When you navigate to the Control Panel or the list of installed Windows applications, you might come across an unexpected sight—a mysterious default program icon with no name.
To make matters more perplexing, this enigmatic entry may display an astonishing file size of 0KB or even reach extremes like 1TB, despite the fact that your computer lacks such vast storage capacity.
It’s crucial to recognize that these unfamiliar applications are highly likely to be malicious in nature, designed with nefarious intentions for your computer.
However, it’s worth noting that there is a slim chance these appearances are caused by system bugs or legitimate programs gone awry.
More Details About The Nameless Programs
Regardless of their origins, it is crucial to acknowledge that these applications are not to be trusted, and immediate removal is the recommended course of action to safeguard your system from potential malicious activities.
These unidentifiable programs can pose significant risks to the security and stability of your computer. By their very nature, they raise suspicions and suggest the presence of malware, spyware, or other forms of malicious software.
They may attempt to exploit vulnerabilities, steal sensitive information, or disrupt the normal functioning of your system. Ignoring these mysterious applications can expose your computer to a range of potential dangers, including identity theft, data loss, and unauthorized access to your personal files.
To protect your system and maintain a secure computing environment, it is crucial to take swift action when encountering these unknown programs. The methods below will help you remove the mysterious nameless application from the computer.
Uninstall Unknown Nameless Application
Our team has attempted and tested each of the techniques listed below because this issue may have numerous primary causes. Try the following one if the first doesn’t work for you until the issue is resolved.
Step 1: Use Malwarebytes Anti-Malware
Using an antivirus software will be the easiest method in order to remove the nameless program from the system. Malwarebytes Anti-Malware is one of the most effective anti-malware programs available.  They have some of the greatest threat detection software, ensuring that any unwanted threats on your computer are totally eliminated.
They have some of the greatest threat detection software, ensuring that any unwanted threats on your computer are totally eliminated.
If neither of those methods work, you can utilize this antivirus program to complete the task. Furthermore, even if the nameless program is completely removed from the computer, we recommend that you run a complete scan just in case.
- Visit the antivirus website or click the button above to download the most up-to-date version of the software that best suits your requirements.
- Follow the software installation instructions until they are completed.
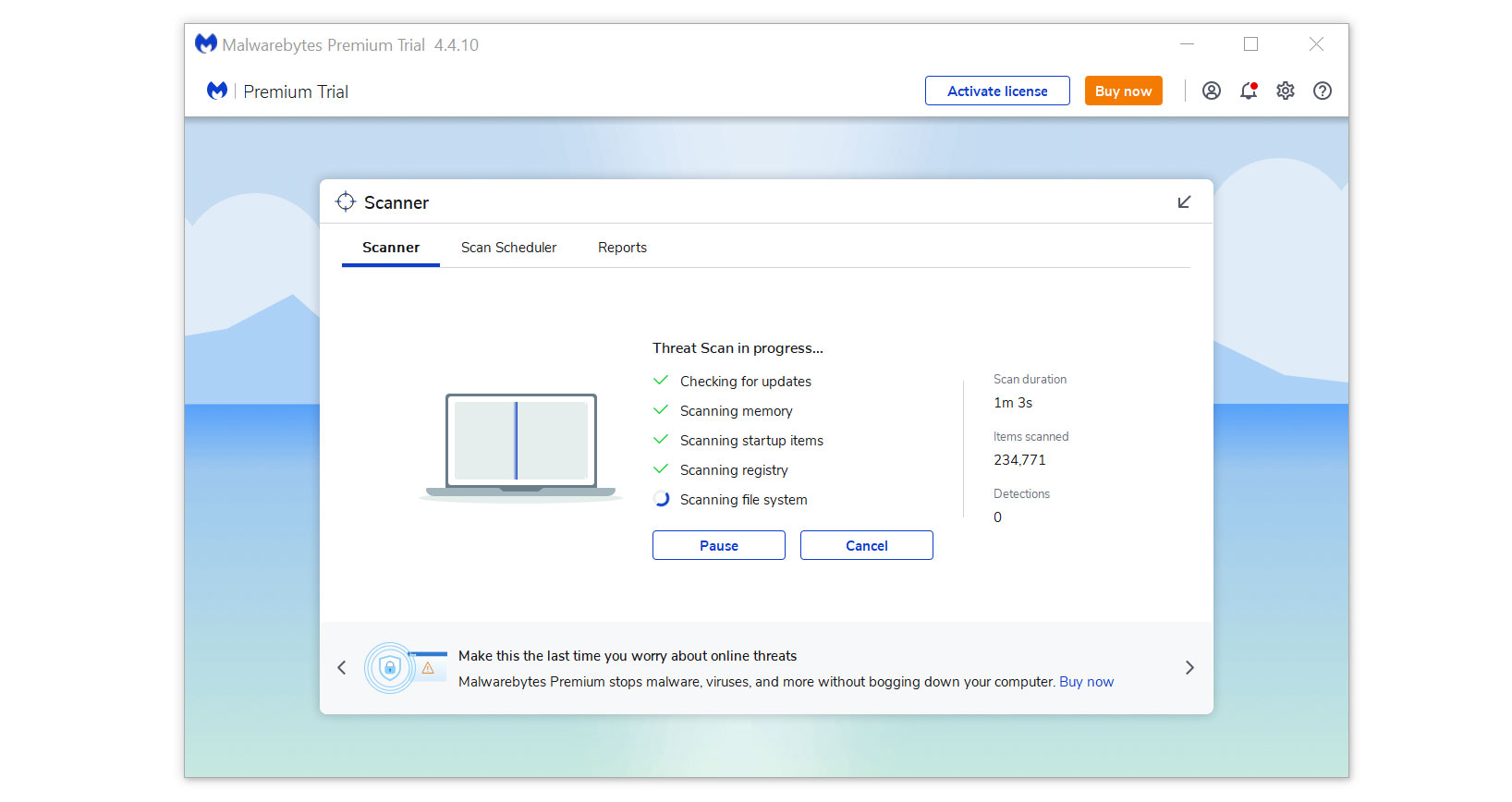
- Run a complete malware scan on the machine and wait for it to finish.
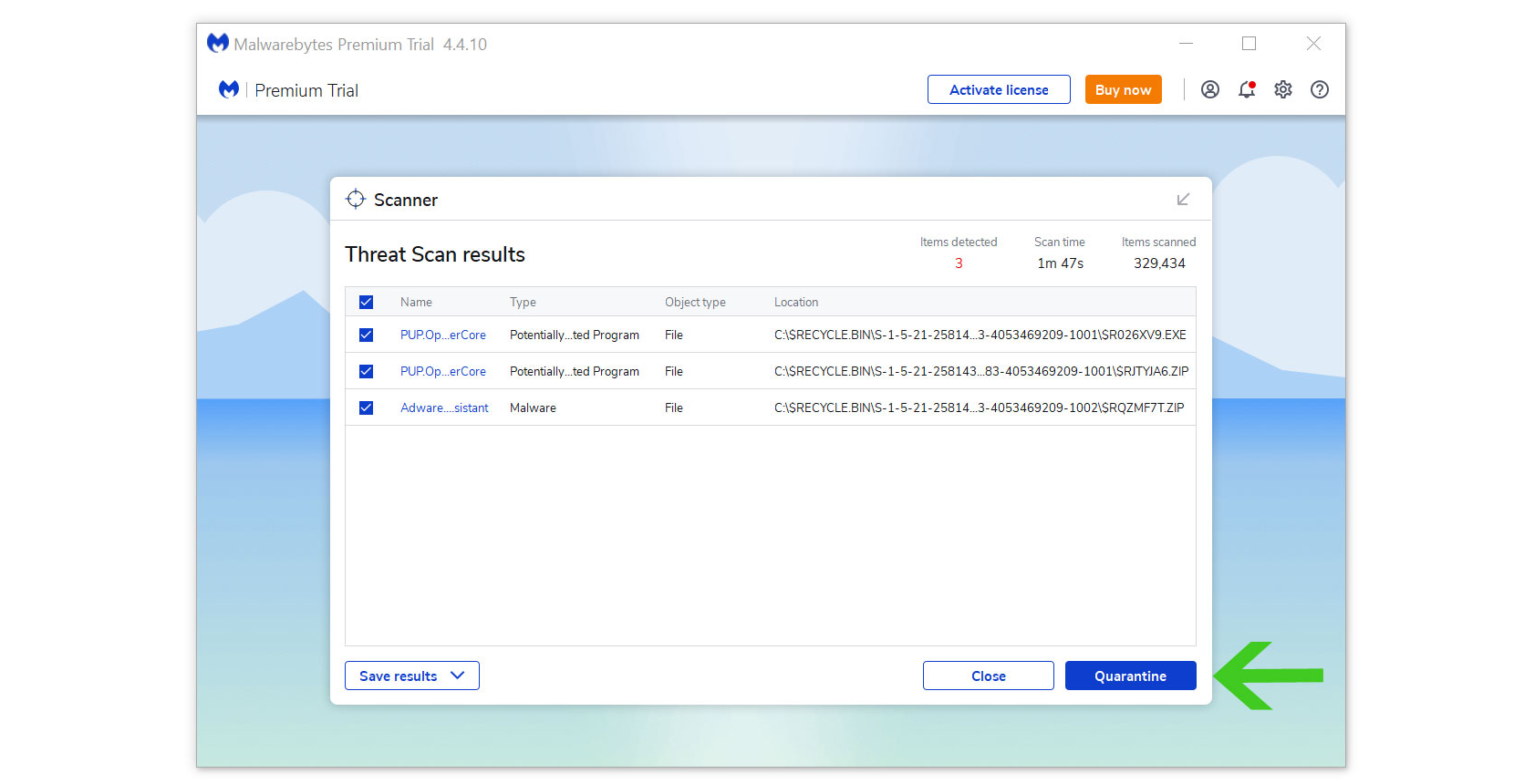
- All the detected threats found on the computer will be shown on the screen and clicking the “quarantine” button to remove them.
After removing the malware from the computer, you have the choice to remove the application if you want to. While doing so will disable Windows Defender Real Time Protection, following the removal of Malwarebytes, you can follow this article to reactivate it again.
Step 2: Find and Remove Unwanted Program
Since this type of computer threat takes the appearance of an application, it is essential to try and locate the source of the program and remove it from the system as soon as possible to avoid further harm.
It is worth noting that locating the program can be tricky because many malicious programs disguise as legitimate programs or system files.
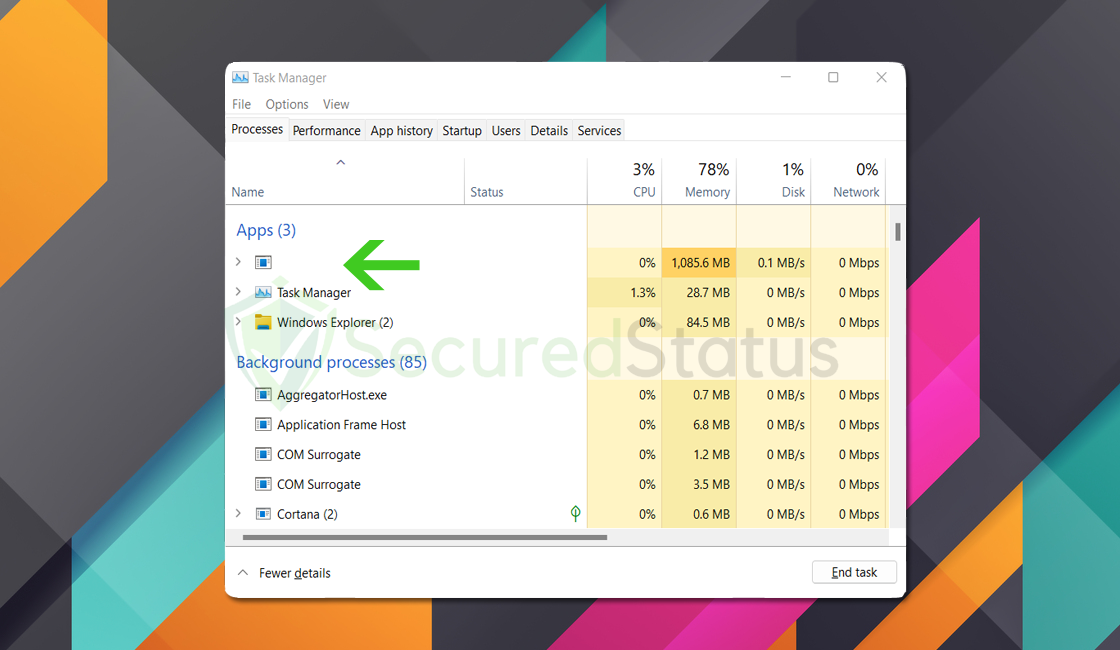
You may locate the program by utilizing the Task Manager and finding suspicious applications that are currently running when you are facing the browser hijacker symptoms.
Remove Program via Control Panel

- Search Control Panel in the Windows search bar then click it.
- The Control Panel should open, from there click Programs then Programs and Features.
- A list of installed software will show on the screen after a moment.
- Scroll down and find the nameless application then right click the application and select Uninstall.
Utilize Revo Uninstaller
For computer users who are not sure of what to do. You may resort to using Revo Uninstaller since it is much more effective and easy to use. Revo Uninstaller is a very useful tool for Windows users.
This uninstaller not only removes programs from the computer but it also deletes their changes from the Windows Registry, Host File and etc.
- Click the button above and download the latest software that is compatible with your system.
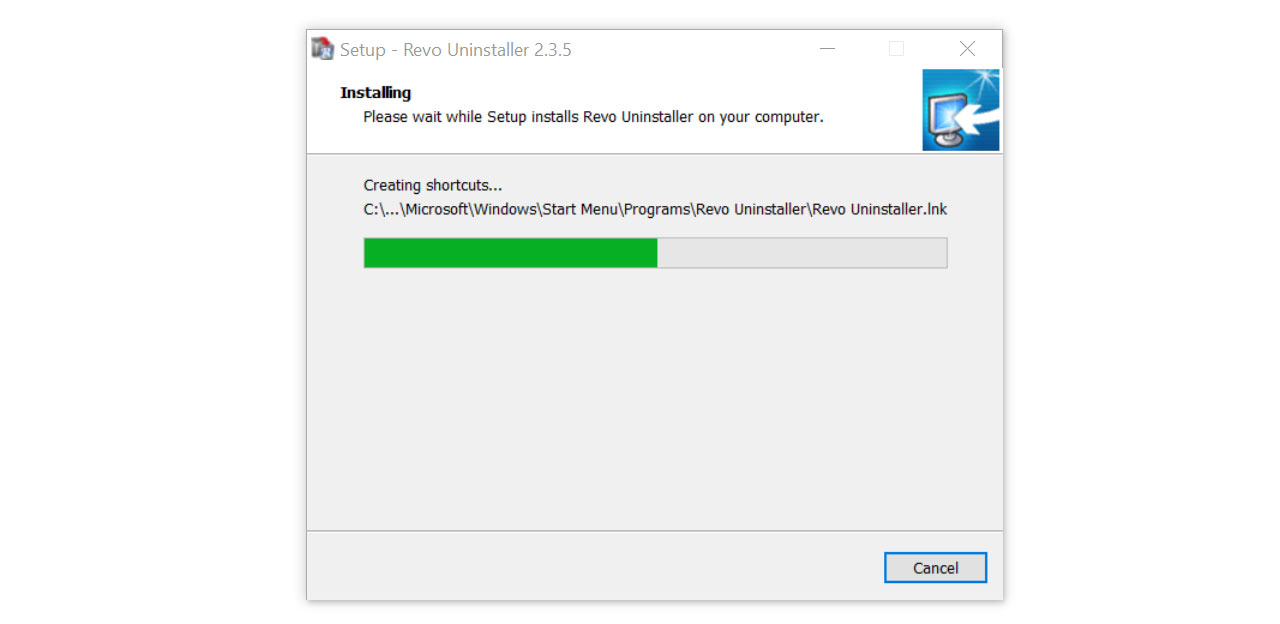
- Open the downloaded file and it should guide you through the setup.
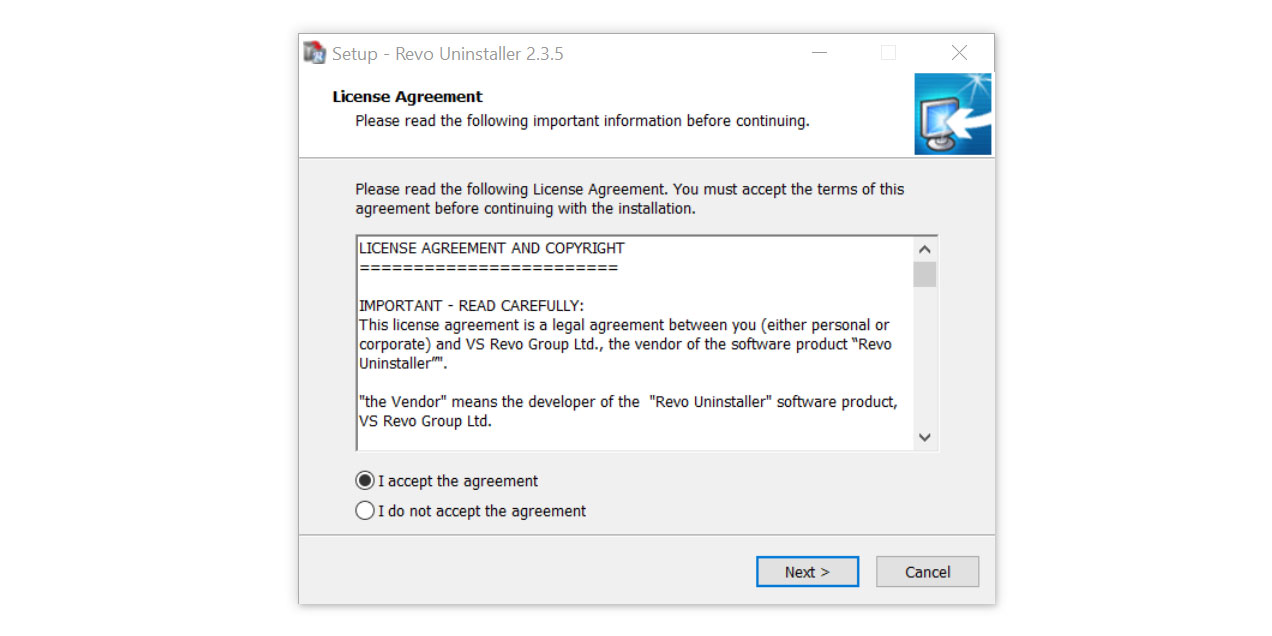
- Follow the installation procedure and wait until the installation of the software is complete.
- After the installation is finished, tick the box that says Launch Revo Uninstaller then click finish.
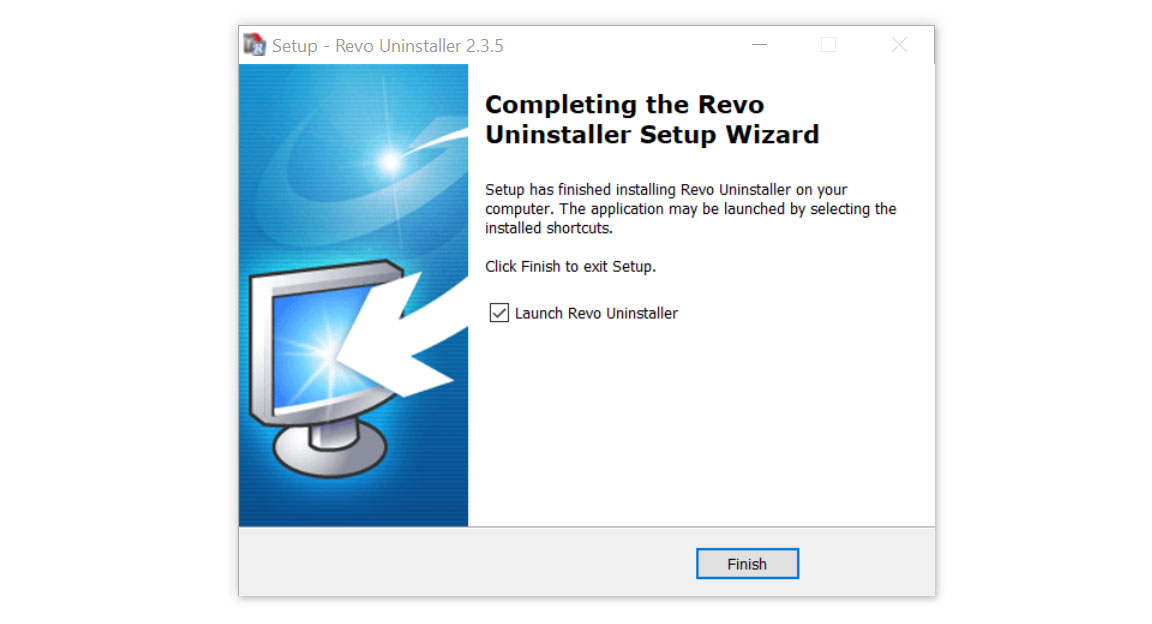
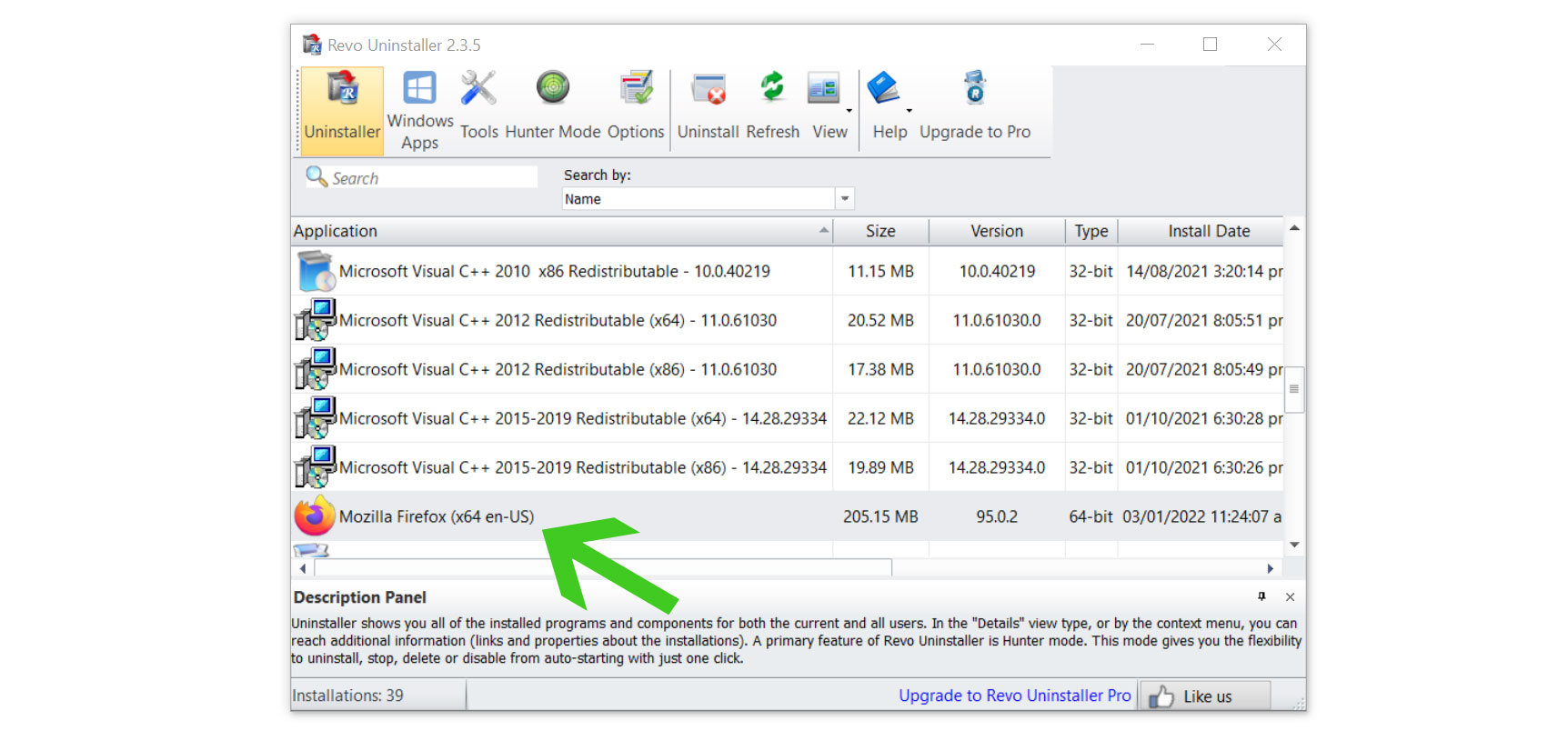
- Once the software has launched, find the unwanted application that is needed to be removed, double click the program to uninstall.
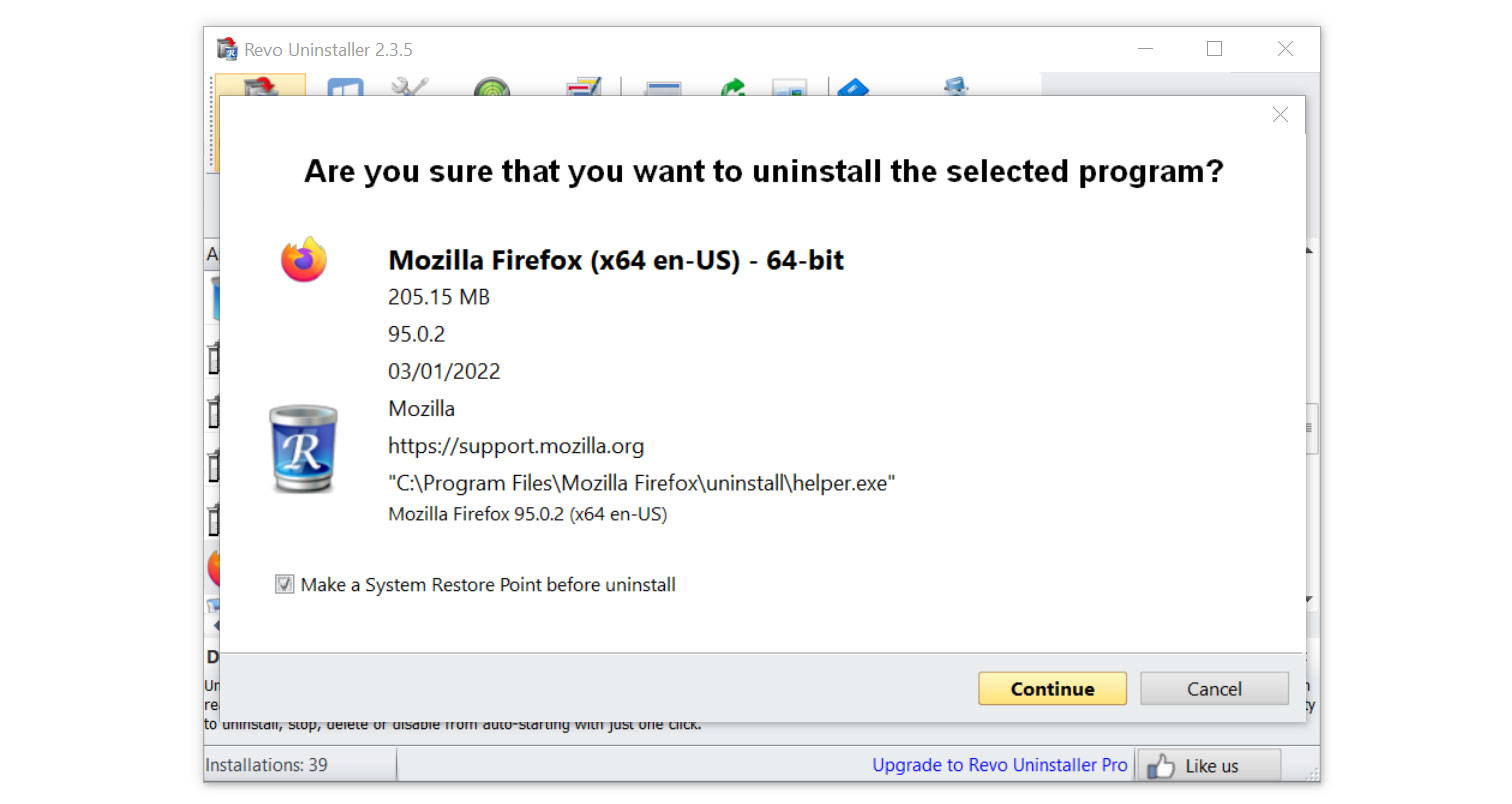
- Click on the Continue button and follow the procedure to start uninstalling the program.
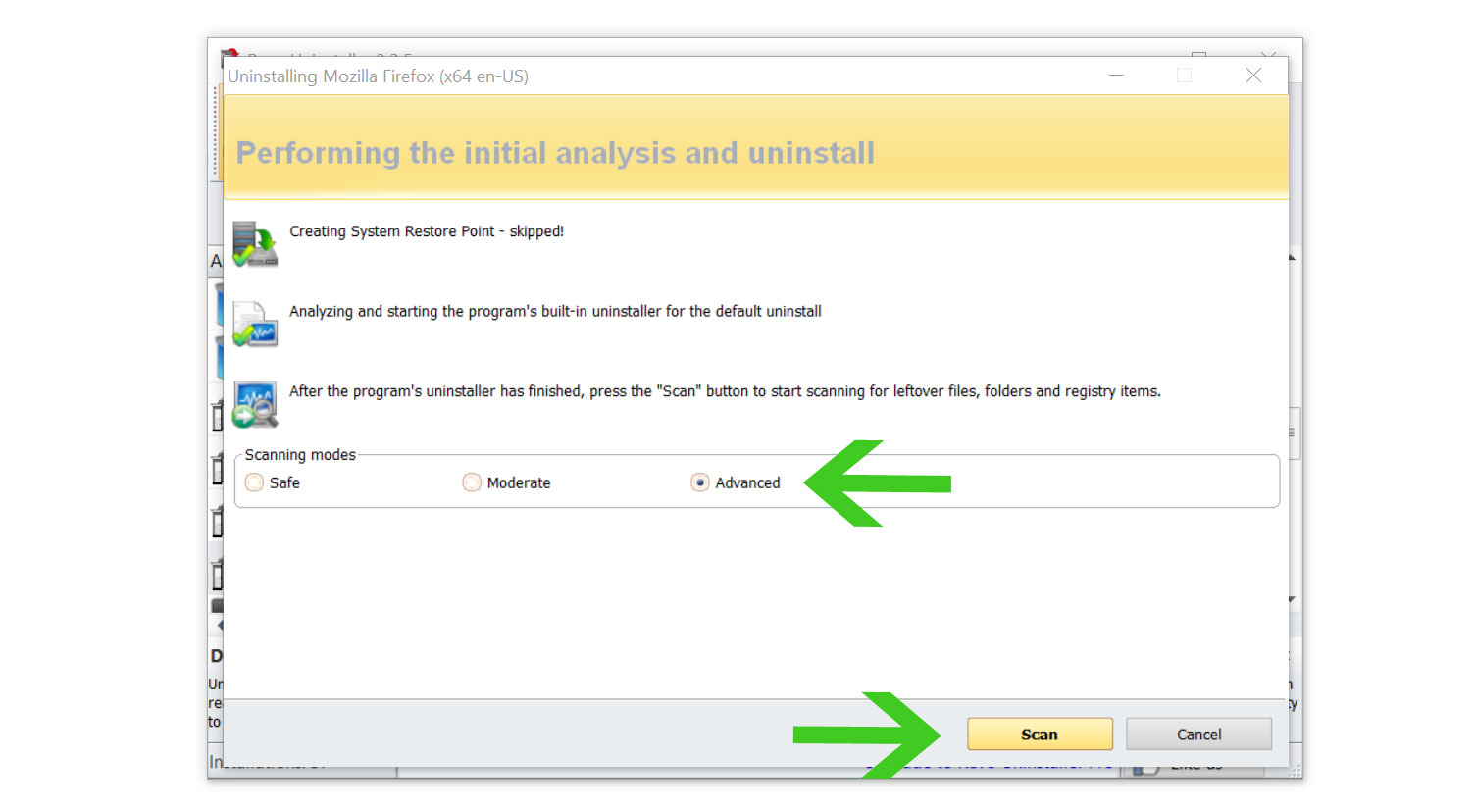
- Once it is uninstalled, a window will pop-up. Select the Advanced option for the scanning mode then click Scan to find remnants of the nameless applications.
- A window will pop-up and show all of the leftovers and changes made by the program uninstalled a while ago.
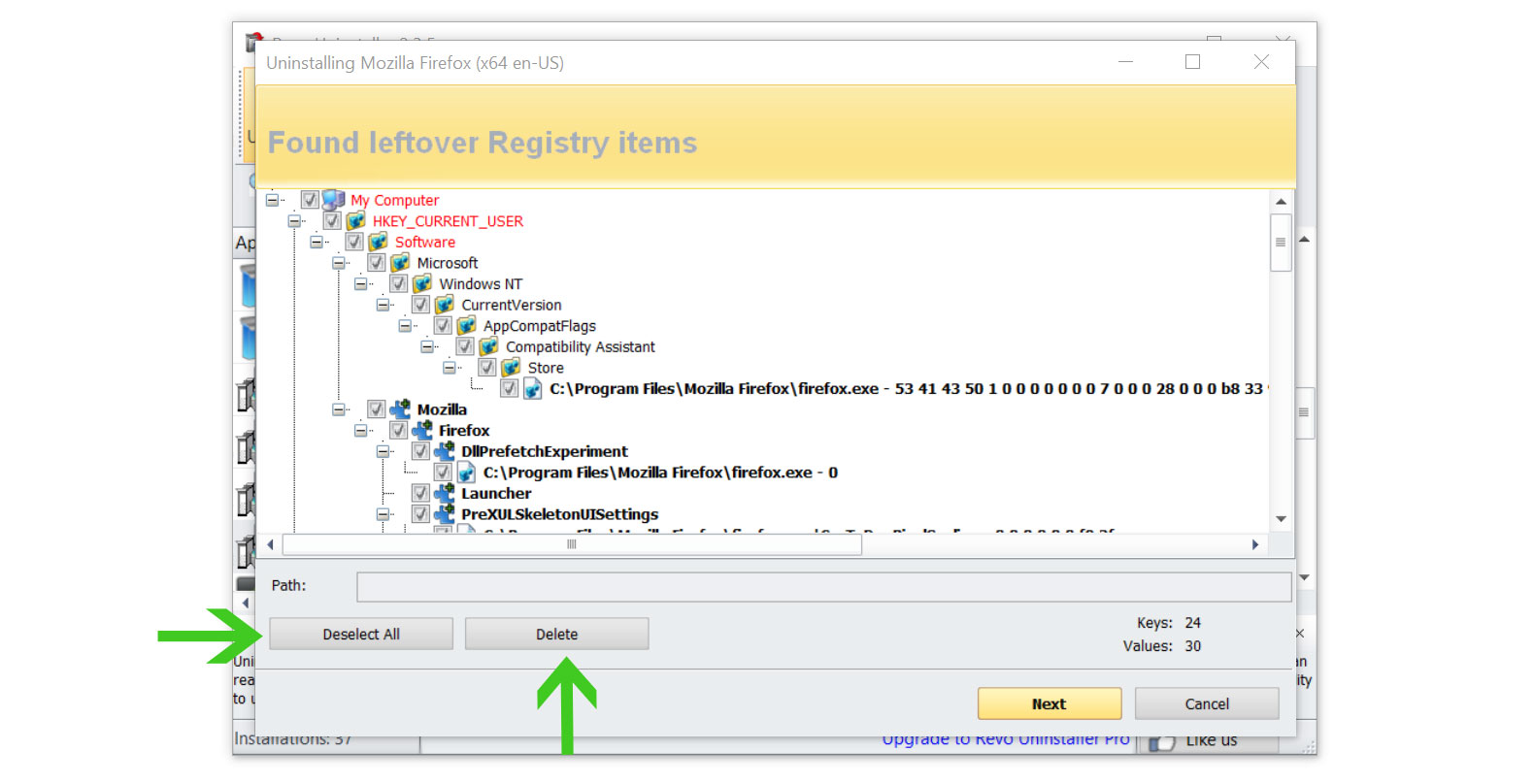
- Click the Select All button and hit Delete to remove the leftovers found on the Windows Registry.
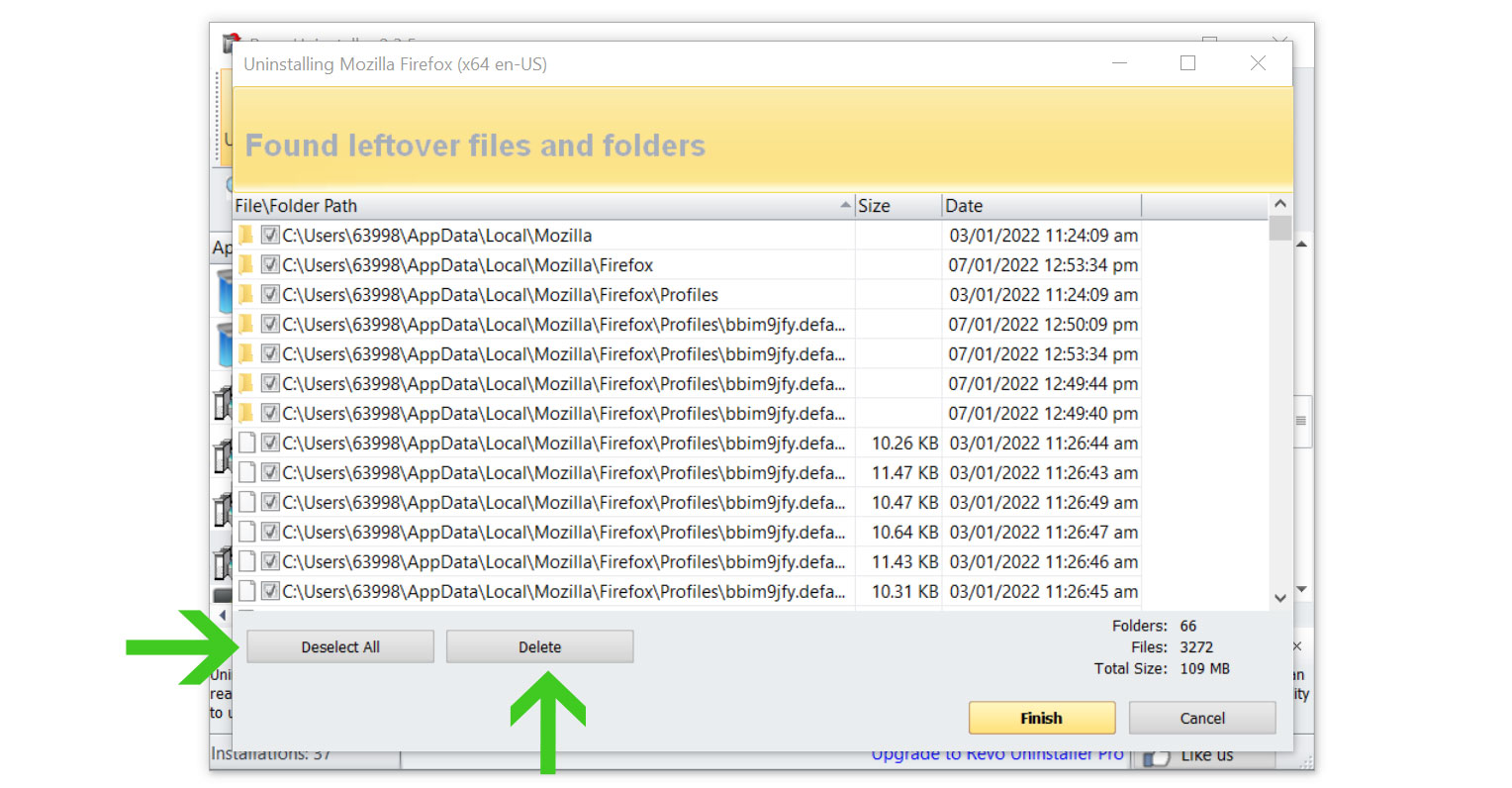
- Some leftover files may be found, click Select All then Delete them as well.
- Once the window closes, you have successfully removed the adware threat from your system.
Step 4: Run a Second Opinion Scan with Kaspersky Antivirus
If you frequent several forums and websites, you will always see the majority of people concurring that Kaspersky is among the top antivirus programs on the market.
Even after we have removed infestations from the computer system, there is a possibility that malware is still present so it is best to scan once more.

Since each antivirus application has its own threat database, Kaspersky’s detection technology may be able to find viruses that the prior program missed.
We recommend conducting a scan just in case to make sure the nameless malware program and other infections are completely and undetectably eliminated from the system. Additionally, if this is your first time downloading the application, you will get a 31-day premium trial.
1. Download the Kaspersky Security Cloud by clicking the button above.

2. Once the setup has finished downloaded, open the file and start the installation.

3. Wait until the wizard finds the latest version of the application or click Skip to install the current version stored.

4. Review the License Agreement. If you agree to its terms, click Continue.

5. Follow the installation instructions as shown then finally click install. (You may choose to uncheck the options shown if you do not want those features.)

6. Wait for the application to finish installing, then after the process is complete, click done.

7. Apply the recommended settings then start the application by clicking apply. Feel free to untick the options you do not desire.

8. You will be prompt to create an account and once you are finished, you will be redirected to the main screen. Select the Scan tab then click the run full scan and wait for it to complete.(Before scanning, we recommend you update the database to ensure any new malware variants are detected.)

9. After the scan has finished, the detected threats will be deleted from the computer.

Simple tips to be safe online
- Never acquire software or programs from unknown sources, as this is one of the most common ways for adware and other types of malware to attack your computer. Only download from reputable and legitimate websites. To be safe, stay away from torrent downloads and cracked software download sites, as there will always be malware in the files.
- Using a firewall is one of the most foolproof ways to be safe online. It serves as a first line of defense against dangerous websites, shielding visitors from potential risks. It protects the user’s network and device from intruders. A firewall will safeguard a user from the threats hiding on the vast internet in today’s age.
- It is essential to keep anti-virus software up to date on a computer since hundreds of new malware threats are released every day that target the machine’s vulnerabilities in order to infect it. Anti-virus updates include the most recent files required to counter new threats and safeguard your machine.
- Only visit websites that has a secured connection. A site with HTTP connection does not encrypt the data it receives and therefore is not considered secure. Entering personal information such as email addresses, phone numbers, and passwords on a website with an HTTP connection is risky since it could be compromised and your information stolen. Websites with HTTPS connections, on the other hand, are secure since data is encrypted and attackers are unlikely to gain access to information exchanged within the site.
- Backups are critical for ensuring the safety of your data. Without a thorough backup of the data, several computer dangers and irreversible damage can arise. Backing up your data is a crucial step in ensuring the safety of your information. Having a backup copy of the system and data will be extremely useful in the event of a harmful malware attack.
