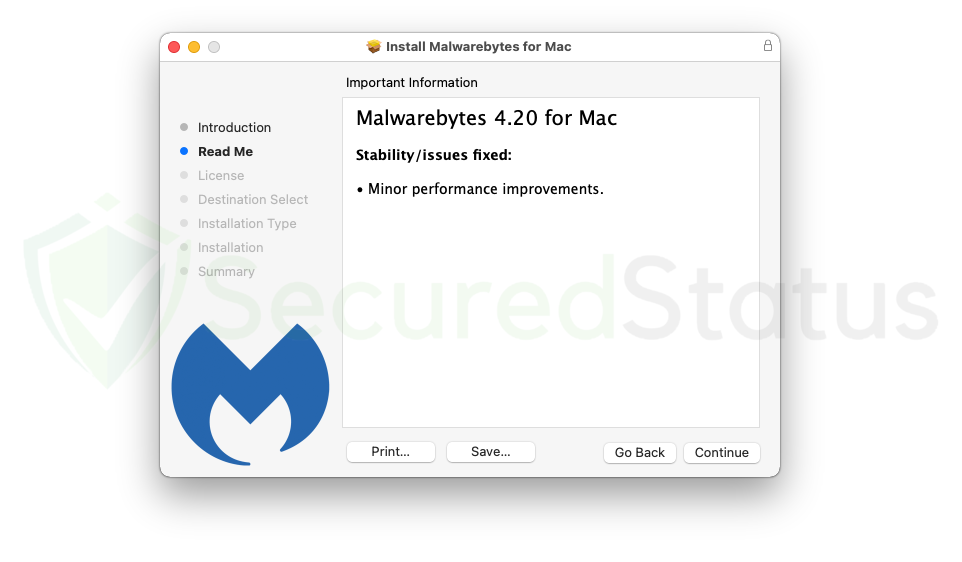
5. A read-me containing the key details of the application would appear in the next step. Depending on the version you’re downloading, it might display new features that come with it, or it might just be stability and bug fixes for minor improvements. To move on to the next step, click Continue yet again.
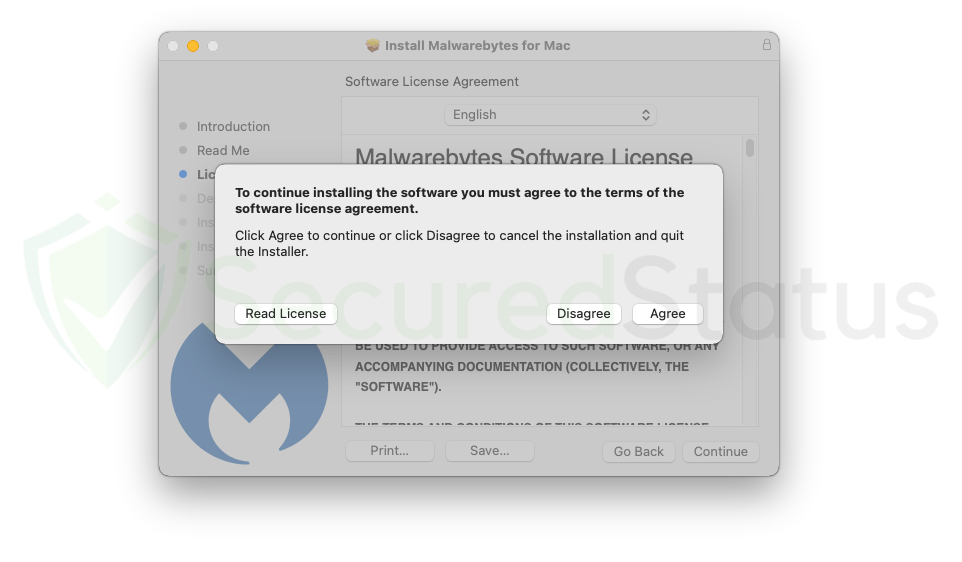
6. By continuing to install Malwarebytes, you agree to the terms of the software licensing agreement, as seen in the image below. Users are entitled to read this document because every application has one, and users must accept it before using the application. To move on to the next stage, select Agree.
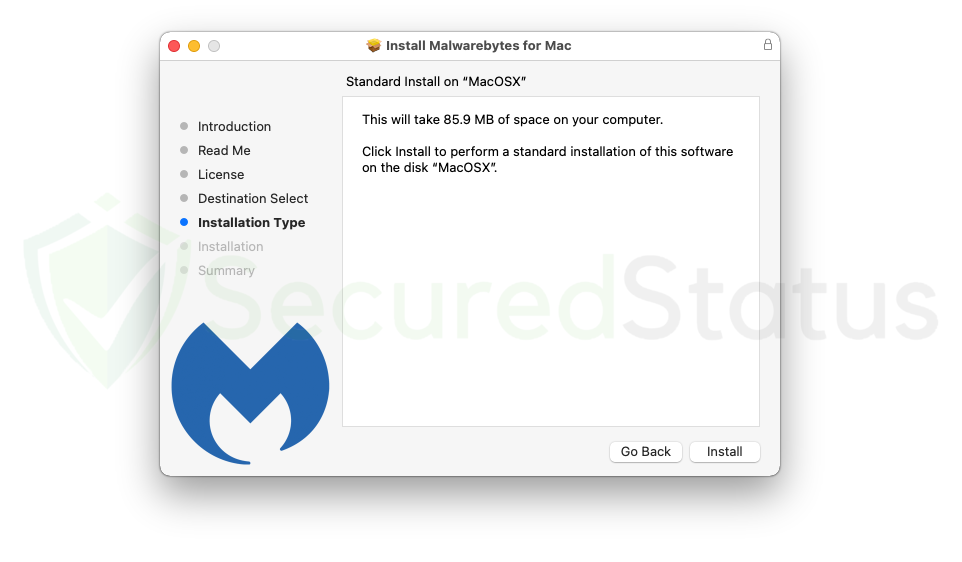
7. You will be informed onscreen before starting the installation process that the application will use a small amount of storage space on your Mac. To ensure a trouble-free installation of Malwarebytes, make sure you have sufficient available space. If you think you have enough storage, click Install to start the program’s installation.
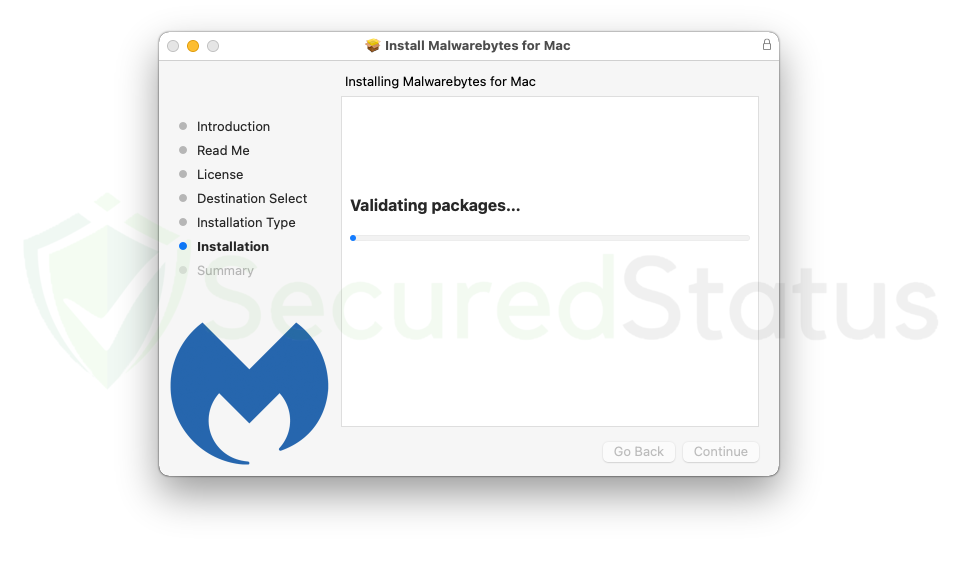
8. The computer will then start to install Malwarebytes. Depending on the available space and how fast your machine is, this could take some time. Installing Mac OS on older Mac computers may take longer than on newer versions and flagship models. In any case, please wait while the application installs.
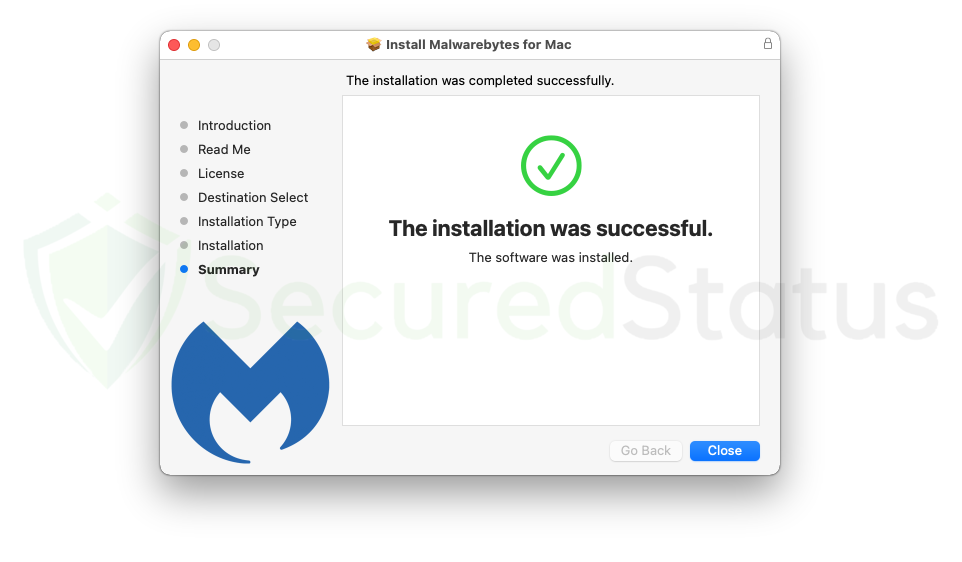
9. When the Mac system’s installation of the application is complete. The summary tab will then appear, stating that Malwarebytes was set up successfully and that the installation process was successful. To launch Malwarebytes and begin scanning your computer for infection, click the Close button.
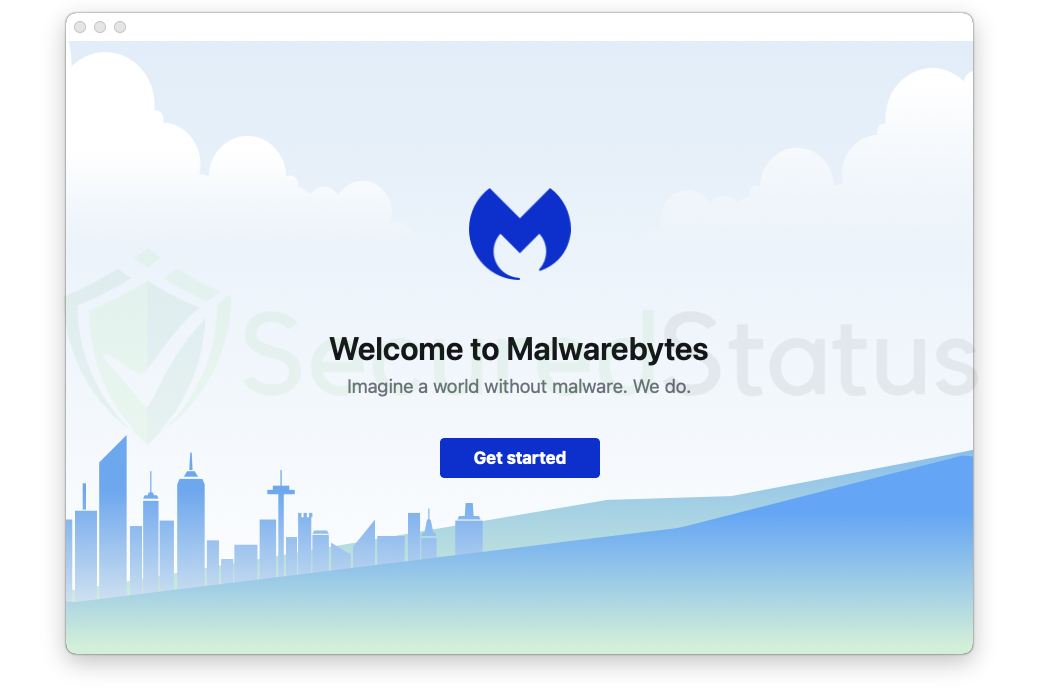
10. After the setup process has been closed, Malwarebytes will launch on the computer. When the setup wizard is finished, you can select to delete it since it is no longer needed. Click Get started on the main Malwarebytes program to start the preparations for utilizing the program. Only when you download the application for the first time will this appear.
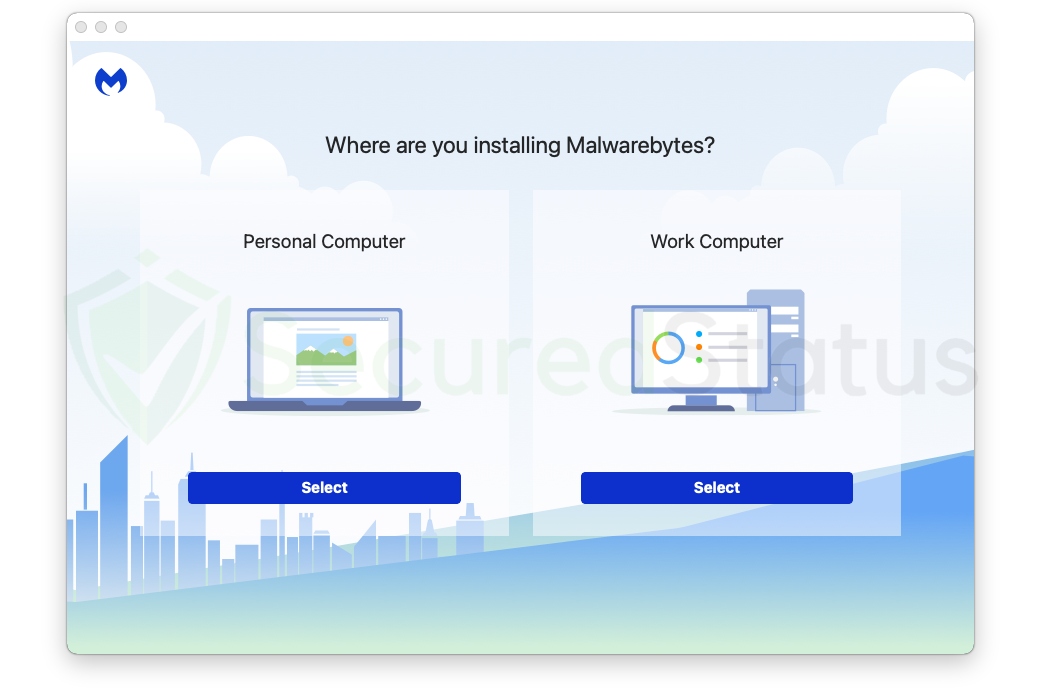
11. You will be directed to a screen where you can choose which computer you want to install Malwarebytes on. This is between Work Computer for office usage, which may download a different version of Malwarebytes anti-malware created exclusively for businesses, and Personal Computer, such as for devices owned by you and your family. However, because you probably came to this page to remove spyware and protect your computer, simply choose that you are installing it for your Personal Computer.
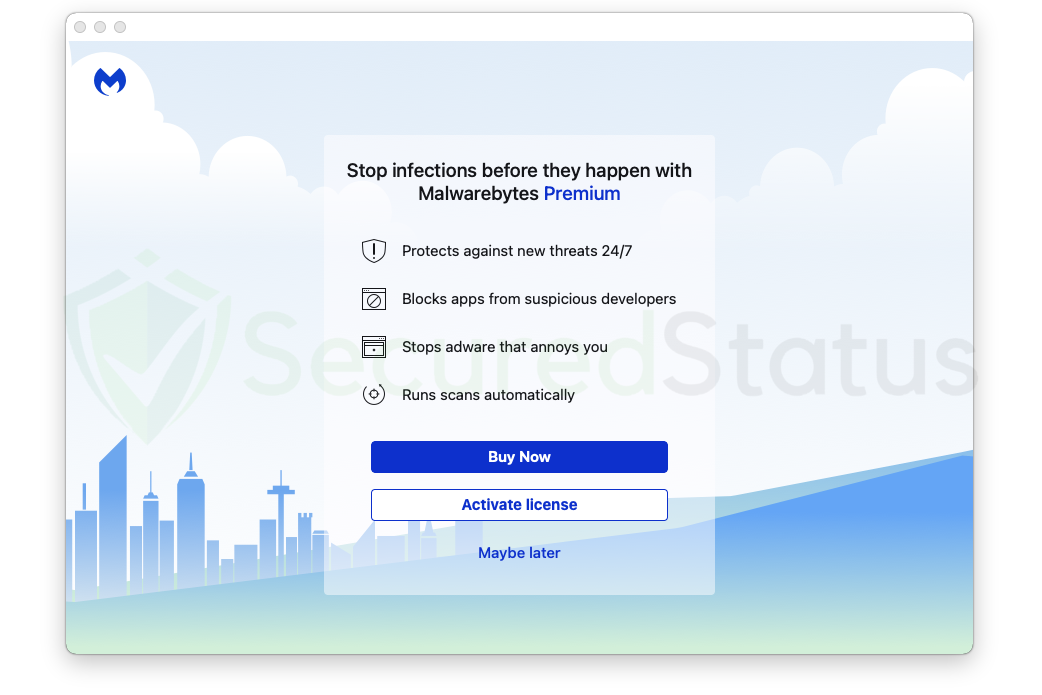
12. The features of Malwarebytes Premium will be shown on the following screen, and if this is your first time downloading the program, a 14-day free trial will be given. On the other hand, if you purchased the paid version, click on Activate subscription to begin entering the license code that was provided. Click Maybe later to continue without a subscription.
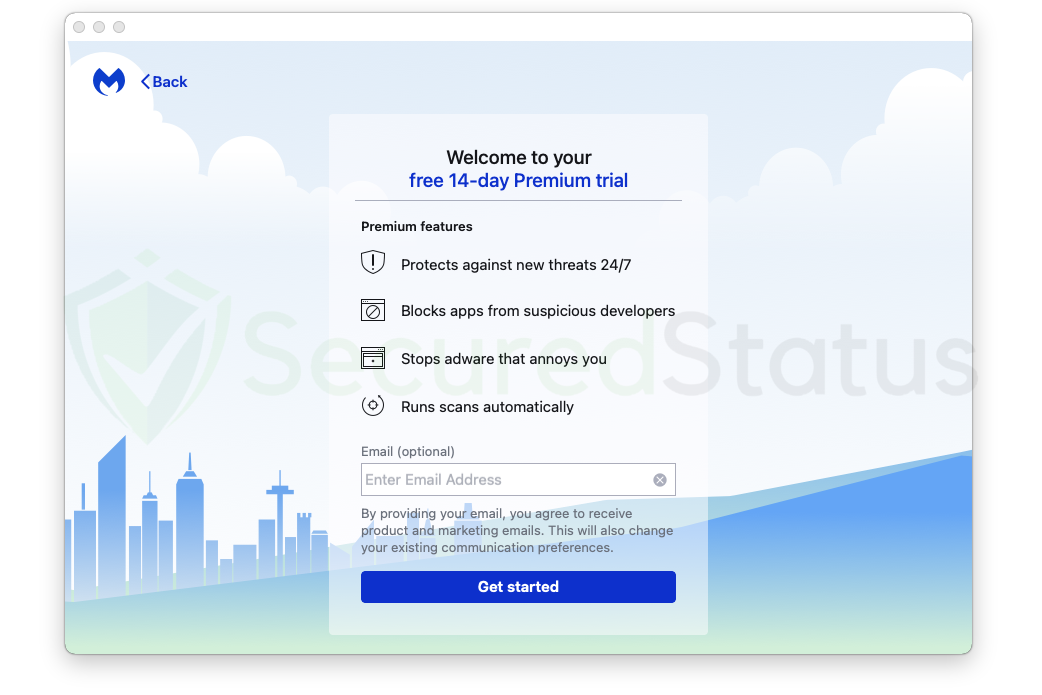
13. If you selected the free version, you will then get a notice offering a 14-day Premium trial. Enter your email address in the space provided if you want to receive marketing emails and promotions from Malwarebytes. Click Get started when you’re ready to finish the welcome messages and begin scanning and protecting your device.
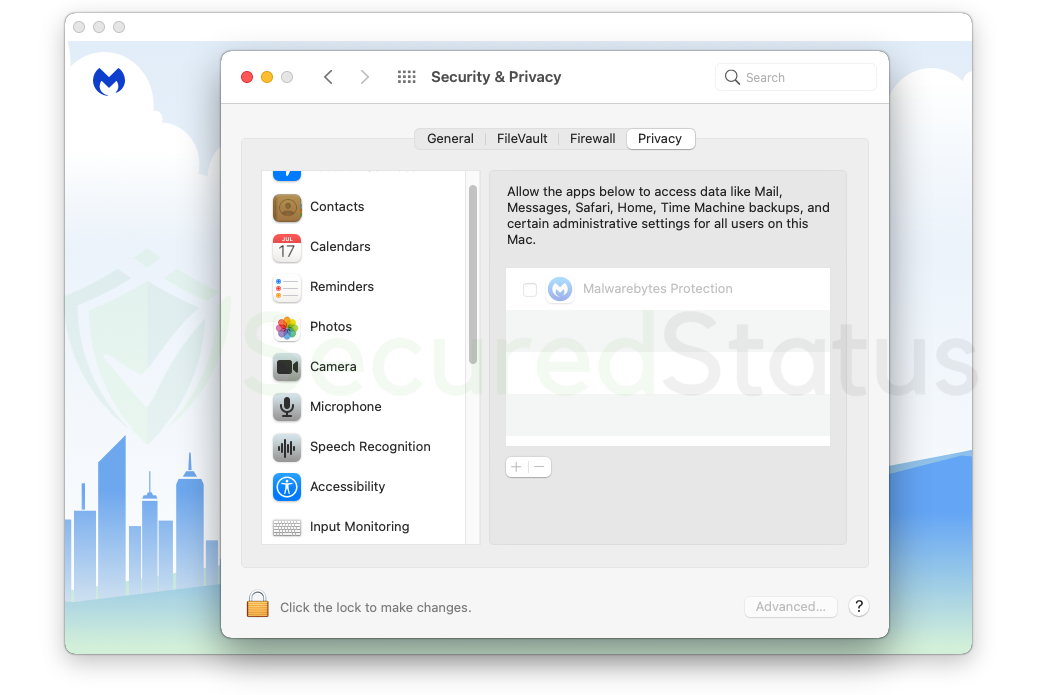
14. You will then be prompted to grant Malwarebytes full disk access. This is crucial since Mac OS is strict about granting apps access to the computer. The anti-malware program requires this permission in order to scan all of the system’s contents. To do this, click the Open Preferences button, which will launch the settings immediately.
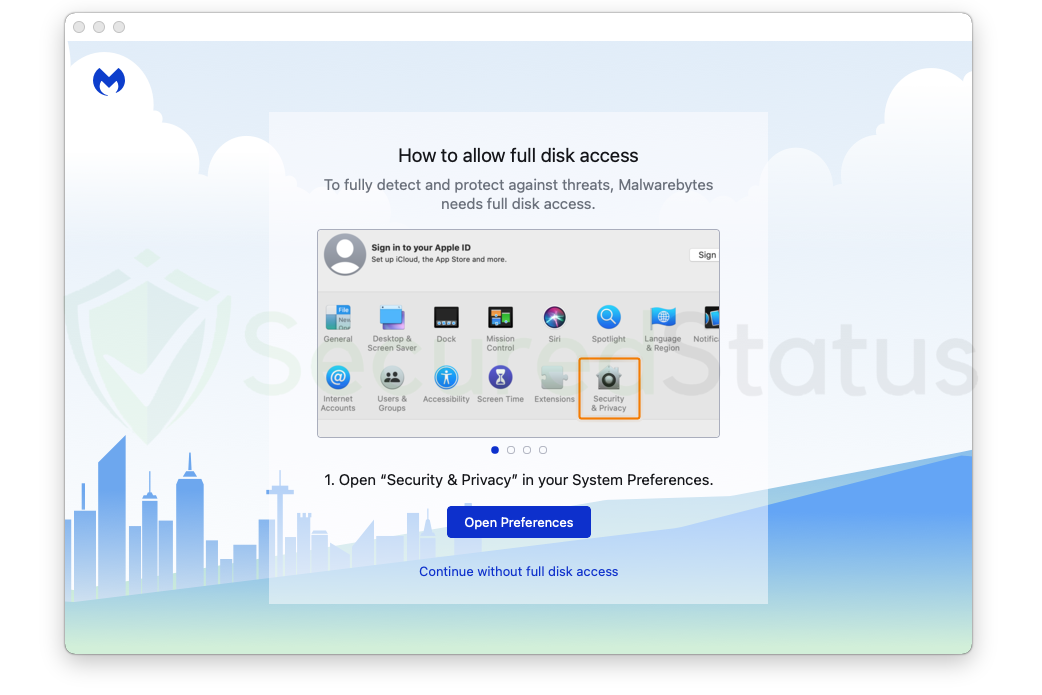
15. When the Security & Privacy window opens, it will immediately direct you to the Privacy tab, where you may make the necessary changes. To alter the authorization of Malwarebytes, click the lock at the bottom left of the window, unlock it, and begin making changes.
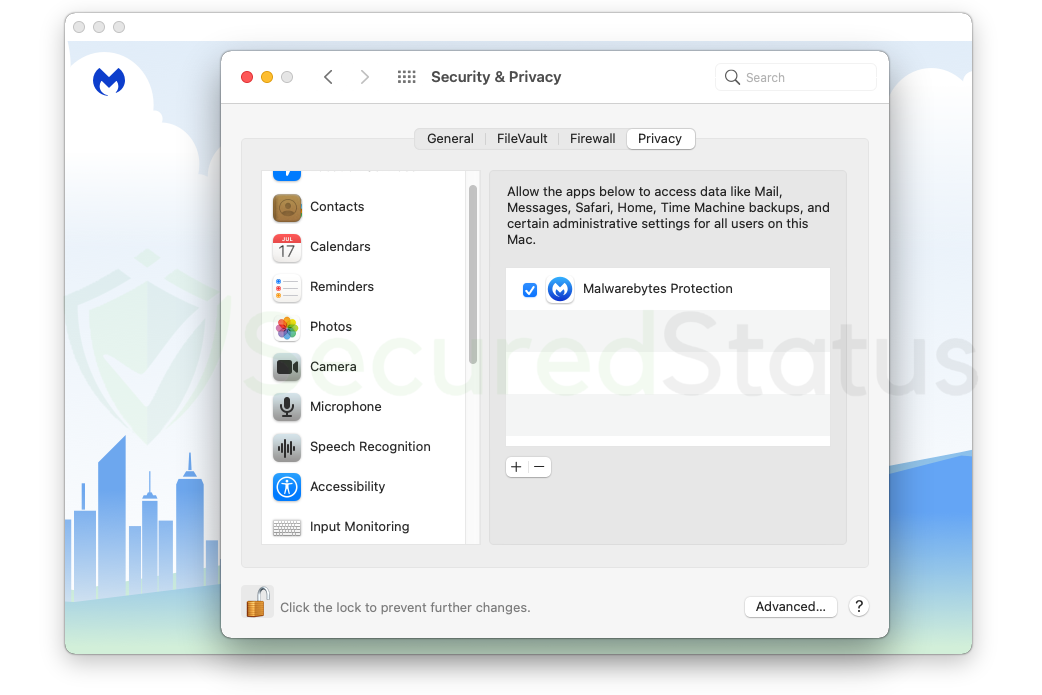
16. You will see that the checkmark in the box near the application has been unlocked. Simply check the box to give Malwarebytes permission to access the disk and perform a deeper scan for malware. After reviewing the program, click the lock once more to save the changes and prevent further alterations.
17. The main program of Malwarebytes will appear after completing the aforementioned procedures. When you initially use the main software, you will see three boxes due to its distinctive and simple user interface. A Scanner for initiating the computer’s scan, Real-Time Protection for enabling and disabling overall security features, and Detection History for erasing quarantined files after scanning, which is an important step that shouldn’t be overlooked.
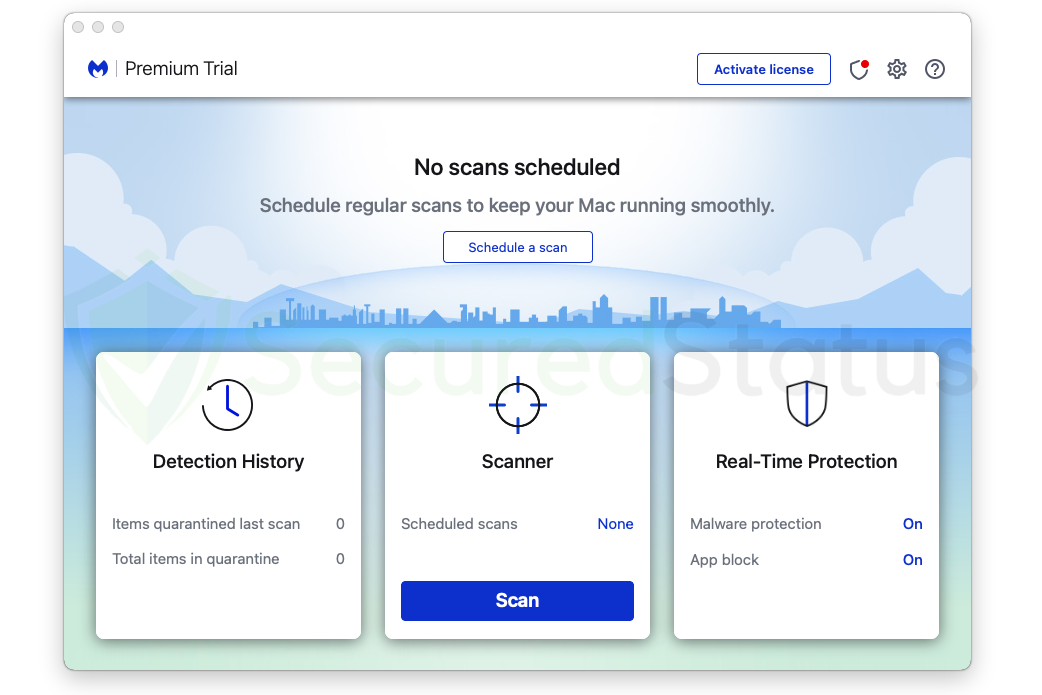
18. From the home screen, select the Scan button to launch a malware scan. Your computer should now begin to be scanned for infections by Malwarebytes. Along with other components, it will search all of your disk files if you gave it permission to do so. Please be patient while the application scans; depending on how many files are on the computer, this process can take a long time to complete.
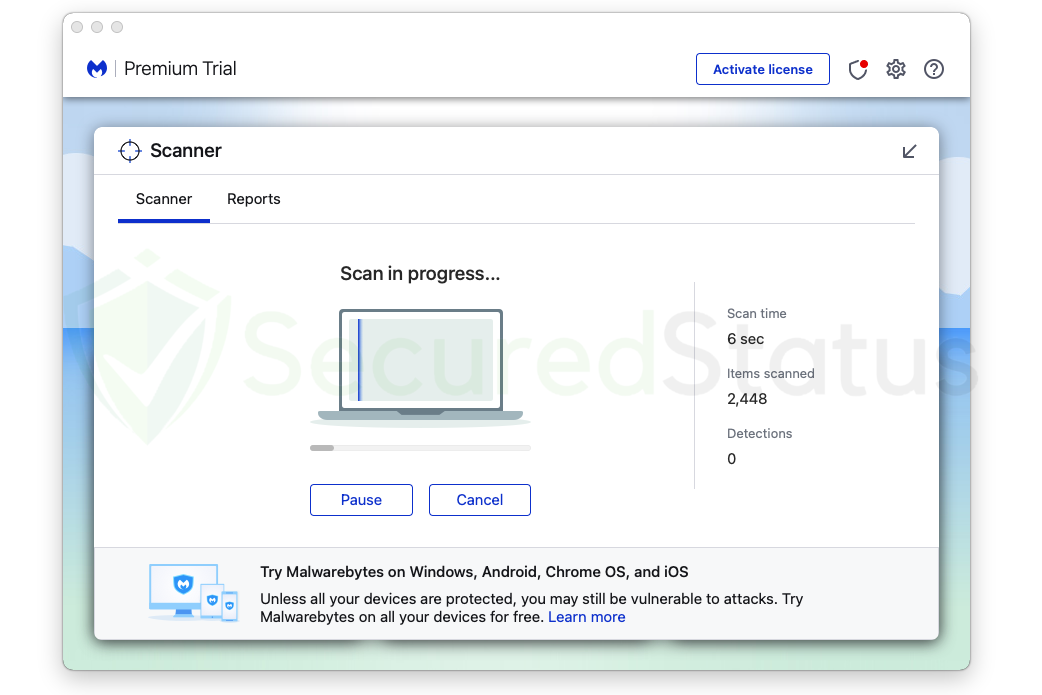
19. Malwarebytes will provide the results of the malicious threats it has found on the computer after the scan is complete. It will be shown along with its location and the detection name that Malwarebytes has assigned to it, such as PUP.Adware and other similar names.
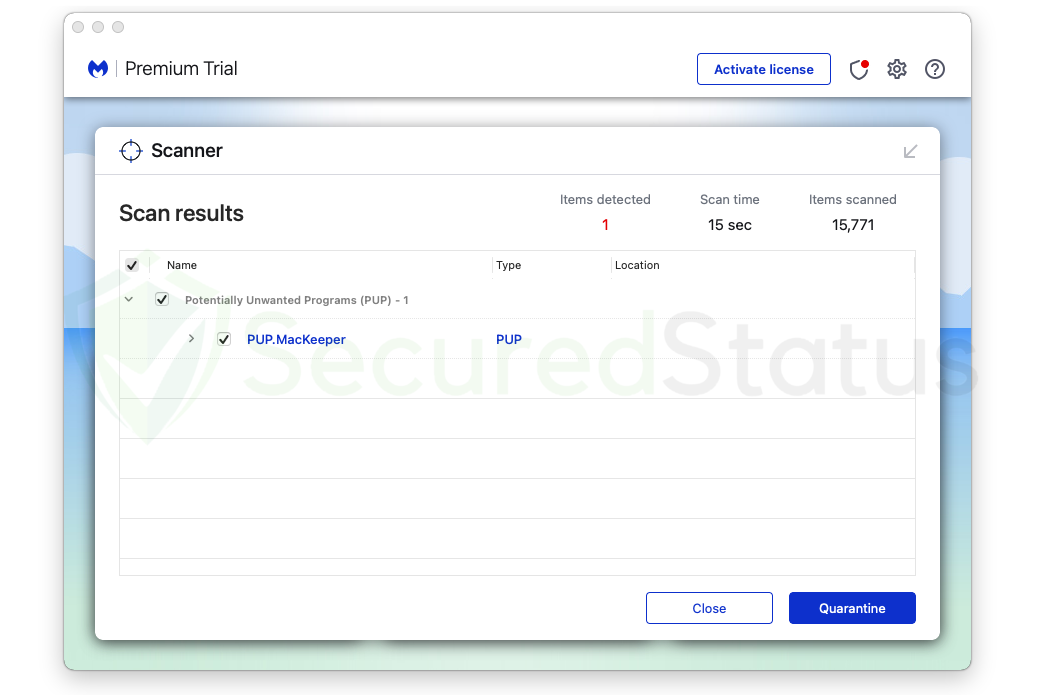
20. Select all the detected files from the report, then click the Quarantine button to remove harmful files from the computer system and put them in the anti-malware program’s secure quarantine area where they won’t affect or harm the Mac system again.
21. After you’ve quarantined the infected files, if the program asks you to restart the computer to finish the system scan, please do so because it is important. After the restart, the Malwarebytes program will run and send a message that the scan was successful.
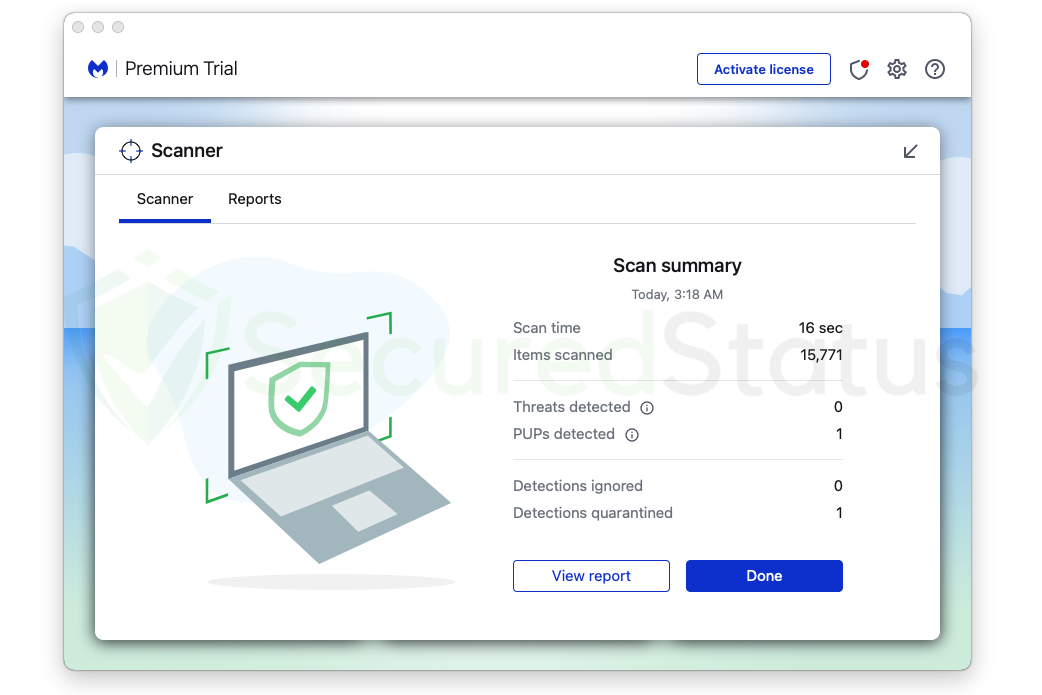
22. The Malwarebytes application’s quarantine area now contains the malware that was previously on the computer. To completely remove it from the system, go to the Detection History tab on the home screen, select all Quarantined items, and then click Delete.
Every piece of malware and computer virus on your computer has been successfully eliminated. You may rest assured that they won’t reappear because Malwarebytes offers a free 14-day premium trial so you can use it to stop malware from infiltrating your machine.
Malwarebytes offers free malware detection and cleanup, but its premium editions also come with real-time protection that keeps your computer secure at all times. Although we advise using the premium trial, if you find it beneficial, you are free to buy the complete version.
Frequently Asked Questions (FAQs)
Here are the most frequent queries concerning Malwarebytes Anti-Malware that users may have before downloading the application. We have also provided answers to these queries that we happen to have answered since we have tried and tested the application.
How long can I use Malwarebytes for free?
You can use the Malwarebytes application for free for as long as you like, and we are happy to mention this. The 14-day trial of Real-Time Protection, which ensures your computer is protected throughout the day without the user noticing, is the only thing with a time limit.
However, even once the trial is over, the primary application, which is to find and remove malware, will still be available and can be used indefinitely. We assure you that it won’t stop working and won’t demand payment for its removal features. You may simply launch Malwarebytes and let it get rid of malware for you once more if you come across one.
Is Malwarebytes better than Windows Defender?
Since Malwarebytes has so many more capabilities to offer when it comes to removing malware, it is always preferable to Windows Defender, which is a built-in program.
However, since that is the case for removing malware, Windows Defender may have some advantages when it comes to securing your computer all-around since it is created by the operating system itself.
Instead of using it as a comparison, you should utilize both. While Malwarebytes is free to scan for malware, Windows Defender is already a solid alternative for overall computer protection and would not cost you any money to use it.
Consider Windows Defender as your primary security, and Malwarebytes as your secondary scanner and second line of defense. You will have robust computer security when these two programs are together.
Is there a good alternative to Malwarebytes?
One program stands out as an alternative to Malwarebytes Anti-Malware that offers good protection with even more features: Kaspersky Antivirus. It is a good alternative, and it also tops our list of recommendations due to its impenetrable defense against computer viruses because it is an antivirus program.
Kaspersky Antivirus is also superior to Windows Defender because it has been defending users and enhancing their protection since 1997, long before the internet was a thing.
Kaspersky will do a decent job with that with its many helpful features, and it would not slow down the computer as much if you do not like Malwarebytes or do not want it as your first line of defense against malware.
How trusted is Malwarebytes Anti-Malware?
Malwarebytes is a highly regarded tool that has consistently performed at the top of tests for malware detection. Malwarebytes Endpoint is used by many organizations to safeguard their security against dangerous hackers, and it is regarded as a leading cyber security solution by many industry experts.
Millions of users use it worldwide. It is superior to the majority of antivirus products and does not employ dubious strategies, like displaying fake alerts, to get users to install their software. The malware removal feature also comes with no cost, and in addition to that, they also give a free trial after installation so you can see for yourself how it fares against malware.
