What is iTop VPN?
iTop VPN is a free virtual private network program with many locations. Many have reported that this program has been suddenly getting installed into their computers, that is because iTop VPN is frequently bundled into other program’s installations.
If your computer is acting weird than usual then this application may have gotten inside your system before you know it. There are people who uses a wide range of techniques to implant their programs inside the victim’s computer.
Although this application is a legitimate VPN program and is safe to use, getting a software suddenly installed into the computer is something people may not want that is why it is often branded as a PUP (Potentially Unwanted Application).
One of the main ways of getting in to the computer is through software bundling wherein their malicious program is tagged along a legitimate software like emulators and video editors. So when the user installs the program, the adware will be injected into the system as well.
If you have iTop VPN installed in your system, you may experience lag and system overheat every time you use the computer because there may be other programs that are bundled along such as coin miners and keyloggers.
Windows PowerShell and Command Prompt may be popping up and closing every few minutes is another indication that the system has a great likely hood of malware infection. Please head over to the next section below and follow the removal guide presented to uninstall iTop VPN from the computer system.
How to remove iTop VPN
This procedure will assist you in removing iTop VPN as well as any other programs that were bundled with the potential unwanted application. You can rest assured that the information provided below has been tried and tested.
Step 1: Find and Remove Unwanted Program
Since this type of computer threat takes the appearance of an application, it’s essential to try and locate the unwanted program and remove it from the system as soon as possible to avoid further harm.
It’s worth noting that locating the program can be tricky because many programs are able to disguise as legitimate programs or system files. In that case, using an antivirus scanner will be of help to detect the threat from the computer and eliminate it.
An antivirus guide may be found below for a quick malware removal, but first here are the methods to remove the app manually.
Method 1: Remove Program via Control Panel 

- Search Control Panel in the Windows search bar then click it.
- The Control Panel should open, from there click Programs then Programs and Features.
- A list of installed software will show on the screen after a moment.
- Scroll down and find iTop VPN or any suspicious programs you did not download then right click the application and select Uninstall
Method 2: Utilizing Revo Uninstaller 
For computer users who are not sure of what to do. You may resort to using Revo Uninstaller since it is much more effective and easy to use. Revo Uninstaller is a very useful tool for Windows users.
This uninstaller not only removes programs from the computer but it also deletes their changes from the Windows Registry, Host File and etc.
- Using your browser, head over to their official website (click here) and download the latest software that is compatible with your system.
- Open the downloaded file and it should guide you through the setup.
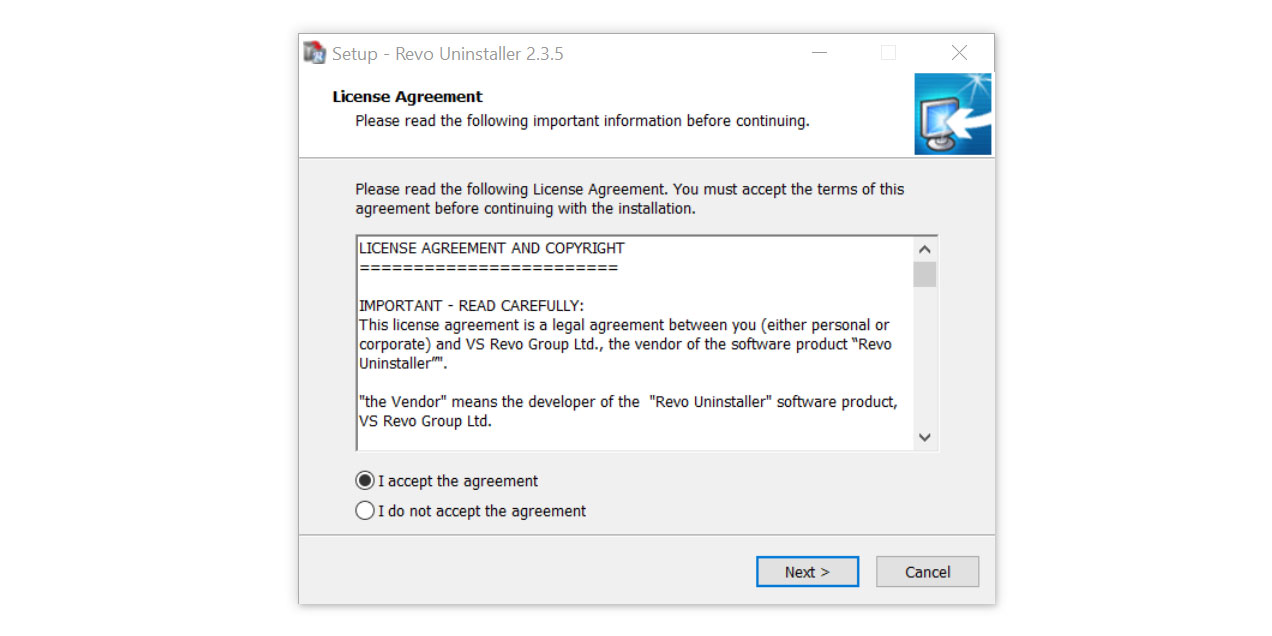
- Follow the installation procedure and wait until the installation of the software is complete.
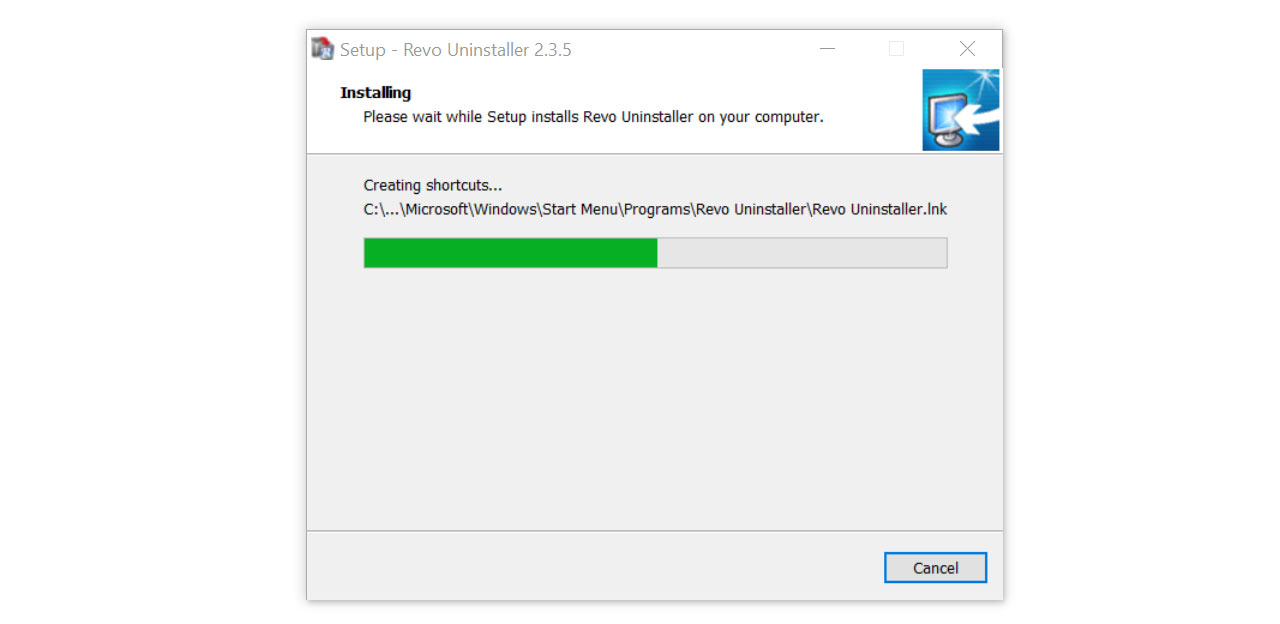
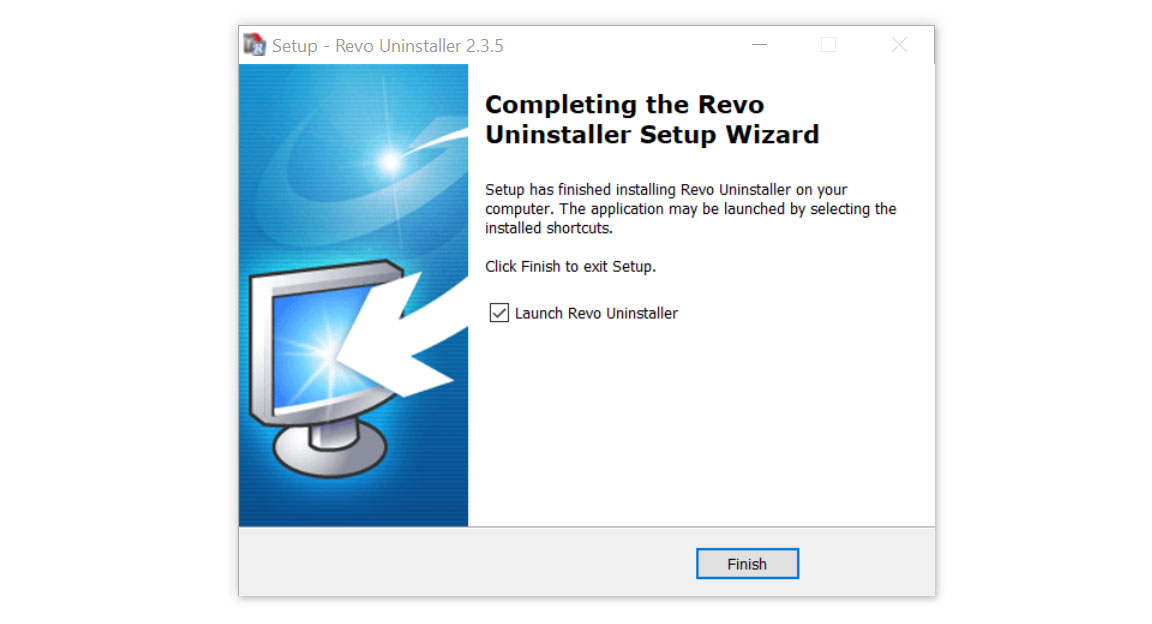
- After the installation is finished, tick the box that says Launch Revo Uninstaller then click finish.
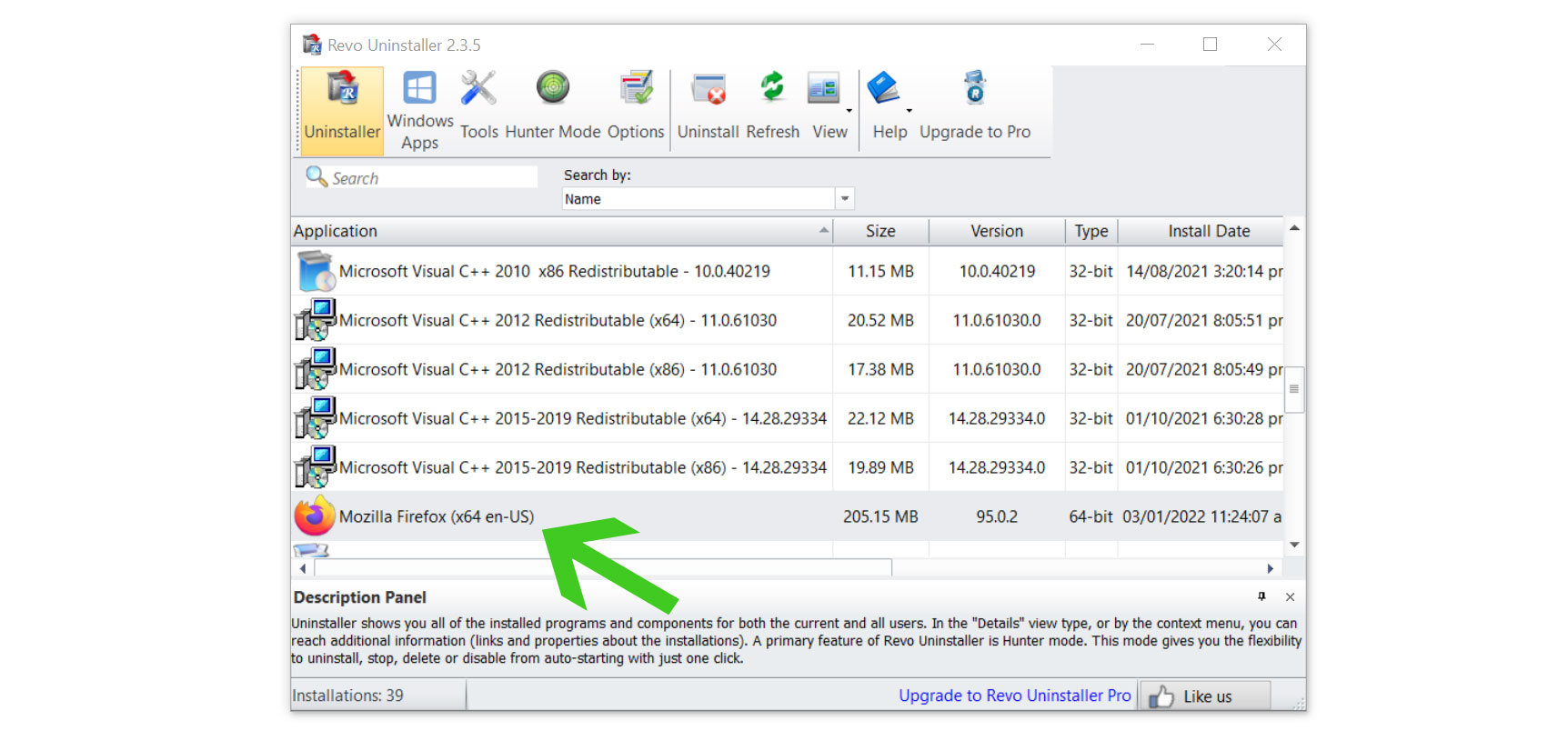
- Once the software has launched, find the unwanted application that is needed to be removed, double click the program to uninstall.
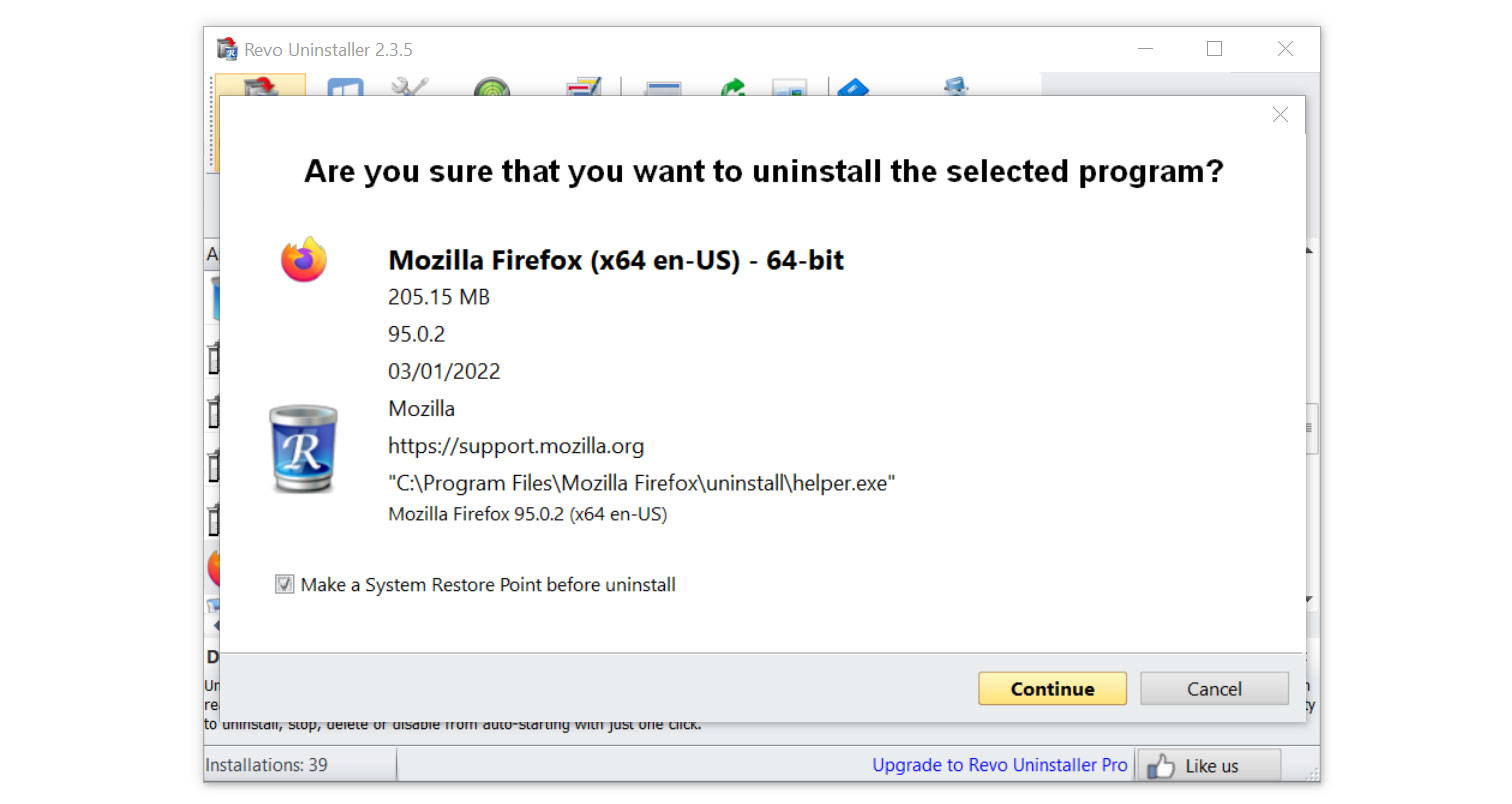
- Click on the Continue button and follow the procedure to start uninstalling the program.
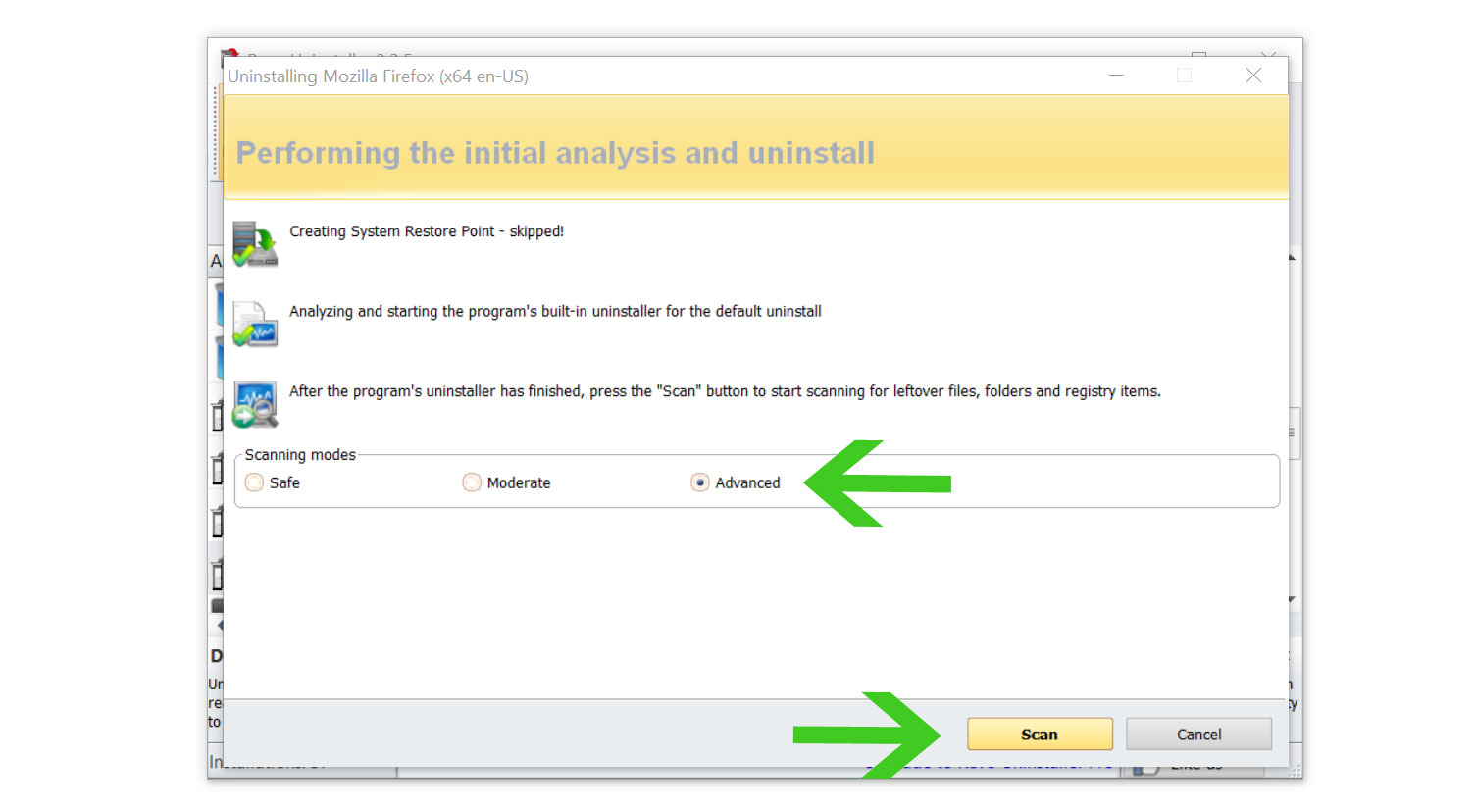
- Once it is uninstalled, a window will pop-up. Select the Advanced option for the scanning mode then click Scan to find remnants of iTop VPN.
- A window will pop-up and show all of the leftovers and changes made by the program uninstalled a while ago.
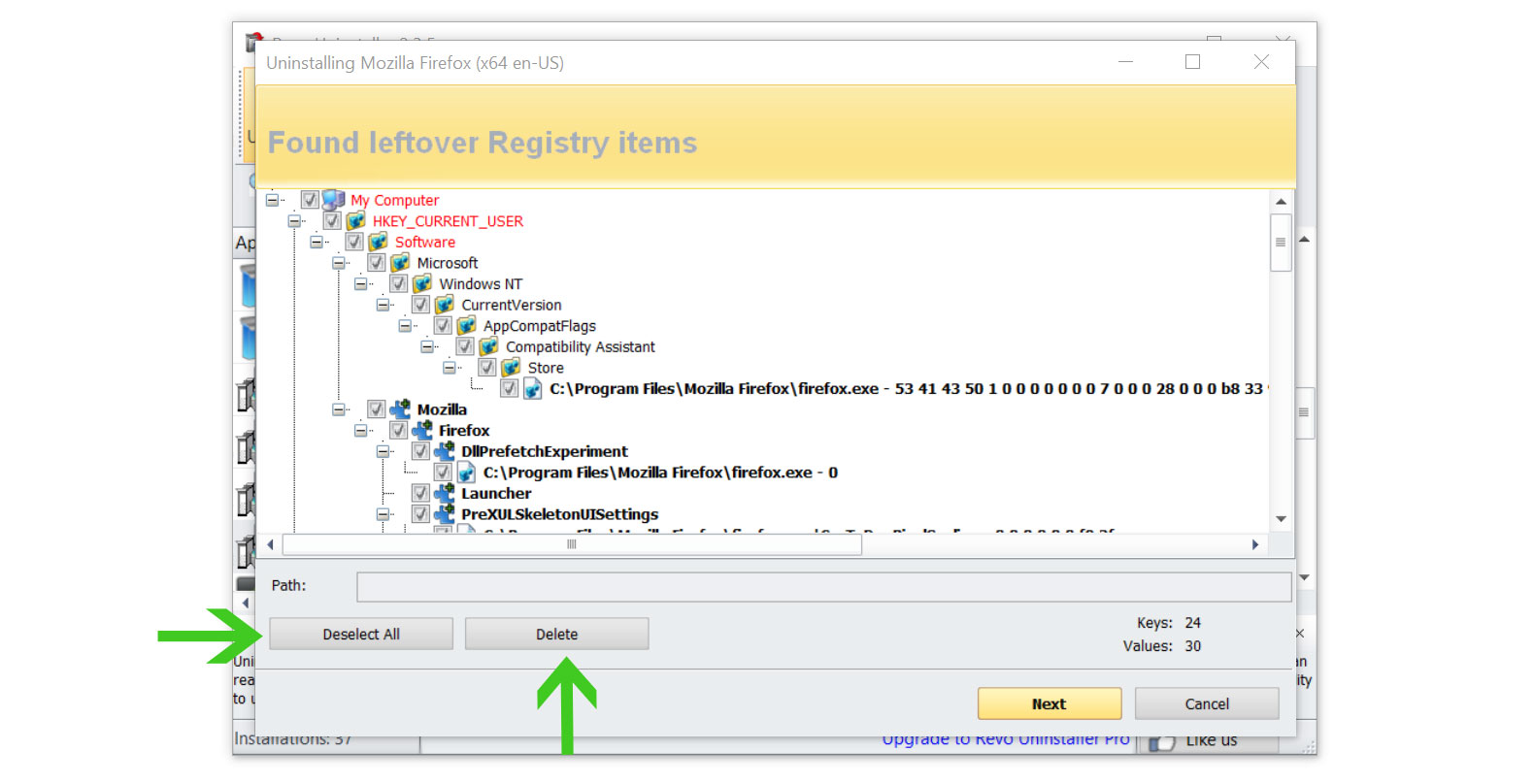
- Click the Select All button and hit Delete to remove the leftovers found on the Windows Registry.
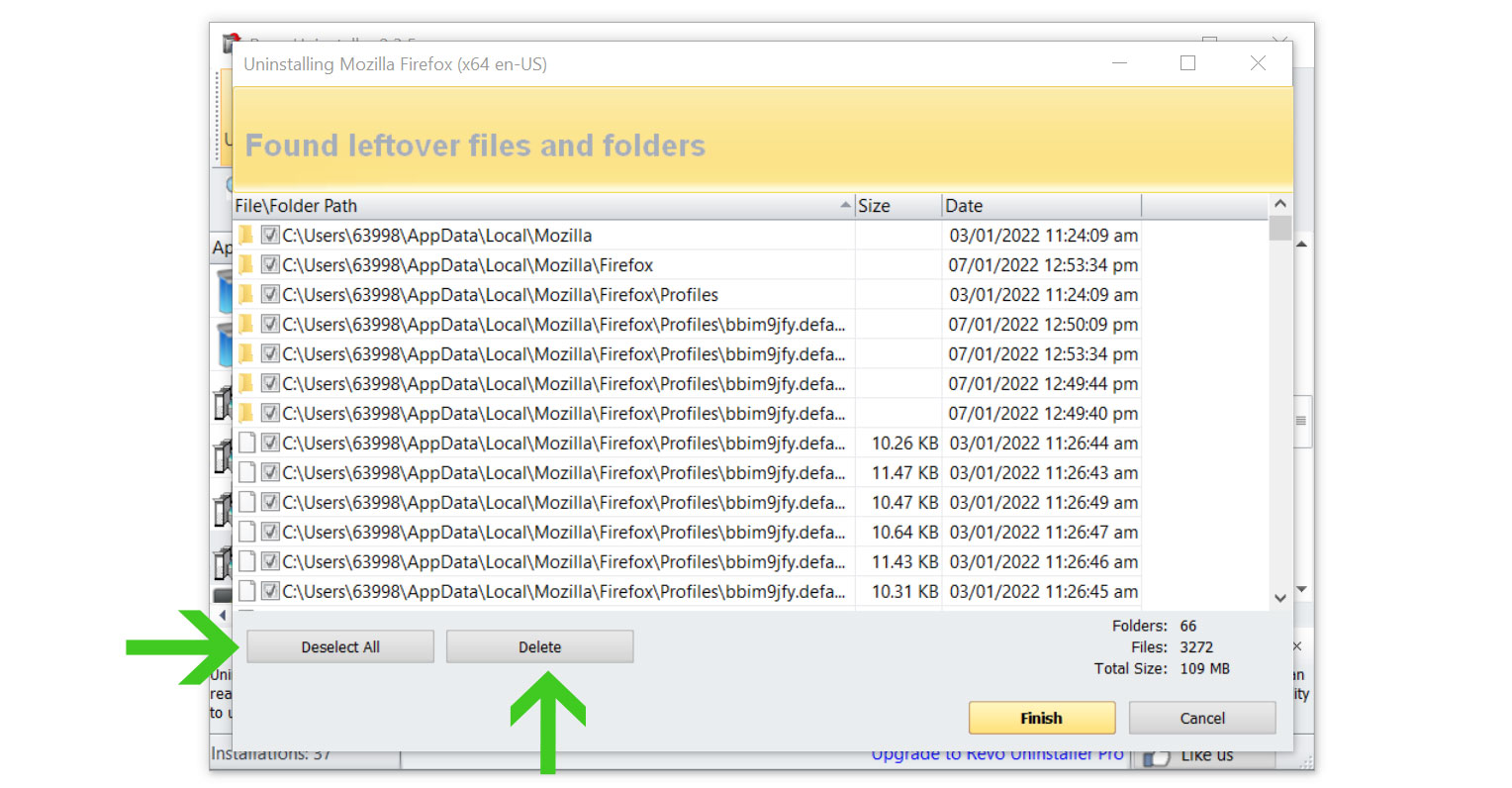
- Some leftover files may be found, click Select All then Delete them as well.
Once the window closes, you have successfully removed iTop VPN threat from your system.
Simple tips to be safe online
- Never acquire software or programs from unknown sources, as this is one of the most common ways for adware and other types of malware to attack your computer. Only download from reputable and legitimate websites. To be safe, stay away from torrent downloads and cracked software download sites, as there will always be malware in the files.
- Using a firewall is one of the most foolproof ways to be safe online. It serves as a first line of defense against dangerous websites, shielding visitors from potential risks. It protects the user’s network and device from intruders. A firewall will safeguard a user from the threats hiding on the vast internet in today’s age.
- It is essential to keep anti-virus software up to date on a computer since hundreds of new malware threats are released every day that target the machine’s vulnerabilities in order to infect it. Anti-virus updates include the most recent files required to counter new threats and safeguard your machine.
- Only visit websites that has a secured connection. A site with HTTP connection does not encrypt the data it receives and therefore is not considered secure. Entering personal information such as email addresses, phone numbers, and passwords on a website with an HTTP connection is risky since it could be compromised and your information stolen. Websites with HTTPS connections, on the other hand, are secure since data is encrypted and attackers are unlikely to gain access to information exchanged within the site.
- Backups are critical for ensuring the safety of your data. Without a thorough backup of the data, several computer dangers and irreversible damage can arise. Backing up your data is a crucial step in ensuring the safety of your information. Having a backup copy of the system and data will be extremely useful in the event of a harmful malware attack.
