Minecraft mods have gained immense popularity among players of all ages, especially children, as they offer a vast array of creative and innovative features that enrich the gameplay.
These mods introduce new functionalities, unique items, captivating skins, and even custom scripts, allowing players to tailor their Minecraft experience to their liking.
However, the unfortunate reality is that malicious hackers and cybercriminals often exploit the widespread demand for Minecraft mods as an opportunity to deceive unsuspecting users, particularly kids.
They cunningly disguise their malware as enticing Minecraft mods, exploiting the trust and enthusiasm of young players.
By disguising malware as mods, these hackers seek to infiltrate the computers of unsuspecting users. Once downloaded and installed, these seemingly harmless mods can unleash a host of detrimental consequences.
Malware can compromise the security and integrity of the computer system, steal sensitive information, cause system crashes, or even grant unauthorized access to the user’s personal data.
If you believe your computer has been infected due to a malicious Minecraft mod, please follow the removal procedure below.
Remove Minecraft Mod Malware
This procedure will assist you in removing malware including in Minecraft mods. You can rest assured that the information provided below has been tried and tested.
Use Malwarebytes Anti-Malware to Remove Minecraft Mod Malware
If you believe there is a malware threat in the system, you may utilize a powerful antivirus software. Malwarebytes Anti-Malware is one of the most effective anti-malware programs available.  They have some of the greatest threat detection software, ensuring that any unwanted threats on your computer are totally eliminated. If neither of those methods work, you can utilize this antivirus program to complete the task. Furthermore, even after malware is removed from the computer, we recommend that you run a complete scan just in case.
They have some of the greatest threat detection software, ensuring that any unwanted threats on your computer are totally eliminated. If neither of those methods work, you can utilize this antivirus program to complete the task. Furthermore, even after malware is removed from the computer, we recommend that you run a complete scan just in case.
1 Visit the antivirus website or click the button above to download the most up-to-date version of the software that best suits your requirements.
2 Follow the software installation instructions until they are completed.
3 Run a complete malware scan on the machine and wait for it to finish.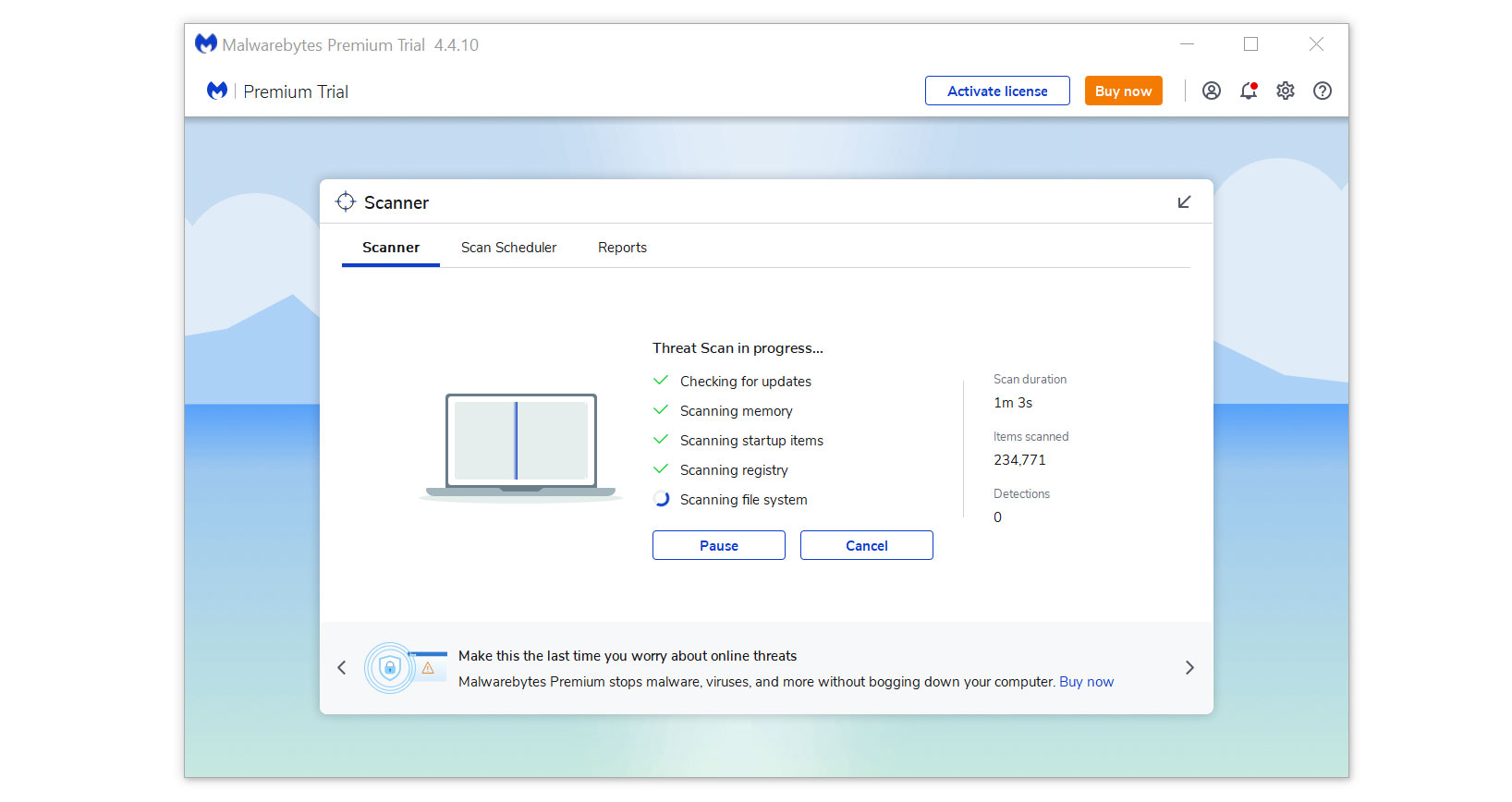
4 All the detected threats found on the computer will be shown on the screen and clicking the “quarantine” button to remove them.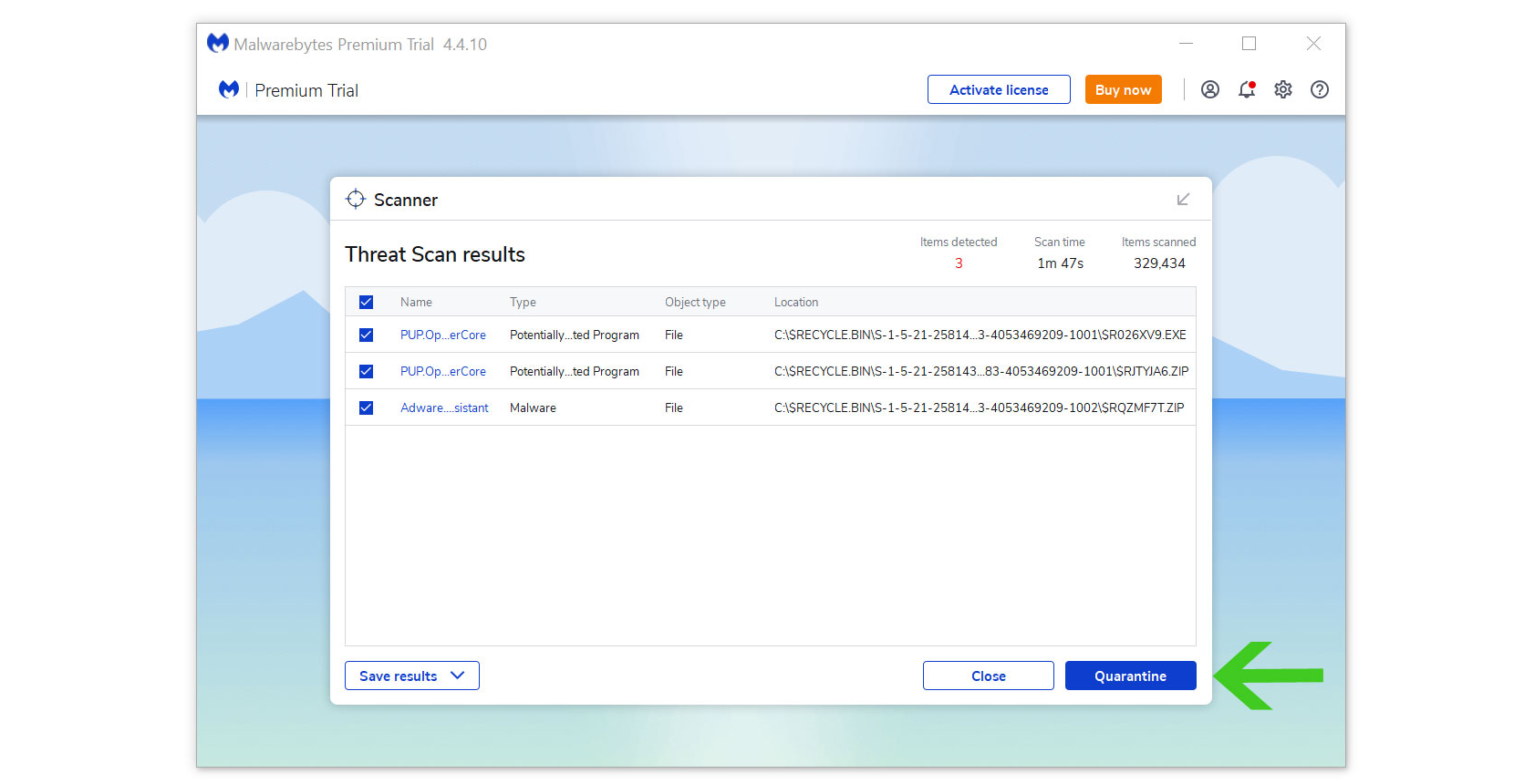
After removing the malware from the computer, you have the choice to remove the application if you want to. While doing so will disable Windows Defender Real Time Protection, following the removal of Malwarebytes, you can follow this article to reactivate it again.
Alternative: Scan with Kaspersky Antivirus for Hidden Malware
If you frequent several forums and websites, you will always see the majority of people concurring that Kaspersky is among the top antivirus programs on the market.
Even after we have removed infestations from the computer system, there is a possibility that malware is still present.

Since each antivirus application has its own threat database, Kaspersky’s detection technology may be able to find viruses that the prior program missed.
We recommend conducting a scan just in case to make sure malware and other infections are completely eliminated from the system. Additionally, if this is your first time downloading the application, you will get a 31-day premium trial.
1 Download the Kaspersky Security Cloud by clicking the button above.

2 Once the setup has finished downloaded, open the file and start the installation.

3 Wait until the wizard finds the latest version of the application or click Skip to install the current version stored.

4 Review the License Agreement. If you agree to its terms, click Continue.

5 Follow the installation instructions as shown then finally click install. (You may choose to uncheck the options shown if you do not want those features.)

6 Wait for the application to finish installing, then after the process is complete, click done.

7 Apply the recommended settings then start the application by clicking apply. Feel free to untick the options you do not desire.

8 You will be prompt to create an account and once you are finished, you will be redirected to the main screen. Select the Scan tab then click the run full scan and wait for it to complete. (Before scanning, we recommend you update the database to ensure any new malware variants are detected.)

9 After the scan has finished, the detected threats will be deleted from the computer.

Simple tips to be safe online
- Never acquire software or programs from unknown sources, as this is one of the most common ways for adware and other types of malware to attack your computer. Only download from reputable and legitimate websites. To be safe, stay away from torrent downloads and cracked software download sites, as there will always be malware in the files.
- Using a firewall is one of the most foolproof ways to be safe online. It serves as a first line of defense against dangerous websites, shielding visitors from potential risks. It protects the user’s network and device from intruders. A firewall will safeguard a user from the threats hiding on the vast internet in today’s age.
- It is essential to keep anti-virus software up to date on a computer since hundreds of new malware threats are released every day that target the machine’s vulnerabilities in order to infect it. Anti-virus updates include the most recent files required to counter new threats and safeguard your machine.
- Only visit websites that has a secured connection. A site with HTTP connection does not encrypt the data it receives and therefore is not considered secure. Entering personal information such as email addresses, phone numbers, and passwords on a website with an HTTP connection is risky since it could be compromised and your information stolen. Websites with HTTPS connections, on the other hand, are secure since data is encrypted and attackers are unlikely to gain access to information exchanged within the site.
- Backups are critical for ensuring the safety of your data. Without a thorough backup of the data, several computer dangers and irreversible damage can arise. Backing up your data is a crucial step in ensuring the safety of your information. Having a backup copy of the system and data will be extremely useful in the event of a harmful malware attack.
