It’s possible that you’ll come upon an old, disused computer or other gadget from a long time ago and recall that it once had malware on it.
Another illustration would be if you purchased a used device that had a history of malware. The concern is if the infection inside the system shuts off or expires after a prolonged period of inactivity.
Users do not want a virus attacking their device unexpectedly one day as a result of an old infection that has been within the device for a very long time because malware, in general, is quite destructive.
Contrary to a perishable object with a fixed shelf life, malware can continue to work indefinitely unless it is identified and eliminated by security software or manually by a user, which is why it is crucial to understand that malware does not intrinsically “expire.”
But it’s crucial to remember that malware from the past wouldn’t have the same dire effects it did in the past because operating systems like Windows and Mac OS have continued to receive updates and security patches ever since and have strengthened their defenses against malware attacks.
Can Old Malware Versions Still Cause Damage?
For instance, as outdated operating systems and software programs are phased out and replaced with more secure versions, malware that is developed to target them may become less effective or stop working completely.
Since some malware is engineered to take advantage of particular flaws or outdated systems, it will not stand a chance against today’s computers. Not unless the device’s operating system was left out-of-date and hasn’t been updated since.
Another illustration would be outdated malware like trojans, keyloggers, and stealers that need a server connection to send the data they have intercepted or stolen to. It may also be referred to as a command and control server, which is what the hacker uses to take advantage of the infected computer through a malicious application via their server
The old malware server would have been abandoned if it had existed years ago, and the hackers would have developed a new program to keep up with the system’s security patch. In other words, obsolete malware will be regarded as useless and will no longer function since it was abandoned by cyber criminals long ago.
Malware can also be programmed to shut down or destroy itself after a certain period of time. When an attacker wants to minimize exposure and the chance that they will be discovered, they typically use this type of malware in targeted attacks.
Maintaining solid cybersecurity habits, such as using strong passwords, periodically scanning systems with updated security software, and maintaining software and operating systems up to date are the best ways to protect against malware. In conclusion, it is inaccurate to argue that malware “expires”; it might become outdated or self-destruct.
How to Remove Old Malware from System
Older versions of malware may not expire, as we’ve already explained, and the only way to completely remove it is to have it identified by antivirus software or manually deleted by the user.
To remove any sort of malware from the system we propose to use Malwarebytes Anti malware since it has the best detection rate amongst other products in the field.

Malwarebytes also offers a free 14-day trial when you download it for the first time, so you might want to use the remaining time of the trial to test out the premium features.
1 Click the button above to download the latest version of Malwarebytes Anti-malware.

2 Open the installation file after the download and follow the procedure shown.
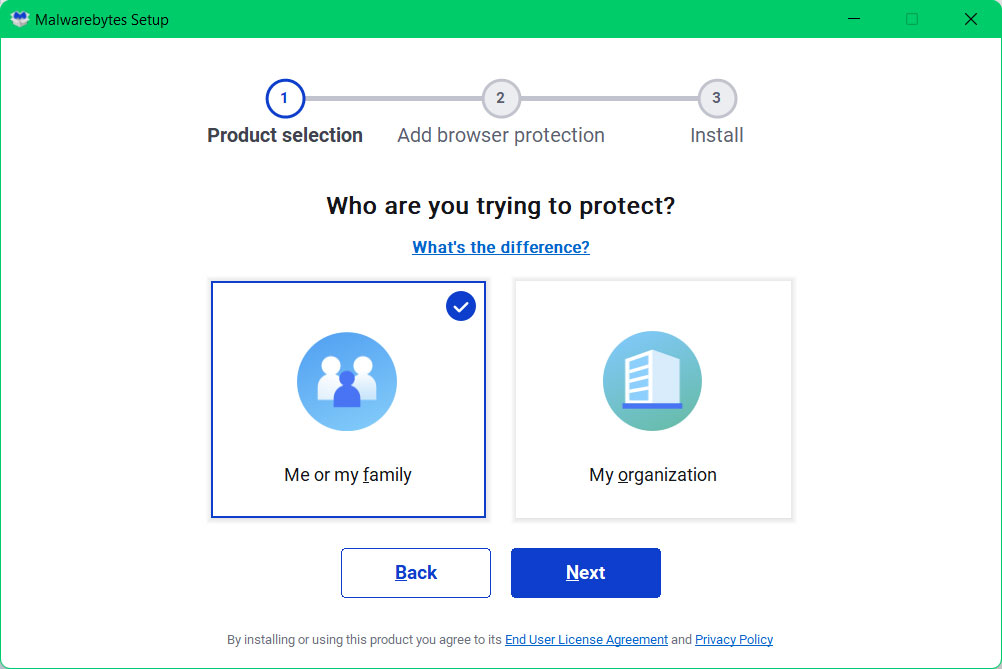
3 After following the software setup instructions, wait for the application to finish installing.

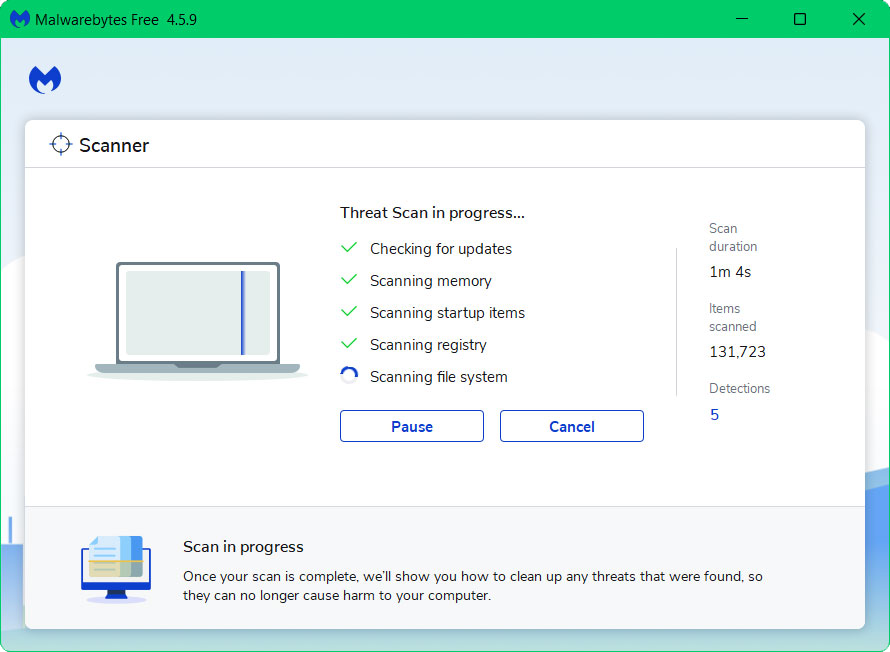
4 Once the application is installed, you may now run your first computer scan and wait for it to finish.
5 All discovered malware on the computer will be displayed on the screen, and you can eliminate them by pressing the “quarantine” button.
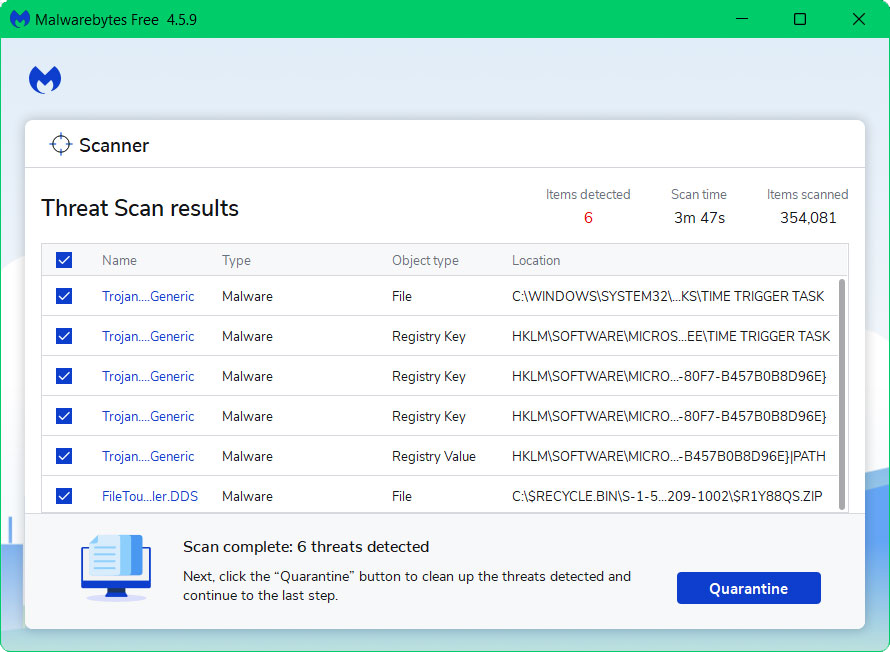
Any malware that might have been hiding on your system has been eliminated, and any modifications it may have performed have been undone. You can rest assure that your computer is free of malware after the scan.
Alternative Antivirus: Kaspersky Security Cloud Free
There are instances where a different antivirus can find something another antivirus cannot. In this situation, if the first antivirus program didn’t work, we advise doing a scan with a different one.
If you visit numerous forums and websites, you will see most users agree that Kaspersky is one of the best antivirus tool available. .

Since each antivirus application has its own threat database, Kaspersky’s detection technology may be able to find viruses that the prior program missed.
To ensure sure viruses are totally and undetectably removed from the system, we advise running a scan just in case. If you are downloading the application for the first time, you will also receive a 31-day premium trial.
1 Download the Kaspersky Security Cloud by clicking the button above.

2 Once the setup has finished downloaded, open the file and start the installation.

3 Wait until the wizard finds the latest version of the application or click Skip to install the current version stored.

4 Review the License Agreement. If you agree to its terms, click Continue.

5 Follow the installation instructions as shown then finally click install. (You may choose to uncheck the options shown if you do not want those features.)

6 Wait for the application to finish installing, then after the process is complete, click done.

7 Apply the recommended settings then start the application by clicking apply. Feel free to untick the options you do not desire.

8 You will be prompt to create an account and once you are finished, you will be redirected to the main screen. Select the Scan tab then click the run full scan and wait for it to complete. (Before scanning, we recommend you update the database to ensure any new malware variants are detected.)

After the scan has finished, the detected threats will be deleted from the computer. Reset the computer if prompted to do so.
